Always-on governance
for non-human identities
Automatically assign owners and automate governance.
Non-human identities sprawl
but your processes stall
Service accounts, APIs, integrations, automation, and AI agents are driving a tidal wave of non-human identities. And our old governance processes can't keep up.
Torii's industry leading discovery spots all identities, separates the NHI from the human, and allows you to automate enforcement for the whole organization.
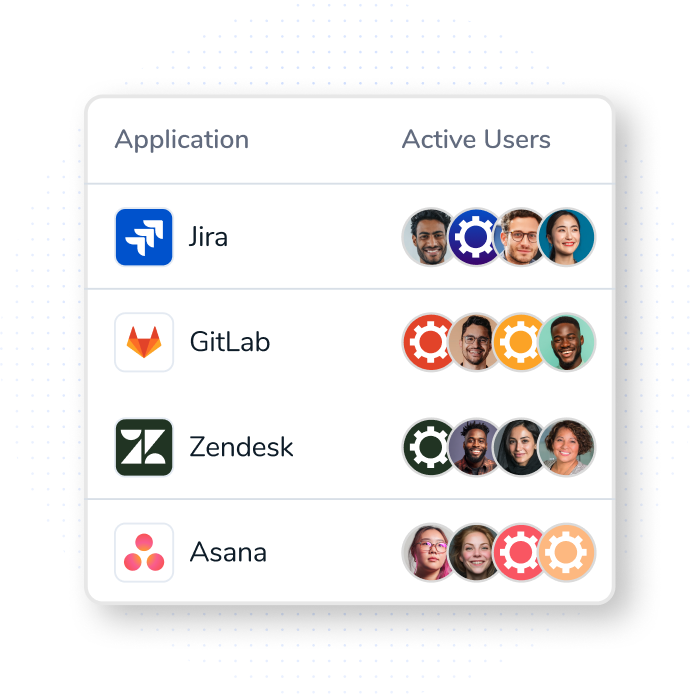
Discover non-human users
outside your AD & SSO
- Multi-source discovery that starts at the browser
- MDM-based signals to surface identities and usage paths outside directory views
- Coverage across agents, bots, integrations, and service accounts
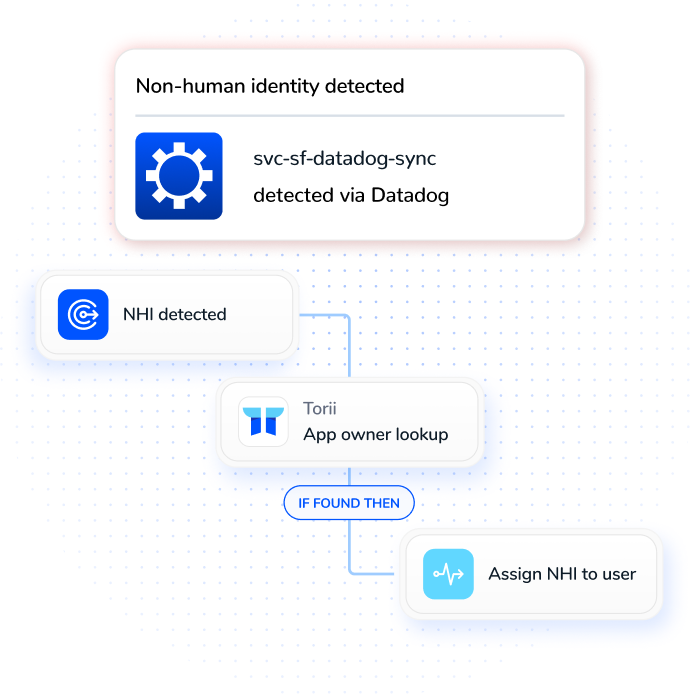
Autoassign owners
enforce guardrails
- Automatically assign each NHI to its application owner—no manual triage
- Delegate via the Task Hub—Security oversees, owners execute
- Automatically reassign owners when people leave, so nothing goes unowned
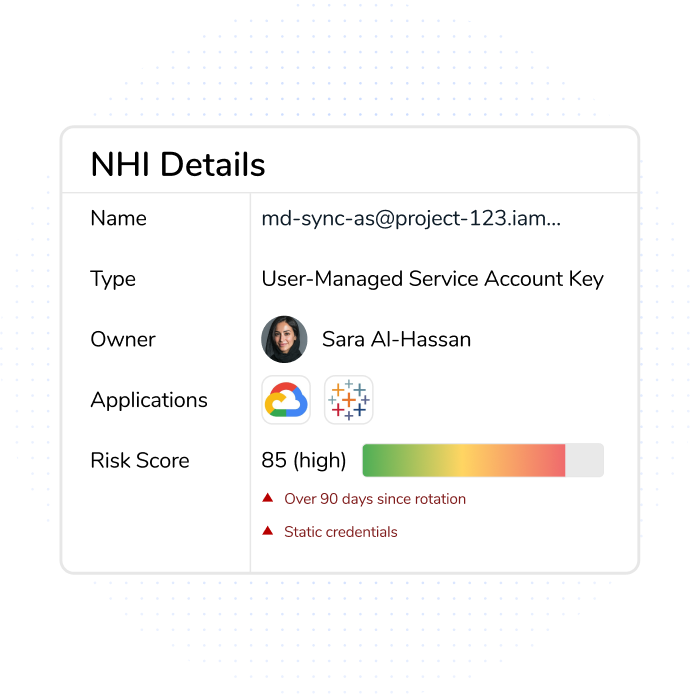
Prioritize management
with NHI risk your AD & SSO
Torii assigns each NHI a risk score and delivers a prioritized list with reasoning—so the most exposed identities are addressed first.
- Scores based on multiple signals like security posture, encryption, and vendor health
- Get a prioritized list with reasoning so you know exactly why certain NHIs come first
- Torii routes tasks to owners for action so issues are reviewed and resolved
Automatically enforce
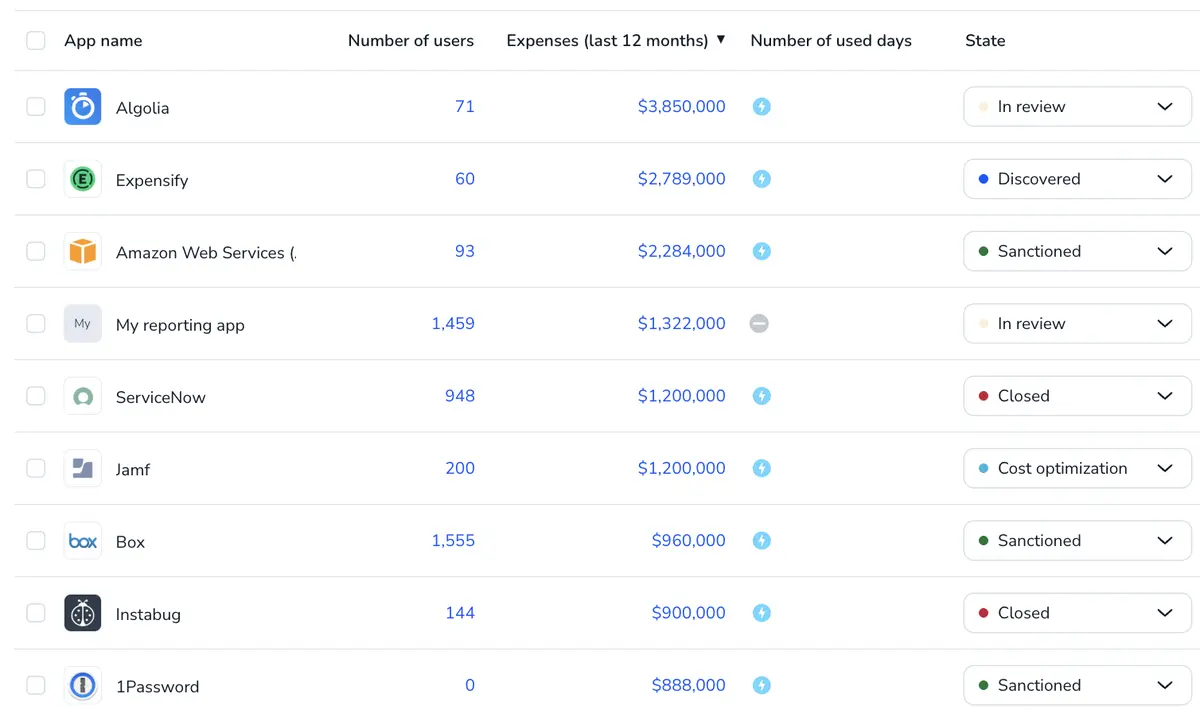
least-privilege policy
Torii automatically enforces least-privilege principles for NHIs—so you reduce risk without manual intervention.
- Automatically adjust permissions to the minimum needed for each NHI
- Enforce least-privilege policies continuously so no identity retains excessive access over time
- Reduce manual workload by letting Torii handle permission cleanup automatically

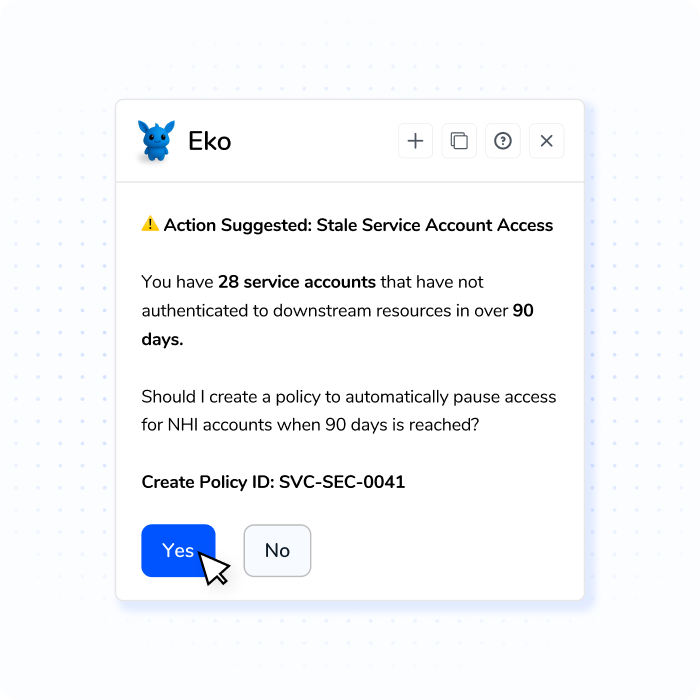
Detect risk patters
and policy solutions
Eko, your governance copilot, identifies patterns of risky NHI adoption and usage, then suggests policies that prevent those risks at their source—so you can enforce lasting solutions.
- Get evidence-based recommendations with drillable data for full context
- See clear, natural-language explanations of the policy reasoning
- Chat with your data to explore insights and confidently approve solutions
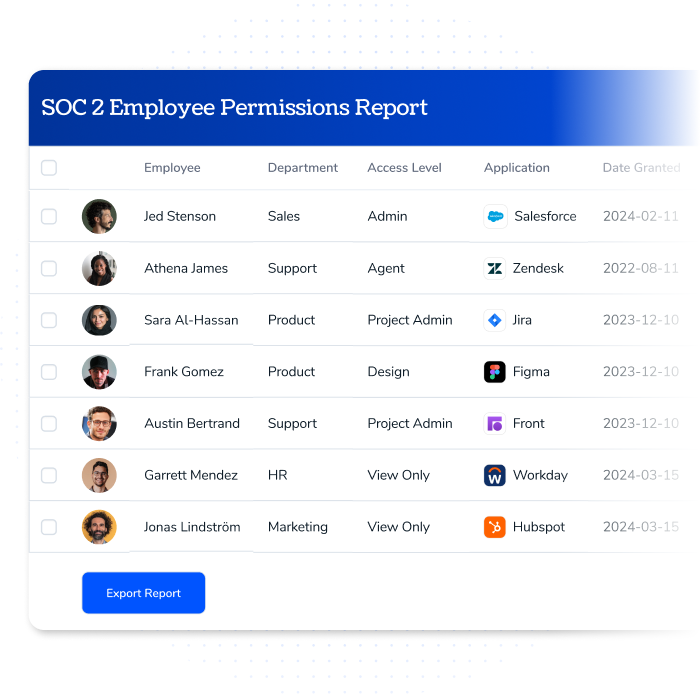
Audit ready by design
Torii automatically logs every NHI action and policy decision, providing a complete audit trail that keeps you compliant and ready for review.
- Maintain a full audit trail of all changes and actions automatically
- Easily access and share records for compliance checks and audits
- Demonstrate governance and accountability with transparent, tamper-proof logs
Ready to keep license savings continuous?
See how Torii keeps licenses aligned to real usage and company policies.
Frequently Asked Questions
What are non-human identities (NHIs)?
Non-human identities (NHIs) are identities used by software—agents, bots, service accounts, integrations, and machine identities—that authenticate and perform actions without a person behind each login.
How does Torii discover NHIs others miss?
Torii uses additional discovery layers, including browser and MDM signals, to detect identities that AD/SSO-only approaches don’t capture.
What goes into Torii’s NHI risk scores?
Risk scores are based on multiple signals, including but not limited to, compliance and encryption indicators, plus incident-related signals and status changes used to prioritize remediation.