Access requests
that start with policy
Utracked requests create silent risk
Most access is still granted through DMs, email threads, or manual tickets. That means no audit trail, inconsistent enforcement, and standing access that quietly outlives its purpose.
Tori brings access requests into a single policy aware control layer, so approvals are consistent, traceable, and enforced the moment access is granted.
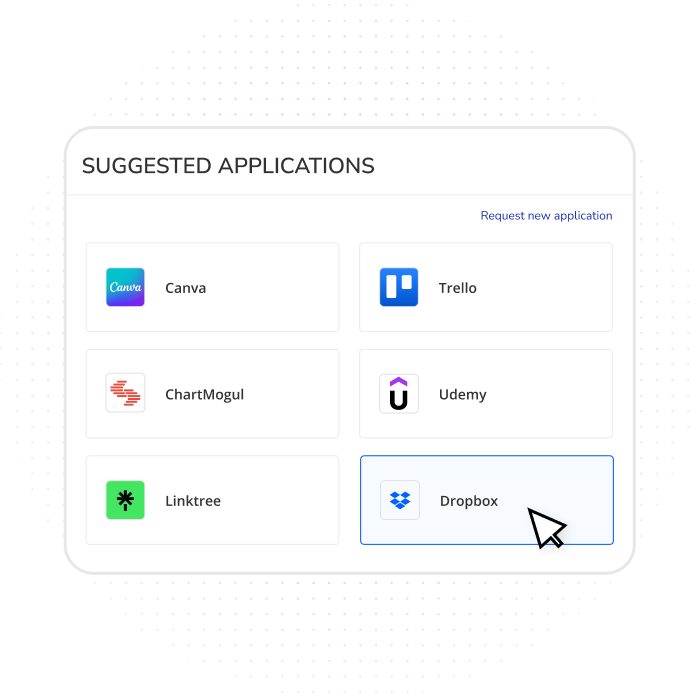
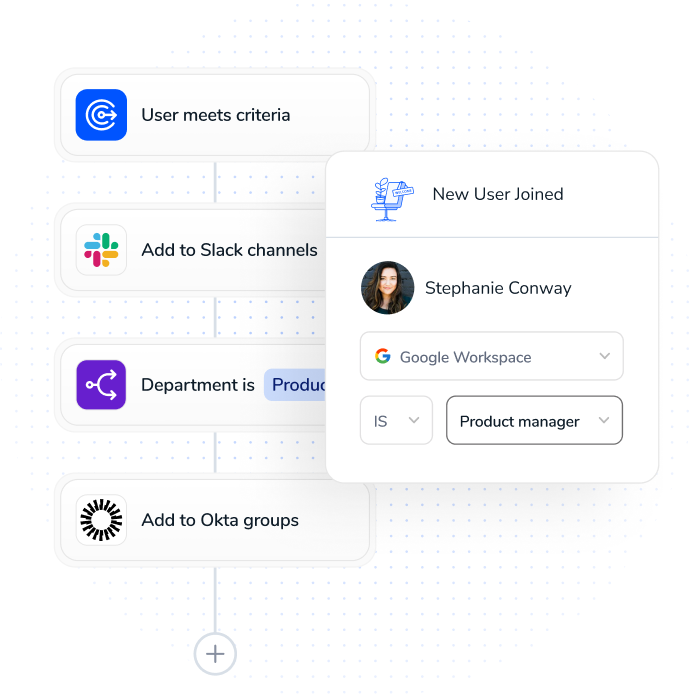
Guide users to
the right access
Out-of-policy requests create unnecessary risk and approval fatigue. Torii helps users request the right access the first time— without workarounds.
- Suggest apps and entitlements based on policy, usage patterns, and peer groups
- Offer Slack, Teams, email, and in-portal request flows
- Drive users to governed access instead of tickets or DMs
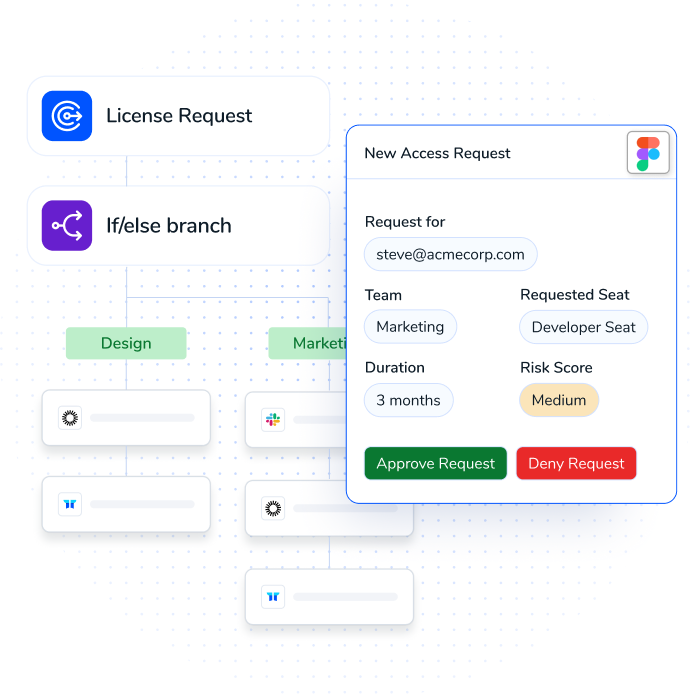
Route requests
with full access
Approvals break down when reviewers lack visibility. Torii routes every request to the right owner with the information they need to make confident, policy-driven decisions.
- Evaluate each request against real app ownership, entitlement data, and policy context
- Automatically determine approvers based on how access is actually managed—not static rules
- Enforce step-up approvals dynamically for privileged, high-risk, or out-of-policy access
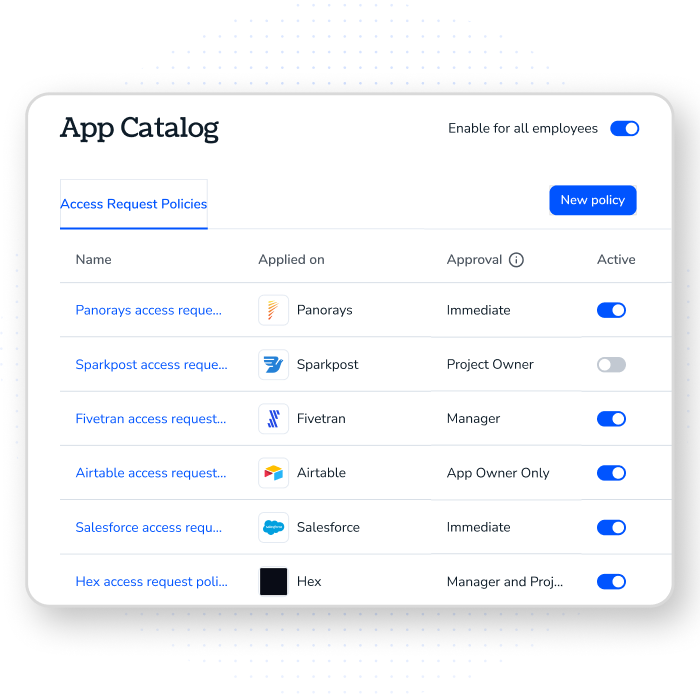
Provision access by
policy automatically
Approvals only reduce risk when they’re enforced consistently across systems. Torii applies policy at the moment of approval so decisions are enforced everywhere they matter.
- Enforce approved access across SaaS, IdP, and infrastructure systems
- Apply roles, scopes, and expiration based on policy—not manual follow-up
- Revoke or adjust access automatically when approvals expire or conditions change
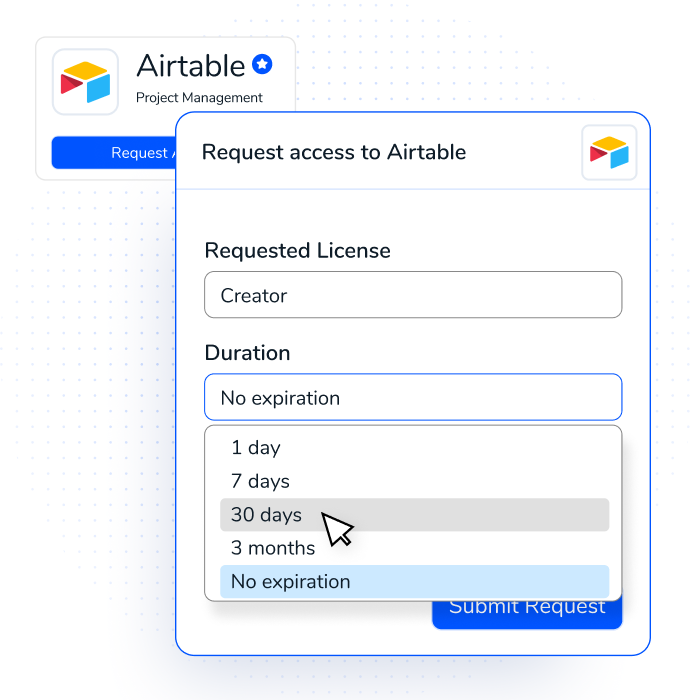
Least privilege
by default
Vague access requests create overprovisioning and approval risk. Torii structures every request to capture the details security teams need—so access is granted precisely, not broadly.
- Require time-bound access by default to prevent standing permissions
- Request license type, role, and justification with built-in recommendations
- Collect security-relevant context through custom fields without slowing users
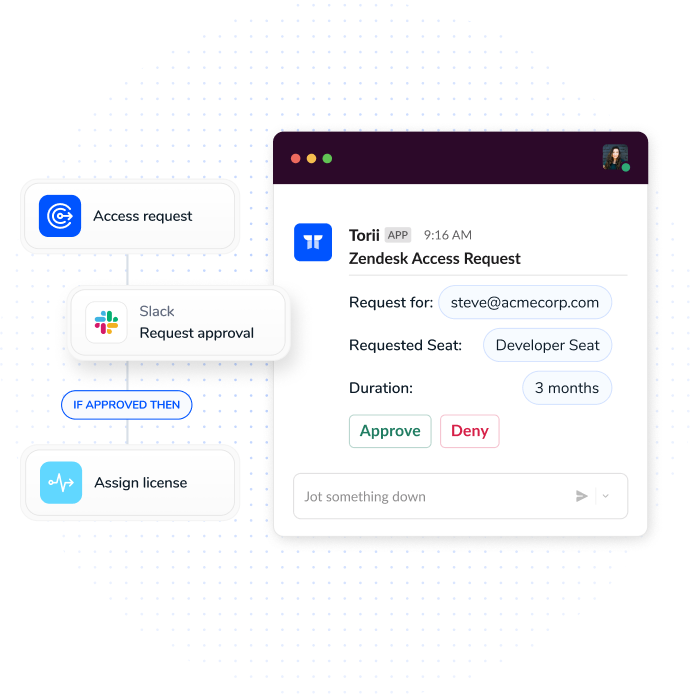
Approve or deny
with one click
Access governance fails when approvals live outside daily workflows. Torii brings requests and approvals into the tools teams already use—without sacrificing control.
- Approve or deny requests from Slack, Microsoft Teams, or email
- Route decisions to the right owners automatically
- Preserve a complete audit trail regardless of where approvals happen
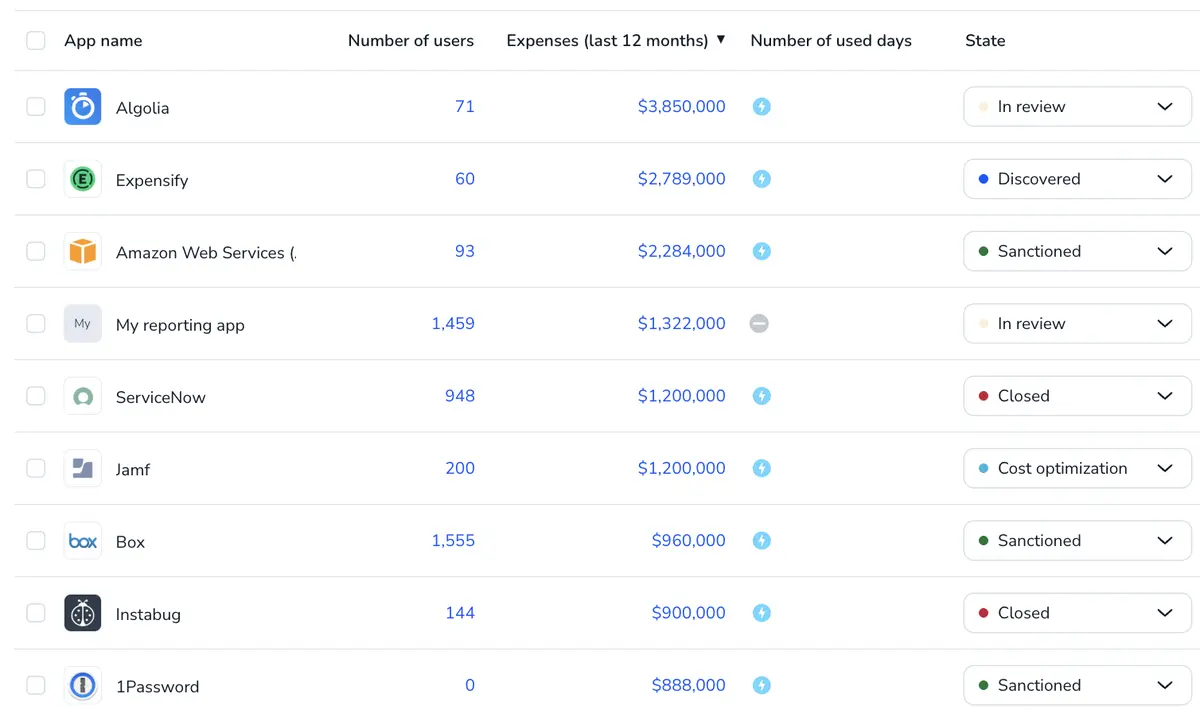
Detect request patterns
and strengthen policy
Repeated requests signal gaps in policy—not user error. Torii analyzes request patterns to identify where policy can be strengthened upstream, so employees get the access they need without constant exceptions.
- Detect recurring requests that indicate missing or overly restrictive policy
- Identify access that should be granted by default based on role or context
- Recommend policy changes that reduce requests while keeping access in bounds
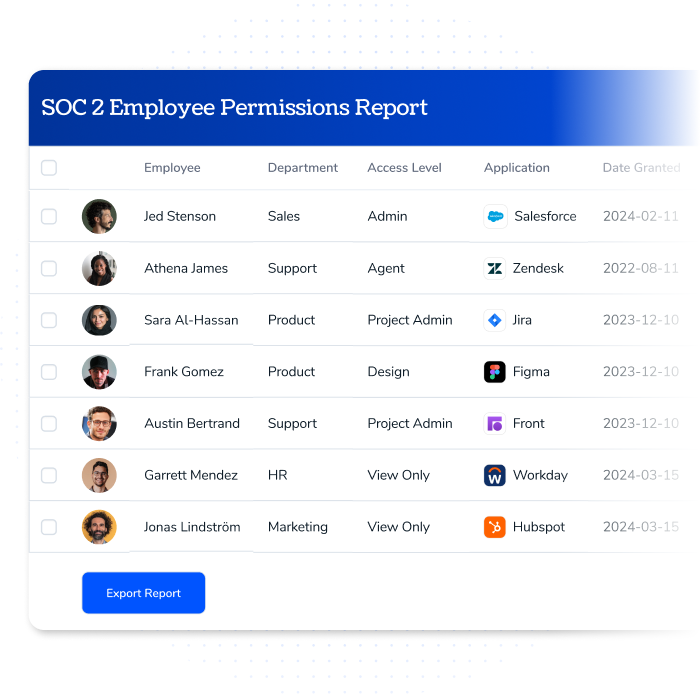
Audit-ready by default
- Record every access decision with clear timestamps and rationale
- Track changes across users, roles, and permissions over time
- Export structured evidence instantly for audits, GRC, or SIEM
Ready to keep license savings continuous?
See how Torii keeps licenses aligned to real usage and company policies.
Frequently Asked Questions
How does access request automation reduce access sprawl and overprovisioning?
Torii enforces least-privilege access by default. Requests are scoped, time-bound, and continuously monitored, ensuring access is revoked when it’s no longer needed and preventing standing or excessive permissions.
How do access request approvals enforce least-privilege access policies?
Access policies define exactly what users can access, under what conditions, and for how long. Approvals enforce those policies at request time, before access is provisioned across systems.
How does access request governance improve security and compliance over time?
Torii analyzes access request patterns, approvals, and exceptions to identify policy gaps. These insights help security teams strengthen access controls, reduce manual reviews, and prevent future risk through continuous governance.