User Provisioning (UP), in the broad sense, is a cornerstone of identity and access management; it encapsulates the suite of enterprise-level processes needed to create, manage, modify, and terminate user accounts and access rights across IT systems. This extensive process involves account provisioning, user management, authentication routines, and user onboarding and offboarding processes often guided by role-based access control principles.
Note: Struggling with cumbersome user provisioning processes? Take charge and streamline account creation, management, and access control effortlessly, all while maintaining top-notch security. Check out how Torii can transform your workflows.
What if you’re not struggling with Access Management?
User provisioning tools automate the critical and complex processes of granting, changing, and revoking access rights involving user directory and privileged access management.
Imagine being able to provide a new hire with a set of keys (access rights) that opens only specific doors (systems) in your company based on their role (role-based access control). That’s the essence of user provisioning!
Efficient Framework: An efficiently designed UP framework encompasses user lifecycle management, from onboarding to offboarding, taking the duty of synchronizing user data across several systems off your plate. It offers capabilities such as self-service user provisioning, which allows users to request additional access autonomously, and automated user provisioning, which speeds up access delivery and reduces manual workload.
Identity Governance: A role in identity governance must be balanced. With user access review as part of it, you can perform frequent checks to ensure that the right users have the proper access at the right time. This significantly reduces unauthorized and redundant access, a prevalent issue in unmanaged IT landscapes.
Workflow Automation: Built on workflow automation, UP enables seamless and rapid account provisioning and de-provisioning, vital during employee onboarding and offboarding. This way, organizations can ensure that ex-employees can no longer access sensitive company information.
Detailed Record Activities: The process also leaves behind audit trails that provide a detailed record of all user provisioning activities. During internal or external audits, these logs are invaluable to demonstrate to assessors that the organization has been competently managing access to its systems and data.
In conclusion, User Provisioning is vital to effective and efficient user and access management, given its role in guaranteeing that every user has the access they require and nothing more. It’s a crucial enabler of security, compliance, and operational effectiveness in today’s digital era.
Examples of User Provisioning (UP)
In IT management, the seamless integration of new users into an organization’s ecosystem is paramount. User provisioning, creating, managing, and deactivating user accounts and access rights in systems, applications, and networks is critical for IT departments. Here are real-world examples showcasing the importance and implementation of user provisioning in various sectors.
Enterprise Business
Salesforce, a leading CRM platform, offers a vivid example of user provisioning in action. When new employees join a sales team, their accounts are automatically created in Salesforce. This process includes setting up their profile with appropriate access levels to customer data, sales records, and collaboration tools. The automation ensures that the new team member can start contributing without delay, fostering efficiency and data security from day one.
Educational Sector
In the education sector, universities often employ user provisioning to manage student and faculty access to resources. At the start of a new semester, IT systems automatically create accounts for new students in the university’s learning management system (LMS), library databases, and e-mail services.
This automated process ensures that students have immediate access to necessary educational resources, enhancing their learning experience. As students graduate or staff contracts end, access is automatically revoked, maintaining system security and data integrity.
Healthcare Setting
Healthcare provides a critical context for user provisioning, where access to patient information must be meticulously controlled. When a new healthcare professional joins a hospital, their access to electronic health records (EHR) is provisioned based on their role.
For example, a nurse might receive access to patient care plans and medication schedules, while a billing specialist would have access to insurance and billing information. This role-based access ensures that sensitive patient data is only accessible to authorized personnel, safeguarding patient privacy and complying with regulations like HIPAA.
These examples underscore the value of user provisioning in maintaining operational efficiency, data security, and regulatory compliance across diverse industries. Organizations can ensure that their resources are used effectively and safely by automating granting and revoking access.
Best Practices for User Provisioning (UP)
Effective user provisioning is critical in any organization, encompassing access management, identity management, account provisioning, and user management. It balances providing necessary access for productive work, enhancing security, and minimizing the human error factor.
Initiate with User Onboarding
Initiating with user onboarding, an automated user provisioning process is recommended, which can help synchronize user data from all connected systems. Automation standardizes the onboarding process, saving time and minimizing possible errors.
Setup Role-Based Access Control
Role-based access control is another best practice, allowing defined roles and specific access privileges depending on job requirements. Privileged access management ensures that users with high-level privileges are correctly managed, mitigating potential risks.
Empower Users with Self-Service User Provisioning
A complement to automated user provisioning, self-service user provisioning empowers users to manage requests for access and updates to their profiles. This user-friendly aspect reduces administrative workload while granting users more control.
Efficient User lifecycle management
Another essential element is user lifecycle management. Supervising an account from the point of onboarding to offboarding ensures efficient access management throughout the working contract. User offboarding is equally crucial as user onboarding. All assigned access should be correctly and timely revoked, minimizing security risks.
Implement Policies
Identity governance goes hand in hand with user lifecycle management, providing a framework for defining and implementing policies for ensuring correct user access. Regular user access reviews are suggested, ensuring access privileges remain updated and secure.
Enable Audit Trail Function
Integrated within the process, an audit trail function is critical, providing accountability and tracking of all activities related to user provisioning. These records are invaluable, particularly for compliance purposes.
Automate Workflow
Workflow automation in user provisioning offers several benefits, such as speed, efficiency, and accuracy. Having software to manage end-to-end user access provides a systematic and disciplined approach, facilitating processes without manual intervention.
Use of Management Tool
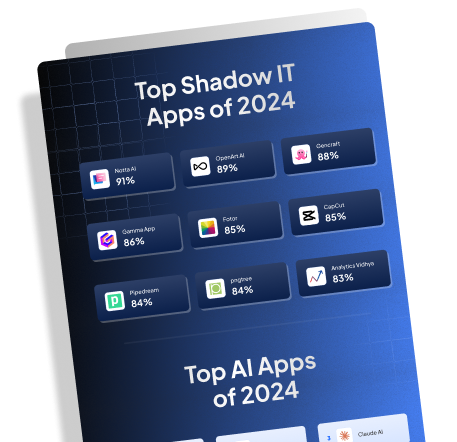
Finally, utilizing platforms like Torii SaaS Management Platform for user provisioning can significantly streamline practices, providing visibility over SaaS expenditures, identifying shadow IT, and automating operations like SaaS on/offboarding, among other features. Torii’s software provides the means to scale their SaaS-related work by allowing IT professionals to build custom integrations and plugins for their cloud apps.
Empathetic insights make it clear that effective user provisioning is not merely about tight controls but also about fostering secure and productive working environments. As companies continue to evolve and grow, their approach to user provisioning should keep pace, ensuring that the process is as intuitive and hassle-free as possible without compromising security.
Related Tools for User Provisioning (UP)
- Torii SaaS Management Platform: A cloud-based tool for overseeing and optimizing Software as a Service (SaaS) usage and expenditures.
- Okta: A user provisioning tool offering enterprises identity and access management solutions.
- OneLogin: A user provisioning platform providing single sign-on, multi-factor authentication, and identity management services.
- Azure Active Directory: Microsoft’s cloud-based identity and access management service for managing users and groups.
- Google Identity: Google’s identity management platform offers single sign-on and multi-factor authentication capabilities.
- Ping Identity: A user provisioning tool providing identity and access management solutions for enterprises and federated identity management.
- IBM Security Identity and Access Manager: IBM’s user provisioning platform offers identity governance, access management, and directory services.
- ForgeRock: An identity and access management platform providing user provisioning, authentication, and authorization services.
- SailPoint IdentityNow: A user provisioning tool offering identity governance, access management, and provisioning services.
- Salesforce Identity: Salesforce’s identity management solution provides single sign-on and user provisioning capabilities.
- RSA SecurID Access: RSA’s user provisioning platform offers secure access with multi-factor authentication.
- Centrify: A user provisioning tool providing identity management, single sign-on, and privileged access management solutions.
- Auth0: A user provisioning platform offering identity and access management services focusing on developers.
- AWS Identity and Access Management (IAM): Amazon Web Services user provisioning service for securely managing access to AWS resources.
- VMware Workspace ONE: VMware’s unified endpoint management platform provides user provisioning, device management, and access control.
- Citrix Workspace: Citrix’s digital workspace platform offers user provisioning and access management solutions.
- JumpCloud: A user provisioning tool providing directory services, single sign-on, and device management for IT environments.
- SecureAuth: A user provisioning platform offering adaptive authentication and identity management solutions.
- Avatier Identity Anywhere: Avatier’s identity management platform offers user provisioning, access governance, and password management solutions.
- Oracle Identity Management: Oracle’s comprehensive identity management platform offers user provisioning, access management, and identity governance.
- Bitium: A user provisioning tool providing single sign-on, identity management, and access control for cloud applications.
- Duo Security: A user provisioning platform offering multi-factor authentication and endpoint security solutions.
- Keeper Security: A user provisioning tool providing password management, encryption, and secure file storage solutions.
- LastPass Business: A user provisioning platform offering password management, single sign-on, and secure sharing for teams.
- One Identity Manager: A user provisioning tool offering identity and access management solutions, including user lifecycle management and access governance.
Related Concepts in User Provisioning (UP)
- Access management: Controlling and managing user access to resources and systems within an organization.
- Identity management: Overseeing the authentication, authorization, and administration of user identities and their access rights.
- Account provisioning: Creating and configuring user accounts, including granting appropriate access privileges.
- User management: Administering and controlling user accounts throughout their lifecycle in an organization.
- Authentication: Verifying the identity of a user to grant access to systems or resources.
- User onboarding: The process of granting access and setting up user accounts for new employees.
- User offboarding: Revoking access and deactivating user accounts for departing employees.
- Role-based access control: Assigning access rights and permissions to users based on their assigned role or job function.
- Privileged access management: Managing and securing access to critical systems and data by privileged users.
- User directory: A central repository that stores and organizes user information, such as usernames, passwords, and access privileges.
- Self-service user provisioning: Allowing users to request and manage their own account access, reducing IT involvement.
- Automated user provisioning: Streamlining the process of creating and configuring user accounts through automated workflows.
- User lifecycle management: Managing user accounts throughout their entire lifecycle, from creation to deactivation.
- Identity governance: Ensuring compliance and security in user access by establishing policies, processes, and controls.
- User access review: Review and audit user access rights to ensure they are appropriate and up-to-date.
- Audit trails: Recorded logs that document user activities and system interactions for security and compliance purposes.
- Workflow automation: Automating the sequence of tasks involved in user provisioning to improve efficiency.
- Employee onboarding: Integrating new employees into an organization, including granting them access to relevant resources.
- Employee offboarding: Terminating an employee’s access to systems and resources upon departure.
- Synchronizing user data: Ensures user information is consistent and up-to-date across multiple systems or platforms.
FAQs: User Provisioning (UP)
Q: What is user provisioning?
A: User provisioning refers to creating, managing, and deactivating user accounts and access rights within an organization’s IT systems.
Q: Why is user provisioning critical?
A: User provisioning helps organizations efficiently manage user access to various systems, applications, and resources, ensuring the right level of access for each user based on their role and responsibilities.
Q: What are the benefits of user provisioning?
A: User provisioning offers several benefits, including enhanced security by granting appropriate access, improved compliance with industry regulations, streamlined user management, increased productivity, and reduced administrative burden.
Q: How does user provisioning work?
A: User provisioning typically involves automating the user creation, modification, and deactivation process through specialized software or identity management solutions. It integrates with HR systems to ensure employees’ access aligns with their employment status and responsibilities.
Q: What is the difference between user provisioning and user management?
A: User provisioning focuses on the automatic creation and allocation of user accounts and access rights, whereas user management involves ongoing administration, maintenance, and monitoring of user accounts, including access reviews and role changes.
Q: What are the standard user provisioning challenges?
A: Challenges with user provisioning include accurately defining user roles and access levels, managing access lifecycle (hiring, transfers, and terminations), maintaining data integrity, and ensuring timely and consistent access provisioning.
Q: What is the role of identity governance in user provisioning?
A: Identity governance encompasses the policies, processes, and technologies that govern user access and role management. It helps organizations align user access with business policies, regulations, and compliance requirements, reducing security risks.
Q: What is self-service user provisioning?
A: Self-service user provisioning allows end users to request and manage their access privileges within defined boundaries. It reduces IT workload by empowering users to initiate access requests and simplifies provisioning.
Q: What is single sign-on (SSO) in user provisioning?
A: Single sign-on (SSO) is an authentication process that enables users to access multiple applications or systems with a single login credentials. User provisioning integrated with SSO ensures that users have the appropriate access permissions across various applications.
Q: How can automated user provisioning improve efficiency?
A: Automated user provisioning reduces manual efforts and associated errors by automating the account creation, modification, and disabling processes. It ensures timely provisioning of access rights, improves productivity, and minimizes the risk of unauthorized access.