How to Run Trello Access Reviews: 7 Tools in 2026

Trello boards multiply across organizations faster than most IT teams realize in 2026. What starts as a few project managers tracking tasks quickly expands into every department building workflows, sharing sensitive information, and inviting external collaborators. Before long, contractors have access to product roadmaps, former employees still appear on client-facing boards, and junior staff hold admin permissions they never actually needed.
Project management tools like Trello create unique governance challenges because they store strategic plans, client deliverables, and cross-functional workflows. Unlike document storage where permissions cascade predictably, Trello access sprawl can expose competitive intelligence, unreleased feature plans, or client project details to anyone who was ever added as a board member.
Manual reviews through shared spreadsheets and quarterly audits fail to catch the subtle permission creep that happens between review cycles. Someone gets temporarily elevated to workspace admin during a product launch, and six months later they still have that access. Guest collaborators from an agency partnership retain permissions long after the engagement ends. IT teams struggle to answer basic audit questions about who could view a specific board last quarter, or which departing employees had access to client projects before their last day.
Identity governance platforms automate these certifications, flag inactive accounts with elevated privileges, and generate audit trails that satisfy SOC 2 and ISO 27001 auditors asking who had access to what project boards and when. The seven platforms covered here take different approaches to Trello access audits, from comprehensive SaaS management with identity governance built in to enterprise-grade access certification with deep compliance controls. Your choice depends on whether you need Trello governance as part of broader SaaS visibility or as a focused compliance initiative.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| Okta | ★★★ | ★ | ★★ | ★★ |
| SAP IAG | ★ | ★ | ★★ | ★★ |
| One Identity | ★★ | ★★ | ★★ | ★★ |
| Saviynt | ★★ | ★★ | ★★★ | ★ |
| Omada | ★★ | ★ | ★★ | ★★ |
| Ping Identity | ★★ | ★ | ★★ | ★★ |
Table of Contents
- Torii
- Okta Lifecycle Management
- SAP Cloud Identity Access Governance
- One Identity Manager
- Saviynt
- Omada Identity
- Ping Identity
Torii
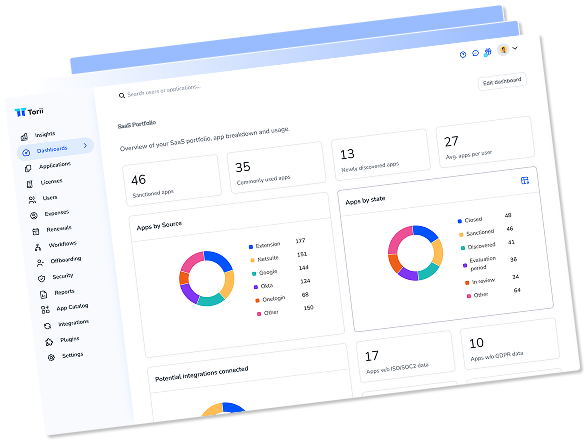
Torii approaches Trello governance as part of a broader SaaS management strategy. The platform connects to Trello through direct API integration, pulling employee names, email addresses, titles, departments, user status, license assignments, and license types into a centralized identity view. This data feeds into automated access review workflows that can run on customizable schedules or trigger based on specific events like role changes or departures.
The platform excels at discovering Trello accounts that IT never knew existed. Through browser extension telemetry and financial record analysis, Torii surfaces shadow Trello workspaces created with personal accounts or corporate cards that bypassed standard procurement. Once discovered, these accounts become part of the same access review campaigns as officially sanctioned deployments, ensuring nothing slips through governance gaps.
Torii’s workflow automation handles the remediation side after reviews complete. When a reviewer flags an account for removal, the platform can automatically deprovision access rather than creating tickets for someone to handle manually. For Trello specifically, this means revoking workspace memberships and board access in near real-time, with complete audit trails showing who made the decision and when the change took effect.
Pros:
- Combined SaaS management and identity governance eliminates the need for multiple tools
- AI-powered discovery finds shadow Trello workspaces across multiple data sources
- In-place attestations let reviewers certify access without context switching
- Workflow automation handles deprovisioning without manual intervention
Cons:
- Enterprise pricing may exceed budgets for smaller organizations
- Cloud-only deployment requires comfort with SaaS security model
Ratings: G2 4.5/5 (302 reviews) · Capterra 4.9/5 (26 reviews)
Okta Lifecycle Management
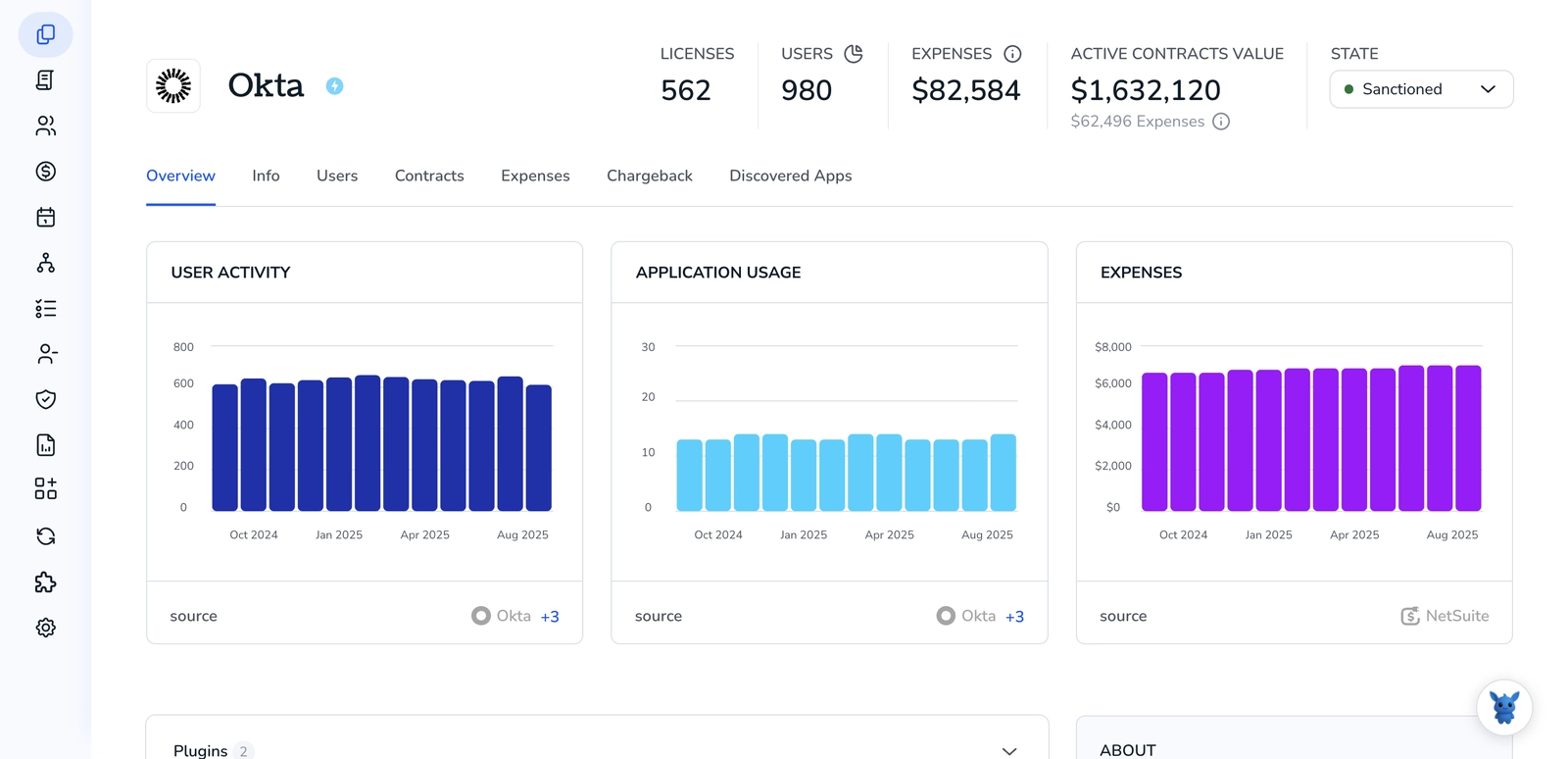
Okta provides Trello governance through its broader identity platform that already handles authentication for most enterprise applications. Organizations using Okta for SSO can leverage the same connection for access reviews, with Trello permissions visible alongside every other application in the portfolio. The platform’s 7,000+ pre-built integrations mean Trello connects through established patterns rather than custom development work.
The 2025 updates to Okta Identity Governance introduced preconfigured certification campaigns that accelerate deployment for common use cases like Trello access reviews. Rather than building campaigns from scratch, administrators select from templates that already incorporate best practices for project management tools. AI-generated access summaries help reviewers understand the full context of each user’s Trello permissions without digging through raw entitlement data.
For organizations already invested in Okta, adding Trello governance requires minimal additional infrastructure. The unified platform approach means reviewers see Trello alongside Salesforce, Slack, and everything else, making cross-application access reviews more coherent. Automated workflows can revoke Trello access immediately when certification decisions finalize, closing the gap between review completion and actual remediation.
Pros:
- Massive integration library connects to virtually any SaaS application
- Modern interface receives consistently positive ease-of-use feedback
- No-code Okta Workflows enables custom automation without developer involvement
Cons:
- Identity Governance requires purchasing the complete OIG bundle
- Group-based provisioning limits fine-grained permission management
- Higher per-user costs accumulate quickly at enterprise scale
Ratings: G2 4.5/5 (1,257 reviews) · Capterra 4.7/5 (914 reviews)
SAP Cloud Identity Access Governance
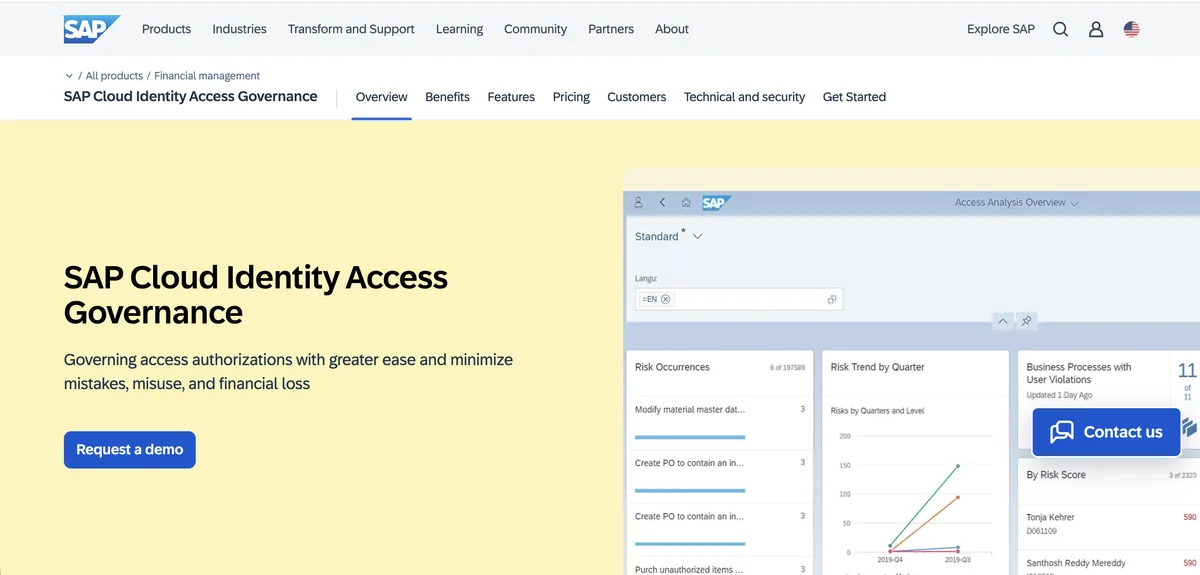
SAP Cloud Identity Access Governance connects Trello into a broader governance framework through SCIM-based integrations. While SAP’s sweet spot remains organizations heavily invested in the SAP ecosystem, the platform extends to non-SAP applications like Trello through its Access Certification service. Teams running SAP SuccessFactors, Ariba, or S/4HANA alongside Trello can consolidate governance across all these applications in a single campaign.
The platform’s Access Certification component handles periodic assessments and confirmation of access rights across multiple systems simultaneously. For Trello, this means certifying workspace memberships alongside SAP roles in the same review cycle, providing a unified view of who has access to what. Campaign progress tracking gives administrators real-time visibility into completion rates, with automated escalation when reviewers miss deadlines.
SAP IAG’s unique Bridge capability allows organizations with existing on-premise SAP GRC deployments to extend governance to cloud applications without abandoning their current investment. This hybrid approach is particularly relevant for large enterprises that standardized on SAP GRC years ago and now need to govern cloud tools like Trello. The machine learning-based role optimization can identify when Trello permissions deviate from peer group norms, flagging potential over-provisioning for review.
Pros:
- Native integration with SAP ecosystem provides seamless governance across platforms
- Hybrid Bridge capability protects existing GRC investments while extending to cloud
- Machine learning role optimization identifies permission anomalies automatically
Cons:
- Platform complexity requires specialized SAP knowledge
- Enterprise-level pricing creates barriers for mid-market organizations
- Limited value proposition for non-SAP-centric companies
- Public cloud only, no private deployment options
Ratings: G2 3.0/5 · Gartner 4.4/5 (114 reviews)
Unlike traditional enterprise applications with defined role hierarchies, Trello's board-level permissions create a flatter access model. Each board has its own membership list, and workspace-level permissions cascade unpredictably. Effective governance tools need to handle both workspace memberships and individual board access to provide complete visibility.
One Identity Manager
One Identity connects to Trello through its extensive connector framework that includes 6,000+ pre-built application integrations. The platform’s attestation policy framework defines which Trello objects get attested, when reviews occur, how often they repeat, and who serves as the attestor. Each attestation case contains the complete context about the Trello access being certified and tracks every decision for audit purposes.
The platform handles multiple certification types relevant to Trello governance, including user attestation for employees managed by their direct supervisors, external user attestation for contractors and partners, and organizational certification for reviewing access across entire departments. This flexibility allows organizations to structure Trello reviews based on their specific compliance requirements rather than forcing a one-size-fits-all approach.
One Identity’s strength in hybrid environments makes it suitable for organizations running Trello alongside Active Directory-managed systems. The platform provides a cross-system view that merges Trello cloud access with on-premise application permissions, giving reviewers unified visibility. For SAP-centric enterprises, One Identity’s certification since 2003 enables deep governance across both SAP and project management tools like Trello in integrated campaigns.
Pros:
- Cost-effective compared to enterprise competitors like SailPoint
- Unified IGA and PAM eliminates need for separate privileged access solutions
- High customizability adapts to specific organizational requirements
Cons:
- Attestation user experience receives criticism for outdated interface
- Steep learning curve requires implementation partner support
- Azure AD connector gaps create challenges for Microsoft-centric environments
Ratings: G2 3.5/5 · Gartner 4.4/5 (155 reviews)
Saviynt
Saviynt’s cloud-native Identity Cloud platform approaches Trello governance through continuous compliance rather than periodic campaign cycles. The platform maintains always-on evaluation of Trello permissions, detecting risks automatically and triggering micro-certifications when anomalies appear. This shifts access reviews from calendar-driven exercises to risk-based events that address problems as they emerge.
The AI-powered Trust Scoring capability reduces reviewer workload by automating decisions on low-sensitivity Trello access while flagging high-risk permissions for human attention. Peer group analysis identifies when a user’s Trello permissions deviate significantly from similar roles, surfacing potential over-provisioning without requiring reviewers to manually compare access patterns. Organizations using Saviynt report 60% improvement in review completion times and 35% increase in actual revocations.
Saviynt’s mobile certification experience enables reviewers to complete Trello access decisions from anywhere. Line managers can approve or reject access requests during brief windows of availability rather than waiting until they’re back at their desks. This accessibility improves completion rates and reduces the pressure that builds when certifications pile up waiting for busy approvers.
Pros:
- Only platform with unified IGA and PAM on the same code base
- Highest Gartner Peer Insights rating in IGA category with four consecutive years as Customers' Choice
- AI-powered certifications reduce approver workload by up to 75%
Cons:
- Customer support receives mixed reviews for response times
- Platform stability concerns with occasional workflow disruptions
- Total cost of ownership increases significantly with implementation services
Ratings: G2 3.5/5 · Gartner 4.8/5 (185 reviews)
Omada Identity
Omada focuses heavily on governance-driven identity management, making it particularly strong for organizations where compliance requirements dominate Trello access decisions. The platform provides real-time visibility into access rights and user activities through intuitive dashboards that surface problems before they become audit findings. Automated discovery flags orphaned Trello accounts and dormant access without requiring manual investigation.
The platform’s AI assistant Javi allows entitlement owners to launch Trello access reviews directly from within collaboration tools like Microsoft Teams. Rather than logging into a separate governance portal, managers can certify access, remediate risks like orphaned accounts, and complete reviews through conversational interfaces. This reduces friction and improves completion rates for busy approvers who find traditional governance interfaces time-consuming.
Omada’s 12-week deployment guarantee addresses one of the biggest pain points in IGA implementations. While many identity governance projects drag on for months or years, Omada’s accelerator approach gets organizations certifying Trello access within a quarter. The 50+ pre-built report templates support regulatory requirements from ISO 27001 to SOX to HIPAA, reducing the effort needed to satisfy auditors asking about project management tool access.
Pros:
- Exceptional governance capabilities for compliance-heavy environments
- Robust reporting engine with complete audit trail retention
- 12-week guaranteed deployment significantly faster than industry average
- AI assistant enables access reviews directly from Microsoft Teams
Cons:
- Large-scale re-certification processes can experience performance issues
- Cloud version significantly more expensive than on-premise option
- Report aesthetics appear dated despite functional capabilities
Ratings: G2 4.5/5 · Gartner 4.6/5 (211 reviews)
Ping Identity

Ping Identity’s Autonomous Identity capability leverages machine learning to analyze Trello permissions across the organization, identifying access blind spots that traditional review processes miss. The system evaluates millions of permissions and provides contextual insights that categorize Trello access as low, medium, or high risk based on actual usage patterns and peer comparisons. This intelligence guides reviewers toward decisions that matter rather than rubber-stamping routine access.
The platform offers multiple certification types relevant to Trello governance, including application access certification for workspace memberships, entitlement certification for specific board permissions, and organizational-based certification for B2B partners managing their own users’ Trello access. Micro-certifications enable ad hoc reviews when situations demand immediate attention rather than waiting for the next scheduled campaign.
Ping Identity’s DaVinci orchestration platform connects Trello governance to 6,500+ capabilities across 350+ connectors, enabling sophisticated workflows that span multiple systems. When a Trello access review decision triggers remediation, DaVinci can orchestrate deprovisioning across related systems, update service desk tickets, and notify stakeholders through preferred channels. This level of automation reduces the manual work that typically follows certification campaigns.
Pros:
- AI-powered access intelligence evaluates permissions at enterprise scale
- Flexible deployment options including SaaS, private cloud, and on-premise
- Comprehensive compliance certifications support regulated industries
Cons:
- Complex initial setup requires significant IAM expertise
- Identity Governance purchased separately from core platform
- Higher costs create barriers for mid-market organizations
- Support response times vary during critical periods
Ratings: G2 4.5/5 (264 reviews) · Capterra 4.7/5 (39 reviews)
How to Choose
Selecting the right platform for Trello access reviews depends on your organization’s broader identity governance strategy. If Trello represents one application among many cloud tools requiring governance, platforms like Torii that combine SaaS management with identity governance provide unified visibility without deploying multiple solutions. Organizations already standardized on Okta for authentication naturally extend to Okta Identity Governance for consistent user experiences.
Enterprises with significant SAP investments should evaluate SAP Cloud IAG for its native ecosystem integration, while those running hybrid environments with substantial Active Directory infrastructure may find One Identity or Ping Identity better suited to their architecture. Saviynt and Omada both excel at compliance-driven governance, with Saviynt offering stronger AI automation and Omada providing faster deployment timelines.
Torii stands out for combining shadow IT discovery, automated access reviews, and AI-powered governance in a platform that deploys in weeks rather than months. The ability to discover unauthorized Trello workspaces alongside sanctioned deployments addresses a gap that pure IGA tools often miss, while workflow automation handles remediation without creating additional manual work.
Budget considerations matter significantly in this space. Enterprise IGA platforms from SAP, One Identity, and Ping Identity carry substantial licensing and implementation costs that may exceed mid-market budgets. Saviynt positions itself as more affordable than traditional IGA leaders while maintaining enterprise capabilities. Torii’s per-employee pricing model scales predictably and avoids the surprise costs that often accompany governance implementations.
The right choice ultimately depends on whether you need Trello governance as a standalone initiative or as part of broader SaaS visibility. For most organizations dealing with application sprawl across dozens or hundreds of cloud tools, integrated platforms that handle discovery, management, and governance together provide better outcomes than deploying separate point solutions for each concern.
Frequently Asked Questions
Trello's board-level membership model and ad hoc sharing let boards multiply across teams and external collaborators. Permissions don't cascade predictably, so temporary admins, contractors, or former employees often retain access, causing unchecked permission creep and governance blind spots.
Access sprawl can expose strategic plans, unreleased feature roadmaps, and client deliverables to unauthorized users. It increases insider risk, complicates SOC 2 and ISO 27001 audits, and amplifies the impact of departed employees or third parties retaining lingering access.
Identity governance platforms automate access certifications, schedule event-driven reviews, and produce detailed audit trails that show who had board access and when. They flag inactive or orphaned accounts, run remediation workflows, and help satisfy compliance controls for auditors.
Discovery relies on API integrations, browser telemetry, procurement and billing records, and SaaS usage signals. Platforms like Torii combine these sources to surface shadow Trello workspaces, personal accounts, and unauthorized subscriptions that bypass standard procurement and governance.
Evaluate integration depth, discovery capabilities, automation for deprovisioning, reporting and audit trails, AI risk scoring, deployment options, and total cost of ownership. Choose based on whether you need broad SaaS visibility or focused, compliance-driven Trello governance.
Yes. Modern IGA and SaaS management platforms can revoke workspace memberships and board permissions automatically when certifications or event triggers occur. Remediation can be near real-time, integrated with ticketing and orchestration to update related systems and provide audit evidence.