What Is SaaS Governance in 2026?

Most companies now run nearly all their essential software through SaaS subscriptions. Each sign-up introduces fresh security, compliance, and budget pressures that traditional governance rarely covers. When those pressures go untracked, gaps open and costs spiral.
Boards want data that proves these duties are covered, auditors demand hard evidence, and employees simply need their apps to run. SaaS governance exists to juggle those demands. A solid program links policy, access, and licensing so risk falls while expenses stay steady. It spells out who may buy software, which controls apply, and how exceptions get recorded. That clarity makes life easier across the board.
The guide below connects policy, identity, and license controls into one framework that reins in SaaS sprawl.
Table of Contents
- Framing SaaS Governance Within Daily Operations
- Turning Governance Policies Into Living Workflows
- Locking Down Access Without Slowing Teams
- Taming Licenses To Save Budget And Stress
- Conclusion
- Audit your company's SaaS usage today
Framing SaaS Governance Within Daily Operations
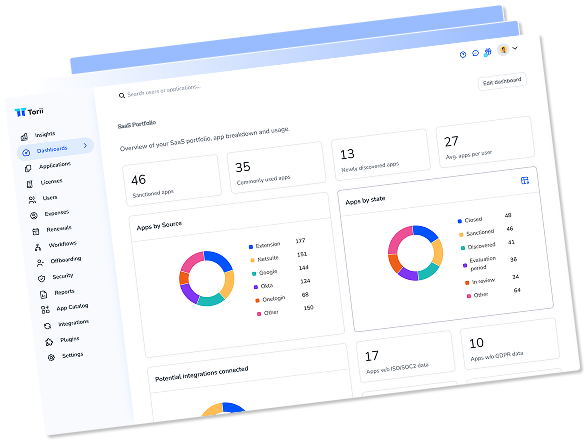
SaaS governance turns scattered app decisions into a controlled, auditable process. Sitting between daily SaaS operations and the board’s risk tolerance, it translates broad rules into checkpoints a team can follow. Asset discovery, spend dashboards, and vendor scorecards still matter, but they remain data feeds. Governance decides when those feeds warrant action, such as blocking a risky sign-up or initiating a security review. It works as the policy brain steering the practical work of SaaS management.
While many teams touch every SaaS tool in the stack, responsibility must be shared, not ambiguous. A simple RACI chart keeps every leader inside the guardrails:
- CIO: Owns strategic fit and keeps the spend in line.
- CISO: Oversees security controls and gauges residual risk.
- Procurement: Weighs in on contract language and pricing wiggle room.
- Line-of-business owner: Covers functional needs and day-to-day adoption.
- IT operations: Stays in the loop on integration work, support, and shutdown timing.
Clear ownership prevents the email ping-pong that often lets risky apps slip through.
Governance shows up at every step of the application lifecycle. During evaluation, a self-service request funnels through templated checks for scope, data type, and vendor risk. At onboarding, automated integrations verify SSO readiness and mark the contract in a renewal calendar. Quarterly, usage telemetry is compared to policy limits; if an app drifts outside guidelines, owners receive a ticket before the next invoice hits. Retirement is also scripted, with data export, license reclamation, and a final security attest captured for audit.
These SaaS governance gates exist for three very practical reasons. They guard sensitive data from accidental exposure, which still causes more than 60 percent of SaaS breaches according to IBM Cost of a Data Breach 2023. Second, they align app use to stated business policy, stopping rogue teams from paying twice for the same feature set. Third, they generate evidence that regulators, investors, and ISO auditors demand. When SaaS governance works, risk and waste drop together, and the board sees a clear line from policy to measurable outcomes.

Turning Governance Policies Into Living Workflows
Every SaaS rule lives or dies on its path from written policy to active control.
Building that path starts with a policy library that maps each regulation and internal guideline to a concrete SaaS rule. Hook SOX account segregation, GDPR data retention, and CIS password length directly to the applications that hold or process that data. Keeping language short and action oriented (for example, “Block file sharing outside tenant” instead of “Users must not share externally”) removes guesswork when the platform translates words into code.
After policies are mapped, teams need a clean way to push each rule through approvals. Instead of email ping-pong, route proposed rules to a RACI queue inside the SaaS management platform. Security signs off on technical impact, finance checks cost implications, and the app owner confirms business fit. Once approved, the platform’s enforcement engine flips the switch; a retention rule, for instance, can be applied across every Slack workspace in under a minute without manual scripting.
Policies are only as strong as the signal watching them. Streaming API logs into the platform adds real-time eyes, while normalized alerts stop teams from juggling vendor-specific dashboards. When a rule pops (for example, an unsanctioned Box folder is shared externally) the tool triggers Slack or ServiceNow tickets and starts the exception timer. Audit mode packages the entire event trail into a PDF that satisfies external auditors without a follow-up call. Boards still want numbers, so surface:
- Mean time to remediate (MTTR) policy violations
- Percent of in-scope apps covered by active rules
- Quarterly trend in exception volume versus total transactions
- Compliance coverage score per framework (SOX, GDPR, PCI)
Even the best policies drift over time and require steady upkeep. A monthly change-control huddle reviews new apps found by discovery scans, sunset apps that left the stack, and metrics trending in the wrong direction. Owners tweak thresholds, retire stale rules, or add clarifying notes, and the platform’s sandbox lets them test safely before rolling live. That tight feedback loop keeps governance aligned with the pace of SaaS adoption and stops yesterday’s controls from blocking tomorrow’s innovation.

Locking Down Access Without Slowing Teams
Access missteps in SaaS rarely make headlines until data walks out the door. A single dormant account with billing-level rights can open the same attack surface as a live administrator, so least-privilege isn’t theory; it is survival. The 2023 Verizon DBIR found that 74 percent of breaches involved human factors, and stale credentials ranked near the top of that list; automated provisioning and fast deprovisioning are the only practical antidotes.
Many firms solve the identity basics with SSO and MFA, yet the friction starts when every new app arrives with its own role map and permission soup. SCIM connectors translate HR system changes into birthright access in seconds, while conditional access rules shut the door if a login appears from an unmanaged device. Over the past year, Okta customers who paired SCIM with device trust eliminated more than 60 percent of orphaned accounts, a clear win for identity hygiene.
OAuth integrations that sit near production data deserve equal attention. GitHub’s 2022 advisory on leaked Heroku tokens showed that even well-scoped tokens can be abused if no one is watching. Continuous permission reviews combine role mining[https://www.toriihq.com/articles/role-mining-saas-management] with user behavior analytics to flag drift before it snowballs into privilege creep. Quarterly access certifications remain the compliance floor, but firms aiming for a tighter window now run rolling reviews that focus on apps holding regulated data.
- Map every SaaS scope to a business role before first use
- Alert when privileged tokens are created outside normal change windows
- Auto-expire improved rights after a set duration
- Require app owners to re-justify broad scopes during each certification cycle
These tactics squeeze lateral-movement risk and shrink the blast radius if a session token leaks. When auditors ask for proof, an export showing closed-loop reviews, deprovision timestamps, and token lifetimes turns a painful scramble into a two-minute screen share.

Taming Licenses To Save Budget And Stress
Unused SaaS licenses quietly bleed budgets and attract auditors, yet many organizations overlook them. Finance teams that dig in often learn thousands of dollars slipped away each month because no one compared entitlements with real usage.
A centralized license inventory reverses that trend by tying every seat to an active user and cost center. Building one is straightforward once usage data from SSO logs and app APIs flows into your SaaS management tool. To begin optimizing your portfolio, start cleaning the data with quick wins:
- Flag any user inactive for 30 days.
- Compare assigned seats to login counts for the past quarter.
- Highlight duplicate subscriptions where two apps solve the same need.
- Surface contracts that exceed auto-renew windows in the next 60 days.
Gartner estimates about 25 percent of SaaS spending goes to waste, so even a modest cleanup pays back fast. Chargeback or showback statements reinforce the change by giving budget owners a direct view of what they consume. Finance teams can then negotiate tier downgrades or shift to pooled licenses, trimming shelfware while keeping capacity for seasonal peaks.
Keeping an up-to-date renewal calendar is the next lever for savings momentum. Tracking notice periods and pricing escalators avoids the last-minute scramble that usually favors the vendor. Contract reviews should go beyond price, pulling in legal and security to confirm data deletion clauses and audit-support terms. That single tweak can shave weeks off compliance responses when regulators ask for proof that retired user data is gone.
Maintaining accuracy across your inventory gives organizations a double payoff. Cost per active user drops; anything below the common 85-to-90-percent use mark leaves room to improve. Second, auditors find a tidy system that ties each license to a named employee and approval trail, which shrinks the sample size they need to test. Those tighter controls and the predictable spend forecasts that follow are why CIOs now treat license oversight as core governance, not clerical cleanup.

Conclusion
SaaS governance only delivers value when policies, access, and licenses tie directly to business risk. Mapping ownership, automating policy checks, tightening identities, and tracking every license dollar help teams cut exposure, satisfy auditors quickly, and redirect budget toward growth. The article’s four pillars detail the roles, actions, and tools behind each step.
Keep those practices in place, and the outcomes speak for themselves: Over time, risk shrinks, wasted spend disappears, and compliance headaches fade into the background for good.

Audit your company’s SaaS usage today
If you’re interested in learning more about SaaS Management, let us know. Torii’s SaaS Management Platform can help you:
- Find hidden apps: Use AI to scan your entire company for unauthorized apps. Happens in real-time and is constantly running in the background.
- Cut costs: Save money by removing unused licenses and duplicate tools.
- Implement IT automation: Automate your IT tasks to save time and reduce errors - like offboarding and onboarding automation.
- Get contract renewal alerts: Ensure you don’t miss important contract renewals.
Torii is the industry’s first all-in-one SaaS Management Platform, providing a single source of truth across Finance, IT, and Security.
Learn more by visiting Torii.
Frequently Asked Questions
SaaS governance is a framework that oversees software subscriptions, ensuring compliance, security, and budget management, while preventing risks associated with untracked software use.
Clear ownership in SaaS governance prevents ambiguity and responsibility gaps, minimizing risks of unauthorized software usage and ensuring accountability among team members.
SaaS governance is involved at every lifecycle stage—from evaluation and onboarding to regular monitoring and retirement—allowing proactive management of software applications.
Policy mapping connects regulations to specific SaaS rules, clarifying rules for software usage and ensuring compliance with standards like GDPR and SOX.
Organizations can lower wasted SaaS costs by maintaining a centralized license inventory, tracking usage against assigned licenses, and identifying unused or duplicate subscriptions.
Automated identity management reduces risks associated with stale accounts, enhances security through rapid provisioning, and maintains compliance through continuous permission reviews.
Real-time monitoring enables immediate detection of policy violations or risks, facilitating swift corrective action, thereby enhancing the overall security posture and compliance readiness.