SaaS Management vs IT Asset Management in 2026
Hardware lifecycles live in the CMDB. Cloud apps appear after someone swipes a card. Finance tracks both costs but sees only one control gap. Decision makers debate whether to expand IT Asset Management, adopt SaaS Management, or run both. Choose poorly, and you inherit blind spots, audit headaches, and wasted cash.
This guide sorts it out by lining up scope, metrics, discovery tactics, and integration paths for ITAM and SaaS Management. We cover hardware disposal rules, data residency clauses, depreciation timelines, renewal savings, scanners, API logs, and measurable results. A checklist then maps environment size, buying habits, and compliance pressure to a practical mix.
Use it to match the right control layer to your tech stack without extra effort or spend.
Table of Contents
- Where ITAM ends and SaaS begins
- Shared goals, different scoreboards
- Discovery tools and where they meet
- Choosing ITAM, SaaS, or both
- Lessons from companies in the wild
- Conclusion
- Audit your company's SaaS usage today
Where ITAM ends and SaaS begins
IT Asset Management (ITAM) lives on the factory floor, in the server room, and at the loading dock. SaaS Management sits in a browser tab and shows up on the credit-card statement. Both track tech, but each watches a different layer of the stack.
ITAM treats every physical or perpetual item as an asset with a beginning and an end. The clock starts when the purchase order clears, runs through depreciation, and stops when the device is recycled or the license retires. Asset tags, RFID stickers, and CMDB entries tie the record to a desk, a rack, or a field technician. Local e-waste rules or GDPR-driven drive-shredding requests often spark a policy review.
SaaS Management enters later. A marketing lead swipes a card for a Figma seat, and the life cycle kicks off, no box to scan, no firmware to patch. What matters is the subscription ID, user count, data region, and renewal date. Visibility tools pull from SSO logs, finance systems, or browser extensions to surface shadow IT that sneaks past the help desk. Data-residency clauses, SOC 2 controls, and shared-responsibility models guide its governance, not a disposal certificate.
The gap between the two practices widened once cloud apps slipped out of centralized buying. Traditional discovery tools missed browser-based work, so finance saw spend while IT saw nothing. SaaS Management stepped in to cover that blind spot.
- ITAM asset examples
- Laptops, servers, mobile phones
- Perpetual database licenses
- Network switches and UPS units
- SaaS Management asset examples
- Salesforce production and sandbox orgs
- Slack guest accounts
These scopes overlap at the contract level. A Microsoft Enterprise Agreement might bundle Office 365 subscriptions with Surface devices. The hardware line rolls into ITAM, while the cloud seats land in the SaaS register. Clear taxonomy prevents double counting and overlooked risks. Build it once, map both life cycles, and each team keeps its view without losing the full picture.

Shared goals, different scoreboards
Cost, risk, and visibility drive both IT Asset Management and SaaS Management, but each field keeps its own report card. When you add up the results without context, priorities blur and budgets stall.
ITAM grew up in accounting. Finance wants proof a laptop lasts four years and that a router’s warranty still stands. Ops wants shorter repair cycles so desks stay productive. These needs shape the metrics. SaaS owners sit closer to procurement and security. They track logins, idle seats, and looming renewals. One group measures hardware wear; the other monitors subscription creep. Combine the data without explaining the difference and teams pull the wrong levers.
Key measures that seldom overlap:
- IT Asset Management
- Depreciation schedule accuracy
- Mean time to repair (MTTR)
- Warranty claim recovery rate
- Audit variance on hardware counts
- SaaS Management
- Cost per active user
- Renewal savings versus list price
- Dormant seat ratio
- Login frequency trend
Both sets still feed governance. ISO 19770 flags how to tag and track hardware. SOC 2 mapping demands evidence on SaaS access and data retention. Align the controls and you reduce audit prep by pulling from one evidence locker rather than two.
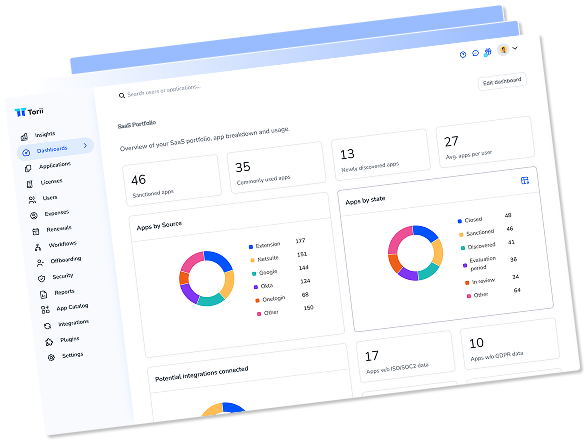
A shared report surfaces duplicate spend across the environment. A new hire may receive a licensed desktop app already bundled inside the company’s cloud suite. One dashboard in ServiceNow or Torii can call out the overlap, but the fix varies. ITAM cancels the shrink-wrap contract at the next true-up. SaaS leads right-size seats or migrate teams into one tenant.
Pick KPIs that match today’s pinch point. If warranty churn hurts uptime, start with MTTR. If surprise renewals hit cash flow, track dormant seat ratio. Clear ownership, shared data, and distinct scorecards deliver the quickest wins.

Discovery tools and where they meet
Discovery fuels every inventory.
IT Asset Management tools run close to the metal; SaaS Management hangs out in the browser or the identity stack. An agent on a laptop grabs BIOS version, patch level, and location tag, then sends it to a CMDB such as ServiceNow. A browser plug-in from Torii reads URL calls, OAuth scopes, and seat counts. Same goal, different sensors.
On the hardware side, subnet scanners flag every MAC address, barcode guns refresh stock rooms, and RFID gates timestamp each move. Switch ports list make, model, and firmware so auditors can spot end-of-support fast. Cloud apps surface through SSO logs from Okta or vendor invoices pulled by API. Gartner notes that 30 percent of discovered SaaS apps never go through procurement, a blind spot for classic ITAM crawlers.
Data shape dictates audit prep. A serial number traces to one device; an OAuth token traces to a user session. Blend those streams without context and the CMDB turns noisy. Seasoned teams push both feeds into a lake, let a rules engine bind user IDs to asset IDs, and close the loop. Lost laptop, account disabled, risk wrapped in a single ticket.
Skipped integrations drain savings. Without an RFID feed, a server can walk out the door. Without an API key, a duplicate Slack workspace renews for another year. Forrester puts that shadow cost at 10-20 percent of tech spend.
Watch for these factors when picking platforms:
- Discovery depth: firmware, geotag, OAuth scope, feature use
- Refresh rate: real-time, daily, batch
- Credential handoff: key vault, OAuth, service account
- Scale ceiling: 10,000 devices, 1,000 apps, or both
- Reporting joins: CMDB, ITSM, finance ERP
Pick the mix that matches your audit window and team size. A tool that nails discovery yet stalls on export will burn hours in spreadsheets.

Choosing ITAM, SaaS, or both
Pick the wrong tool and both budget and risk spike. Start with scope, then run a quick check to find the mix that fits.
- Headcount under 300, cloud-only stack, no outside audits. A focused SaaS management platform such as Torii removes duplicate seats and surfaces renewal dates in hours instead of weeks. Budget for a part-time admin and one security reviewer. Skip full ITAM until hardware appears on the balance sheet.
- 300-2,000 staff, mixed cloud and on-prem, regional data laws. Adopt SaaS management now and grow an existing CMDB in ServiceNow or Jira Assets when funds allow. Sequence the work: inventory SaaS first to spot looming renewals, then barcode critical servers, then fold both data sets into the help desk flow. Plan one dedicated asset analyst and shared finance support.
- 2,000+ workers, multiple business units, active M&A. A hybrid program returns value quickest. Layer API-driven SaaS discovery on top of a mature ITAM tool such as Flexera. Set one purchase path, one inventory, and one renewal calendar. Fund two asset pros, one software buyer, and a part-time data steward.
Budgets stay on track when teams map spend to the life cycle they can steer. Hardware depreciation hits the books monthly, so finance needs forecast reports from ITAM. Cloud costs change daily, so product owners want live usage data from SaaS management. Split dashboards by cadence and both groups stay satisfied.
Rollout order matters more than feature depth. Start where risk peaks. Upcoming ISO audit? Track serial numbers and chain of custody first. Merger next quarter? Map duplicate SaaS apps now to avoid paying twice post-close. Each win pays for the next phase.
Common missteps: hiring a tool before hiring a process, undervaluing data cleanup, ignoring procurement. Fix them by setting a 90-day proof of value tied to one KPI, renewal savings, reclaimed laptops, or fewer audit findings. Prove it, then expand.
Choose based on pain, not hype. The right blend lines up people, data, and timing so savings land before the CFO asks.

Lessons from companies in the wild
Common missteps that surface during rollouts:
- Skipping early stakeholder briefings, so teams felt tracked rather than helped
- Under-estimating data cleanup time when merging feeds
- Chasing 100 percent accuracy before acting, which stalled savings
Treat these as guardrails. Align the scope, pick a clear win, and ship small changes fast.

Conclusion
The article compared IT Asset Management with SaaS Management, mapping each life cycle and the gap that pushed work into the cloud. It laid out the goals and scorecards that shape cost, risk, and insight, then broke down the tools behind those numbers: agents, scanners, API hooks, SSO logs. A guide matched the mix to company size, policies, and budget.
Choose the mix that delivers visibility, control, and savings now.

Audit your company’s SaaS usage today
If you’re interested in learning more about SaaS Management, let us know. Torii’s SaaS Management Platform can help you:
- Find hidden apps: Use AI to scan your entire company for unauthorized apps. Happens in real-time and is constantly running in the background.
- Cut costs: Save money by removing unused licenses and duplicate tools.
- Implement IT automation: Automate your IT tasks to save time and reduce errors - like offboarding and onboarding automation.
- Get contract renewal alerts: Ensure you don’t miss important contract renewals.
Torii is the industry’s first all-in-one SaaS Management Platform, providing a single source of truth across Finance, IT, and Security.
Learn more by visiting Torii.
Frequently Asked Questions
This article explains the distinctions between IT Asset Management and SaaS Management, highlighting their scopes, goals, and tools, as well as providing guidance for effective integration.
ITAM focuses on physical assets, while SaaS Management tracks subscription-based services. They operate on different layers and have unique metrics and governance structures.
Organizations should assess their size, tech stack, and audit needs to determine whether to adopt ITAM, SaaS Management, or a hybrid approach for visibility and control.
ITAM tools typically operate on the hardware level using agents and scanners, while SaaS Management tools leverage browser plugins and API integrations for visibility into cloud environments.
Common missteps include neglecting stakeholder engagement, underestimating data cleanup time, and seeking 100 percent accuracy before implementing necessary changes, which can stall progress.
Companies should prioritize clear ownership, shared data across teams, and actionable KPIs. Regularly auditing assets and eliminating duplicate subscriptions can significantly enhance efficiency.
The article recommends aligning controls to pull from a single evidence locker, thereby simplifying audit prep and streamlining data collection across ITAM and SaaS Management.