The biggest threat to your company’s data isn’t hackers—it’s your own employees. They put your data at risk, not out of malice, but because they want to work faster. Under pressure to do more in less time, employees often turn to shadow IT.
Shadow IT is the use of technology systems, devices, software, apps, and services without the approval of IT.
Today, most of shadow IT is software—more specifically—SaaS. Sometimes, this is called SaaS sprawl, shadow SaaS, or unsanctioned SaaS. The point is, you’ve got a lot of it.
New Report
Shadow AI Response Kit: A Framework for Discovery and Governance
AI is taking over your SaaS stack. Are you ready for the consequences? Check out our guide for frameworks and strategies to help you bring Shadow AI under Governance. In fact, the average organization has approximately 670 apps in its ecosystem—and they only know about a fraction of them. While these tools might boost productivity, they also pose big risks to your security posture, your financial health, and your operational efficiency.
In this article, we’ll reveal the risks, the role of AI, and steps to regain control.
Let’s go!
What Is Shadow IT?
Shadow IT happens when employees use tech or software without IT’s approval. These tools can be anything from personal computers to freemium cloud apps. What separates shadow IT from business resources is not the danger but IT’s knowledge that it exists.
Why Do People Adopt Shadow IT? (Including IT?)
Shadow IT generally crops up when employees are rushing to get work done. Often, the existing tools are seen as too slow or unable to accomplish a specific task. In 2020, we saw this trend explode as companies tried to adapt to remote and hybrid work.
Companies and employees alike desperately sought productivity above all else. Remarkably, 54% of young office workers worried more about deadlines than exposing the business to a data breach. Even IT felt the squeeze. 91% felt pressured to compromise security for business continuity during the WFH revolution.
While reporting is mixed, most IT professionals say that those trends of SaaS adoption never really went away—they became part of a culture of productivity at all costs. Even IT is not immune to the drive to get more done, with 83% of IT staff admitting to using unsanctioned tools at work.
TL;DR: Why Shadow IT Happens
- Employees adopt tools because approved solutions are too slow or complex.
- During the WFH revolution, productivity pressure made shadow IT more common.
- Even 83% of IT staff admit to using unsanctioned tools.Security Vulnerabilities
Here are examples of shadow IT that you’ve probably experienced first-hand.
Common (But Costly) Examples of Shadow IT
- Marketing Teams Using Unauthorized SaaS Tools: A marketing department might subscribe to a new social media analytics platform without informing IT, aiming to gain real-time insights and outpace competitors.
- Personal Cloud Storage in Finance: Employees in a finance firm might use personal cloud services like Dropbox or Google Drive to access work documents remotely, unintentionally exposing sensitive financial data.
- Healthcare Professionals and Mobile Apps: Doctors or nurses might download unapproved medical apps on their personal devices to manage patient information, potentially violating patient confidentiality and regulatory compliance.
- Engineering Teams Deploying Unvetted Software: An engineering group might implement a new code repository or collaboration tool that hasn’t been vetted for security vulnerabilities, putting proprietary information at risk.
- Executives Using Unauthorized AI Tools: Leaders are not exempt—many turn to AI to increase output, often bypassing security protocols.
If shadow IT is everywhere, what are the true risks of this pervasive cultural shift?

What are the Risks of Shadow IT?
Shadow IT affects security, efficiency, and finances. The impact depends on your policies and tools. These are some of the most common risks:
1. Security Vulnerabilities
- Data Breaches: Unauthorized tools may not have robust security features, exposing sensitive data to cyberattacks. For instance, an employee using an unsecured file-sharing service could inadvertently leak confidential information.
- Malware and Phishing Attacks: Shadow IT solutions are likelier to introduce malware into the organization’s network. Employees might download apps from untrusted sources, opening doors for phishing attacks and other malicious activities.
2. Compliance and Regulatory Issues
- Violation of Data Protection Laws: Many industries are subject to strict regulations regarding data handling and privacy, such as GDPR, HIPAA, or PCI DSS. Using unauthorized applications can lead to non-compliance, resulting in legal penalties and reputational damage.
- Auditing Challenges: Shadow IT complicates the auditing process, as undocumented tools and services make it difficult to provide accurate records of data access and processing activities during compliance audits.
3. Operational Inefficiencies
- Data Silos: When employees use disparate tools that aren’t integrated with the organization’s systems, it can lead to fragmented data storage, making it difficult to access and analyze information across the company.
- Resource Drain: IT teams may have to divert resources to address issues caused by shadow IT, such as resolving security incidents or integrating unsanctioned tools after the fact.
4. Emerging Risks: Shadow AI
- Unvetted AI Applications: Shadow AI tools, adopted without IT oversight, bring new risks. These applications may process sensitive data using algorithms that lack transparency, leading to biased outcomes or unintended data exposure.
- Data Privacy Concerns: Shadow AI may store data in locations not compliant with data residency requirements, or they may share data with third parties without consent.
5. Third-Party Integrations and API Risks
- Unsecured APIs: Shadow IT tools may use application programming interfaces (APIs) that are not secured properly, providing attackers with potential entry points into the organization’s network.
- Interoperability Issues: Unapproved applications might not integrate well with existing systems, leading to vulnerabilities when data is transferred between platforms.
6. Financial Risks
- Surprise expenses: Often, shadow IT is adopted and even paid for without going through appropriate channels. In fact, Gartner studies have found that shadow IT is 30 to 40 percent of IT spending in large enterprises, and our research at Everest Group finds it comprises 50 percent or more.
- Contracts and Technical Debt: Often, teams or individuals will even sign contracts for applications outside of sanctioned procurement channels. Sometimes, these contracts will contain terms that violate regulatory concerns and costs that exceed budgets. Additionally, these sunk costs can force a company to continue using sub-par tools.
7. Operational Inefficiencies
- Redundant tech: Sometimes, the shadow IT tech is actually redundant to sanctioned tools. This can confuse and make app admin work more difficult for IT. It also complicates managing app access for employees.
8. Hidden Toll on IT Teams
- Shadow IT is demoralizing: when we talk to IT professionals, the real issue is not the risks but the unknown. It is exhausting, demoralizing, and unsettling to know that there are vulnerabilities and problems hiding—and you have no way to truly prepare. Preventative measures are critical but often ignored. Like how insurance covers surgery but not a healthy diet, leadership often prioritizes reactive security over proactive visibility.
And that’s frustrating.
The cumulative effect of these risks is dramatic. An otherwise healthy company can be crushed by the security, operational, regulatory, reputational, and financial costs of shadow IT.
TL;DR: What Are the Risks of Shadow IT?
- Security Vulnerabilities
- Data Breaches
- Malware & Phishing
- Compliance Issues
- Regulation Violations
- Audit Challenges
- Operational Inefficiencies
- Data Silos
- Resource Drain
- Shadow AI Risks
- Data Handling Compliance
- Privacy Concerns
- Financial Risks
- Surprise Costs
- Redundant Tools
Now, we’ll examine strategies you can use to uncover shadow IT within your organization—especially tools that are SaaS and AI-based.
How to Manage Shadow IT in 2025 (and Beyond)
First, it’s important to recognize that you can’t eliminate shadow IT. That cultural shift towards productivity has become ingrained in many organizations and industries. However, that doesn’t mean it’s hopeless; it just means the tactics for managing unsanctioned technology must shift. A company policy and a CASB tool won’t cut it today—you need to think more holistically. Discovery and prioritization based on risk levels must be your focus. Below is your plan from start to finish.
1. Tackle Visibility and Monitoring
Out of sight, out of control.
Visibility is key to controlling shadow IT. Without that insight, you inherit all the risks of shadow IT with none of the control or upside (more on that later).
There are many tools that help with shadow IT discovery that can generally be put into a few groups.
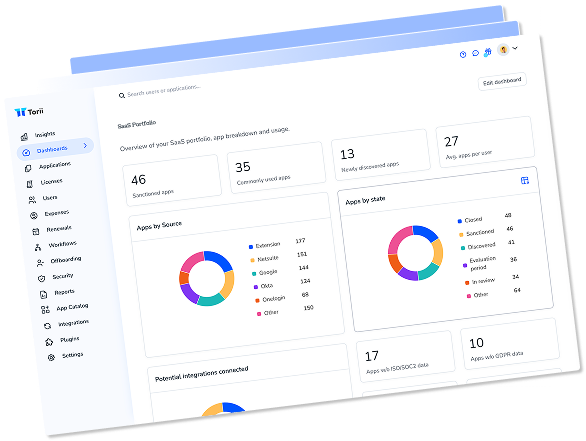
SaaS and AI Discovery
SaaS Management Platforms (SMPs) help detect all SaaS and AI tools in your company. Tools like Torii integrate with your existing tech stack and deploy holistic SaaS discovery. Even something as small as a browser extension can be detected by an SMP. These platforms provide centralized oversight to monitor app discovery, monitor usage, manage contracts and expenses, and even automate the app and employee lifecycle. For most companies today, SaaS Management is no longer optional.
In fact, according to the Gartner® Magic Quadrant™️ for SaaS Management Platforms, “Through 2027, organizations that fail to centrally manage SaaS life cycles will remain five times more susceptible to a cyber incident or data loss due to incomplete visibility into SaaS usage and configuration.”
Learn how Article discovered 375+ shadow IT apps immediately with Torii
Additionally, some SMPs, like Torii, integrate with MDMs like Jamf, Kandji, Jumpcloud, and Intune to show local software discovery alongside SaaS discovery to get a complete picture of software use across the company.
Test Torii’s SaaS Discovery engine for 14 days for free; no credit card is needed.
Network Monitoring
Network monitoring tools like SolarWinds, Wireshark, etc, monitor traffic, performance, and anomalies within the network. They ensure that all the devices and applications accessing the network behave as expected. These tools are perfect for anomaly detection. Typically, though, these tools are less associated with conventional discovery and more with security as they specialize in monitoring internal network traffic, which external users will bypass when working outside the office.
Asset Discovery
Asset discovery tools like Lansweeper or Spiceworks focus on identifying and cataloging all IT assets (such as hardware, software, and cloud services) within the organization. These tools are typically most effective at cataloging physical and virtual infrastructure and on-premise software or hardware. Unfortunately, this class of tools often struggles with remote and hybrid environments where on-prem infrastructure is less critical.
Mobile Device Management (MDM)
MDM Platforms like Jamf or Kandji focus on managing mobile devices like smartphones, tablets, and laptops. They help enforce security policies, deploy apps, and monitor compliance, especially for bring-your-own-device (BYOD) policies or remote workforces. Often, these tools also monitor for local software used on a device.
Which Tool Discovery Tool is Right for You?
The answer is probably a combination of tools. Today, cloud apps are quickly becoming the dominant form of shadow IT, making SaaS Management a key tool for your discovery stack. If your team is remote, you likely also require a number of mobile devices making an MDM an important tool. If your company still utilizes on-prem, physical infrastructure, and work is done in-office, then asset discovery and network monitoring tools are still important for the security of your workplace.

2. Adopt Zero-Trust Security Frameworks
In a zero-trust model, trust is never implicit; verification is always required.
Utilize Identity and Access Management (IAM) and Single Sign-On (SSO) Solutions
- Centralized Authentication: Implement IAM and SSO solutions such as Azure Active Directory, AWS IAM, or Okta SSO to authenticate and authorize users across various platforms and applications. This is critical to managing the access controls for these applications.
- Principle of Least Privilege: Ensure users have access only to the resources necessary for their roles. This is critical to minimizing someone’s ability to integrate systems containing sensitive data with shadow IT tools. Thus mitigating downside risks.
3. Develop and Enforce Clear Policies
Create policies that are easy to understand, easy to enforce, and consistent with company culture.
- Create Shadow IT Policies: Define acceptable technology use and procedures for adopting new tools. Clearly communicate the risks of unauthorized applications and devices.
- Establish BYOD Guidelines: Mandate security measures like encryption, VPNs, and mobile device management (MDM) for personal devices used for work. Specify acceptable activities and prohibited actions.
- Regular Audits and Compliance Checks: Schedule audits to ensure policy compliance and identify shadow IT instances. Generate compliance reports for management and regulatory bodies.
- Establish automated monitoring: to help keep everyone on track, use a tool such as an SMP to automatically notify users when they have breached a shadow IT policy, and to notify IT, Security, and Finance teams when certain criteria are met.
- Articulate an Application Rationalization Plan: It’s essentially a process by which you decide which apps to keep, replace, consolidate, or retire, aiming to cut redundancies, save costs, and boost efficiency.
4. Foster Collaboration Between IT and Business Units
Bridging the gap between IT and other departments is crucial for managing shadow IT effectively.
- Open Communication Channels: Hold regular meetings between IT and other departments to discuss needs and challenges. Appoint technology liaisons to facilitate communication.
- Involve Stakeholders in Decision-Making: Include department representatives in evaluating and procuring new technologies to meet business and security requirements. If an individual wants a new tool, instead of saying “no,” say “why?” You’ll encourage communication and learn something new along the way.
- Training and Awareness Programs: Offer regular cybersecurity training on best practices and the risks of shadow IT. Integrate IT policy education into onboarding for new employees.
Want to get leadership on your side for this initiative? Learn how to earn buy-in from leadership within teams like Security and Operations.
5. Streamline IT Approval Processes
Simplifying procedures reduce the incentive for employees to bypass official channels.
- Agile Procurement Procedures: Create user-friendly platforms for submitting technology requests with clear response timelines. Establish criteria for fast-tracking low-risk tools. An application catalog is helpful for this.
You can’t eliminate shadow IT, and you can’t prevent risk alone, but with the right tools, the right process, and cross-functional communication, you can turn shadow IT from a threat to an opportunity.
TL;DR: How to Manage Shadow IT in 2025 (and Beyond)
- Improve Visibility
- SMPs for SaaS and AI
- MDMs for device management
- Network monitoring and Asset Discovery for on-prem orgs
- Adopt Zero-Trust Security
- Implement Identity and Access Management (IAM) and Single Sign-On (SSO) to better organize approved applications
- Create Clear Policies
- Establish and enforce Shadow IT and BYOD policies, make them clear and consistent with company culture
- Foster Cross-Team Collaboration
- Encourage communication between IT and business units to align on tools and security needs
- Streamline IT Approvals
- Simplify the approval process with agile procurement, so employees can quickly get approved tools without bypassing IT
In this next section, we’ll learn why shadow IT represents something important for your organization and how to leverage it.
Leveraging Shadow IT’s Potential
Shadow IT has always been seen as a problem. But what if that’s missing the point?
There are massive risks with unmanaged shadow IT, but there are also ways to turn that sprawl into a competitive advantage. As one CIO put it, embracing shadow IT is how IT goes from the department of “no” to the department of “know.” But that, requires the discovery of your shadow IT.
Here are some tactics to help you leverage shadow IT’s potential!
Find the BEST Tools
- When employees adopt apps, they’re really adopting solutions to problems. Shadow IT acts as a fast-track testing ground for the best tools employees actually need. You can think of it like Darwin’s survival of the fittest. Employees will test, trial, and quickly identify the tools that are most fit for their work. Sometimes, that will be an established and sanctioned tool, but often it will be a new app ready to disrupt the other players. That being said, this requires IT monitoring (something easily done with an SMP). By speed-running that evaluation, you’ll have a better tech stack than your competitors and a tech stack that employees genuinely love!
Optimize Costs and Resource Allocation
- Did you know that shadow IT can actually save you money? It’s true! Often, companies pay massive amounts for tools that go unused. As much as 66% of company tools are left idle for months at a time—and that’s because the apps are either unnecessary or redundant. By monitoring app usage through a SaaS Management Platform, you’ll find out which tools people actually use. In fact, among SMBs who created a shadow IT team, 80% said that the effort had had a positive financial impact.
Improve Alignment and Collaboration Between IT and Business Units
- Often, business units bypass IT and adopt shadow IT because they believe that IT either takes too long or is likely to say no. But what if we flip the script? If IT allows experimentation while monitoring security, it creates a collaborative environment. IT becomes the enablers and can help to align the priorities of different departments throughout the company via the tools they use.
TL;DR: Leveraging Shadow IT for Innovation
Shadow IT can help identify the best tools for productivity. By monitoring usage through SMPs, you can find out which tools employees love and use most, helping optimize your tech stack.What’s Next for Shadow IT?
Management of shadow IT is no longer an option—especially shadow SaaS. According to Gartner, by 2027, organizations that fail to centrally manage cloud applications will:
- “Be five times more susceptible to a cyber incident or data loss due to incomplete visibility into SaaS usage and configuration.”
- “Overspend on SaaS by at least 25% due to unused entitlements and unnecessary, overlapping tools.”
While that sounds intimidating, it provides an exciting chance for IT professionals to tackle the problem.
What’s next for shadow IT? It’s difficult to say, but here are some things we know for sure:
Shadow AI will dominate shadow IT
Our Benchmarks Report found that 7 of the top 9 shadow IT apps were actually shadow AI and that will only continue. More and more employees will increase productivity through the power of LLMs and AI agents. But, this comes with risk. Often, these can result in breaches or AI’s training on your sensitive IP. One way to combat this is to develop a Data Map to find out what data you have, who has access to it, where it flows, and where it’s held.
Regulatory Crackdowns Will Continue to Increase
- The global average cost of a data breach in 2024 was $4.88 million—a 10% increase over last year and the highest total ever.
- 1 in 3 breaches involved shadow data, showing the proliferation of data makes it harder to track and safeguard.
While shadow IT is here, IT’s active management is more important than ever before.
Shadow IT Will Start to Come From Within the Organization
For the most part, we’ve focused on shadow IT as someone bringing in outside resources, but with the proliferation of low-code and no-code platforms, more and more shadow IT will be created by the employees themselves! IT will need to find creative ways to identify internal threats without squashing innovation.

Conclusion
Shadow IT is here. The question isn’t how to stop it, it’s how to maximize the good and minimize the bad? While it poses significant risks—including security vulnerabilities, compliance breaches, and operational inefficiencies—it also highlights a proactive drive among employees to enhance productivity and innovation. By adopting a holistic approach that includes visibility and monitoring, zero-trust security frameworks, clear policies, and collaboration across departments, organizations can effectively manage shadow IT. This not only mitigates potential risks but also leverages the innovative solutions that employees bring to the table, turning shadow IT from a liability into a competitive advantage.
To navigate shadow IT, especially with the surge of SaaS and AI applications, you need the right tools. Torii’s SaaS Management Platform empowers organizations to discover, monitor, and manage all SaaS applications—including those operating in the shadows. With Torii, you gain unparalleled visibility into your software ecosystem, enabling you to mitigate risks, optimize costs, and foster innovation securely. Take control of your shadow IT and transform it into a strategic asset by partnering with Torii today.
Frequently Asked Questions
Shadow IT refers to the use of technology systems, devices, software, applications, and services without explicit approval from the organization’s IT department. This includes any tools or platforms that employees adopt independently to enhance productivity but are not sanctioned by IT.
Employees often turn to Shadow IT to work more efficiently and meet tight deadlines. When existing, approved tools are perceived as too slow, complex, or inadequate for specific tasks, employees may seek out alternative solutions without IT approval to maintain productivity.
Marketing Teams Using Unauthorized SaaS Tools: Subscribing to new analytics platforms without informing IT.
Personal Cloud Storage in Finance: Using personal cloud services to access work documents remotely.
Healthcare Professionals and Mobile Apps: Downloading unapproved medical apps on personal devices.
Engineering Teams Deploying Unvetted Software: Implementing code repositories without security vetting.
Executives Using Unauthorized AI Tools: Bypassing security protocols to use AI applications.
Security Vulnerabilities: Increased risk of data breaches, malware, and phishing attacks due to unvetted tools.
Compliance and Regulatory Issues: Potential violations of data protection laws like GDPR or HIPAA.
Operational Inefficiencies: Creation of data silos and resource drains on IT teams.
Financial Risks: Unanticipated expenses and redundant tools leading to overspending.
Emerging Risks: The rise of Shadow AI introduces new challenges in data privacy and security.
Shadow IT can expose the organization to significant cybersecurity threats. Unauthorized tools may lack robust security features, making them vulnerable to cyberattacks. This can lead to data breaches, malware infections, and unauthorized access to sensitive information.
Yes, using unsanctioned applications can lead to non-compliance with industry regulations and data protection laws. This poses legal risks and can result in penalties, fines, and reputational damage for the organization.
Improve Visibility and Monitoring: Utilize SaaS Management Platforms (SMPs) to discover and monitor all applications used within the organization.
Adopt Zero-Trust Security Frameworks: Implement Identity and Access Management (IAM) and Single Sign-On (SSO) solutions.
Develop Clear Policies: Create and enforce policies regarding technology use and BYOD (Bring Your Own Device).
Foster Collaboration: Encourage open communication between IT and other business units to align on tool usage.
Streamline IT Approval Processes: Simplify procedures for approving new tools to reduce the incentive to bypass official channels.
Shadow IT can be a source of innovation by highlighting tools that employees find effective. By monitoring and assessing these tools, organizations can identify valuable solutions to officially adopt, thereby enhancing productivity and employee satisfaction.
Shadow AI refers to the use of artificial intelligence applications without IT’s knowledge or approval. These tools can process sensitive data using opaque algorithms, leading to data privacy concerns, biased outcomes, and increased vulnerability to cyber threats.
Growth of Shadow AI: Increased use of AI tools by employees without IT oversight.
Regulatory Crackdowns: Stricter enforcement of data protection laws leading to higher penalties for non-compliance.
Internal Development of Shadow IT: Rise of low-code and no-code platforms enabling employees to create their own applications, posing new management challenges.
The proliferation of SaaS and AI applications has increased the risks associated with Shadow IT. Organizations that fail to manage Shadow IT effectively are more susceptible to cyber incidents, data loss, and financial overspending due to unused or redundant tools.
SaaS Management Platforms like Torii can help organizations discover, monitor, and manage all SaaS applications, including those operating as Shadow IT. These platforms provide visibility, enhance security, optimize costs, and facilitate better collaboration across departments.
Shadow IT can lead to data silos, where information is fragmented across various unsanctioned tools, making it difficult to access and analyze data comprehensively. It can also drain IT resources as teams address issues caused by unauthorized applications.
A Zero-Trust Security framework operates on the principle of “never trust, always verify,” requiring authentication and authorization for every access request. This approach helps in mitigating risks by ensuring that only approved and authenticated devices and users can access the organization’s resources.
Provide Adequate Tools: Ensure that employees have access to efficient, approved tools that meet their needs.
Educate Employees: Conduct regular training on the risks associated with Shadow IT.
Simplify Approval Processes: Make it easier for employees to request and receive approval for new tools.
Foster Open Communication: Encourage employees to discuss their needs with IT rather than seeking unauthorized solutions.