LastPass Access Reviews: 9 Platforms to Consider in 2026

LastPass vaults store the credentials that unlock everything else in your organization. A single LastPass Business account typically holds saved passwords for dozens of SaaS applications, internal tools, and shared team resources. When that account belongs to someone who left the company three months ago and nobody revoked their access, every credential stored in that vault remains reachable. The stored passwords don’t expire just because the person’s employment did.
The 2022 LastPass breach made this risk tangible for thousands of organizations. Attackers exfiltrated encrypted vault backups after compromising a senior DevOps engineer’s personal computer through an unpatched Plex vulnerability, then used a keystroke logger to capture the master password that unlocked internal decryption keys. In March 2025, U.S. federal prosecutors linked a $150 million cryptocurrency heist to credential data stolen in that breach, with victims who had stored seed phrases in LastPass Secure Notes. That timeline turned LastPass access reviews from a compliance checkbox into an operational priority, because the consequences of unaudited vault access are still playing out years later.
LastPass Business supports four role tiers: User, Helpdesk Admin, Admin, and Super Admin, with separate shared folder permissions controlling who can view or edit stored credentials. SCIM provisioning is available through directory integrations with Okta, Azure AD, and OneLogin. Deprovisioning a user from the directory removes their LastPass account, but it does not automatically rotate the shared passwords they previously accessed. That gap means a structured access review needs to cover both account status and credential exposure. LastPass retains user activity logs for up to two years and offers 100+ configurable security policies, but there is no native periodic certification workflow built into the platform.
The nine platforms below each handle LastPass governance from a different angle. Some automate the identity lifecycle so orphaned accounts get caught before they become a problem. Others run formal certification campaigns where managers confirm who still needs access to shared vaults and admin consoles. Each section covers what the tool does for LastPass specifically, along with pricing context, integration depth, and review ratings.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| ConductorOne | ★★★ | ★★ | ★★ | ★ |
| Nudge Security | ★★★ | ★★ | ★ | ★ |
| Okta | ★★ | ★ | ★★ | ★★★ |
| SailPoint | ★ | ★ | ★★★ | ★★★ |
| Saviynt | ★★ | ★ | ★★★ | ★★ |
| MiniOrange | ★★ | ★★★ | ★ | ★★ |
| Ping Identity | ★ | ★ | ★★★ | ★★ |
| Avatier | ★★ | ★★ | ★★ | ★★ |
Table of Contents
- Torii
- ConductorOne
- Nudge Security
- Okta Lifecycle Management
- SailPoint IdentityIQ
- Saviynt
- MiniOrange
- Ping Identity
Torii
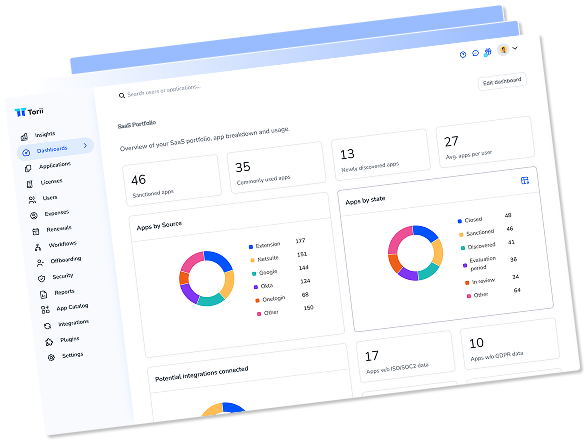
Torii pulls employee name, email, title, department, user status, last-used date, license status, and license type data directly from LastPass Business accounts. That level of detail matters for password manager governance because the risk profile of a LastPass account depends heavily on who owns it and what they do. An engineering manager with shared folder access to infrastructure credentials carries a fundamentally different risk than a marketing coordinator who uses LastPass for social media logins. Torii makes those distinctions visible automatically so reviewers don’t have to cross-reference HR data with the LastPass admin console.
The last-used date field is particularly useful for LastPass reviews. Password managers tend to accumulate dormant accounts faster than most SaaS tools because people stop logging into LastPass directly once their browser extension is set up, or they switch to a different credential manager without telling IT. Torii flags those inactive accounts and routes them into the access review workflow, where a manager can confirm whether the person still needs a LastPass seat or whether the license can be reclaimed. The automated license reclamation workflow saves money on per-seat LastPass Business costs, which run $7 per user per month on the Business plan.
Torii’s AI engine monitors access patterns across the full SaaS stack, not just LastPass in isolation. If a user’s LastPass account shows credentials stored for applications they no longer access through SSO, the system flags that mismatch. That cross-application visibility is where a combined SaaS management and identity governance platform outperforms tools that treat each app as a standalone review target. Torii is a 2025 Gartner Magic Quadrant Leader for SaaS Management Platforms with a 4.5-star G2 rating across 302 reviews.
Pros:
- Pulls name, email, title, department, status, last-used date, and license data from LastPass for contextual reviews
- AI detects anomalous access patterns across the full SaaS stack and flags credential mismatches
- Automated license reclamation identifies unused LastPass seats to reduce per-user spending
- Combined SaaS management and identity governance in one platform with 170+ integrations
Cons:
- Not the lowest-cost option; positioned for mid-market and enterprise organizations
- Cloud and SaaS focused with no on-premise deployment option
G2 Rating: 4.5/5 (302 reviews) · Capterra Rating: 4.9/5 (26 reviews)
ConductorOne
ConductorOne’s Identity Graph maps every LastPass account to its owner’s full access profile across your SaaS environment. That context changes how reviewers think about a LastPass certification, because a LastPass admin account tied to someone who also has privileged access in AWS and Salesforce represents a different risk than an admin account held by someone with limited access elsewhere. The platform builds that relationship view automatically through its 300+ pre-built connectors, and the LastPass review becomes part of a broader identity certification rather than an isolated exercise.
The AI agents in ConductorOne handle routine LastPass certifications without manual intervention. When an account matches the expected access pattern for its owner’s role and department, the system auto-approves and logs the decision. Accounts that deviate from the pattern, such as a junior employee with admin privileges or someone in a non-technical department holding shared credentials for infrastructure tools, surface for human review. PriceSmart reported reducing their overall review cycle from three months to two weeks using this approach, and that efficiency gain compounds when you’re certifying LastPass alongside 50 or 100 other applications in the same campaign.
ConductorOne also offers just-in-time access for LastPass admin privileges. Rather than granting permanent admin status to everyone who occasionally needs to manage shared folders or reset another user’s account, the platform converts those standing privileges into time-bound access requests. That model reduces the number of LastPass admin accounts that need to be reviewed in the first place. Visit ConductorOne for more information.
Pros:
- AI agents auto-certify low-risk LastPass accounts and escalate exceptions for human review
- Just-in-time access converts permanent LastPass admin privileges to time-bound requests
- 300+ connectors provide cross-application context for each LastPass account review
Cons:
- No public pricing; enterprise sales engagement required for budgeting
- Only 13 G2 reviews limits peer validation compared to established vendors
- Can only revoke access in reviews, not modify permission levels
G2 Rating: 4.8/5 (13 reviews)
Nudge Security
LastPass accounts created outside of IT’s provisioning process are a common source of governance gaps. Employees sign up for personal LastPass accounts using their work email, store company credentials in those unmanaged vaults, and nobody in IT knows the accounts exist. Nudge Security’s patented email-based discovery method catches those shadow LastPass accounts by scanning account creation confirmations and login notifications, delivering visibility into the full LastPass footprint within about 75 minutes of connecting the platform.
The behavioral nudge approach works well for LastPass environments where the primary risk is accumulation rather than malice. When Nudge identifies a LastPass account tied to a former employee or someone who hasn’t logged in for 90 days, it sends an automated prompt through Slack or email asking whether the account is still needed. Those nudges achieve an 83% compliance rate, and the responses feed directly into the review record. For organizations where the goal is cleaning up orphaned LastPass accounts rather than producing formal SOX attestation reports, that lightweight approach gets results without the overhead of a full certification campaign.
The offboarding playbook is where Nudge Security delivers the most value for LastPass governance. When someone leaves the organization, the playbook pulls up every SaaS account associated with their email address, including any personal or shadow LastPass accounts. The deprovisioning team sees the complete picture and can ensure that vault access is terminated alongside the person’s other accounts. Nudge also monitors for supply chain breaches, so if a SaaS vendor whose credentials are stored in your organization’s LastPass vaults reports an incident, you get an alert.
Pros:
- Discovers shadow LastPass accounts created outside IT’s visibility through email-based scanning
- Offboarding playbook catches all LastPass access for departing employees, including personal accounts
- Supply chain breach alerts flag risks in vendors whose credentials are stored in LastPass vaults
Cons:
- Requires Google Workspace or Microsoft 365 for email-based discovery to work
- Nudges are behavioral prompts, not mandatory enforcement; users can ignore them
- Very limited public review data makes peer validation difficult
G2 Rating: 5.0/5 (limited reviews) · Gartner Rating: 4.7/5 (22 reviews)
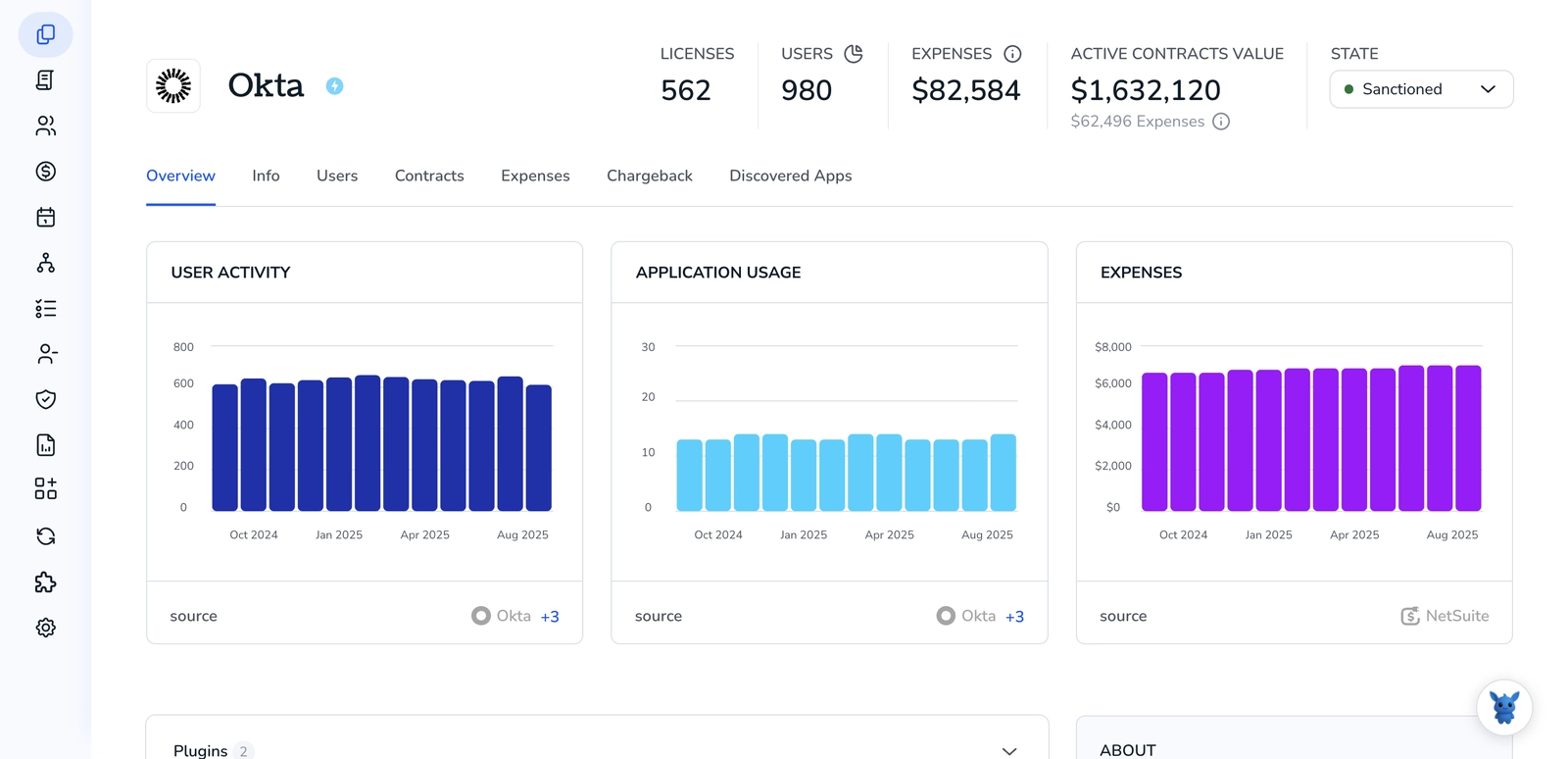
Okta Lifecycle Management
Super Admin accounts with full control over vault policies and user management. Admin accounts that can manage users and shared folders but cannot change organization-wide settings. Helpdesk Admin accounts with customizable permissions for day-to-day support tasks like password resets. Regular user accounts with access to personal and shared vaults. Shared folder permissions that grant read or read-write access to team credential stores. An effective review needs to audit both the account-level role and the shared folder memberships, since a regular user with write access to an infrastructure credentials folder may carry more risk than their role title suggests. Admins also cannot see what credentials users store by design, which makes external governance tooling the only way to correlate vault access with actual job requirements.
Okta’s LastPass integration handles user provisioning and deprovisioning through SCIM, which means adding or removing someone from a LastPass group in Okta automatically updates their account status in LastPass Business. The Identity Governance module (OIG) extends that lifecycle automation into structured access certifications. Reviewers see each LastPass account alongside its owner’s broader application access, and the certification campaign can cover LastPass as one of dozens of applications in a single review cycle.
The 2025 Security Access Reviews feature adds event-triggered reviews that fire when specific conditions are met, rather than waiting for the next quarterly campaign. If Okta detects that a LastPass account was added to a high-privilege group or that an account hasn’t been used in the expected timeframe, it can trigger a targeted review of that specific account. AI-generated access summaries give reviewers a plain-language overview of what each person’s LastPass account looks like relative to their peers, which cuts the time spent investigating each certification item.
With 7,000+ pre-built integrations in the Okta Integration Network, the platform connects to nearly everything else in the stack. That breadth makes it straightforward to include LastPass in a unified certification program covering your full application portfolio. Root Insurance reported saving over 100 hours annually on certification campaigns through Okta Workflows automation.
Pros:
- SCIM integration automates LastPass user provisioning and deprovisioning through Okta directory
- Event-triggered Security Access Reviews catch LastPass changes between scheduled campaigns
- 7,000+ integrations enable unified certification across the full application portfolio
Cons:
- Identity Governance requires purchasing the full OIG bundle, not available standalone
- Group-based provisioning model limits fine-grained permission reviews within LastPass
- Pricing at $6-$17 per user per month before governance add-ons gets expensive at scale
G2 Rating: 4.5/5 (1,257 reviews) · Capterra Rating: 4.7/5 (914 reviews)
SailPoint IdentityIQ
SailPoint’s approach to LastPass governance centers on entitlement-level certification rather than binary account-level reviews. Instead of asking a reviewer to approve or revoke someone’s entire LastPass account, SailPoint can present the individual shared folder memberships and admin privileges for certification. That granularity matters for organizations where LastPass holds credentials segmented by department or sensitivity level, because a user might legitimately need access to the marketing credentials folder but not the infrastructure passwords folder.
The peer group analysis engine is where SailPoint adds the most value for LastPass reviews. The ML algorithms compare each user’s LastPass access profile against others in similar roles and departments. A finance analyst with shared folder access to engineering infrastructure credentials gets flagged as an outlier immediately, while standard access patterns for that role get recommended for approval. SailPoint reports that this approach reduces rubber-stamping, where overwhelmed reviewers approve everything because they don’t have the context to make informed decisions.
SailPoint connects to LastPass through its connector library and supports both the cloud-based Identity Security Cloud and the on-premises IdentityIQ deployment. For organizations running LastPass alongside on-premises Active Directory environments, that hybrid support means a single governance platform covers both cloud and legacy infrastructure. SailPoint has been named a Leader in every Gartner Magic Quadrant for IGA published and serves 53% of Fortune 500 companies. Learn more at SailPoint.
Pros:
- Entitlement-level certifications review individual LastPass folder memberships, not just account status
- Peer group analysis flags users with unusual LastPass access relative to similar roles
- Hybrid deployment supports organizations governing LastPass alongside on-premises systems
Cons:
- Average annual cost of approximately $240,000 makes SailPoint prohibitive for mid-market teams
- Implementations typically take 6-12 months with professional services that can double the software cost
- Configuration complexity requires specialized IAM expertise that many organizations lack
G2 Rating: 4.5/5 (161 reviews) · Capterra Rating: 4.2/5 (21 reviews)
Saviynt
Saviynt’s continuous compliance monitoring applies to LastPass accounts in real time rather than on a fixed schedule. When a LastPass user gets promoted to admin status or gains access to a new shared credential folder, Saviynt can trigger a micro-certification targeting that specific change instead of waiting for the next quarterly review. For LastPass environments where shared folder permissions shift frequently as teams reorganize, that event-driven model catches access drift that periodic campaigns would miss entirely.
The AI trust scoring system evaluates each LastPass account against expected access patterns and auto-approves low-risk certifications. Saviynt reports that trust scoring reduces the manual review burden by up to 75% and predicts correct decisions with 94% accuracy based on peer group analysis. A regular LastPass user with standard shared folder access matching their department gets processed automatically, while an account with admin privileges or access to credential folders outside the owner’s job function gets routed to a human reviewer. That separation keeps LastPass reviews focused on the accounts that actually warrant scrutiny.
Saviynt’s unified IGA and privileged access management architecture is relevant for LastPass governance because LastPass admin accounts qualify as privileged. Those accounts can export vault data, manage other users, and modify organizational security policies. Governing them through the same platform that handles your other privileged accounts creates consistent policy enforcement. Saviynt raised $700 million at a $3 billion valuation and has been named Gartner Peer Insights Customers’ Choice for IGA four consecutive years.
Pros:
- Continuous compliance catches LastPass admin changes and folder permission shifts in real time
- AI trust scoring auto-resolves low-risk LastPass certifications with 94% prediction accuracy
- Unified IGA and PAM governs both standard LastPass users and privileged admin accounts
Cons:
- Customer support receives mixed reviews, with some reporting tickets that stay open too long
- Backend configuration is complex despite a modern frontend, requiring specialized expertise
- Starting at $10,000 annually creates a cost barrier for smaller organizations
G2 Rating: 3.5/5 (limited reviews) · Capterra Rating: 4.5/5 (2 reviews) · Gartner Rating: 4.8/5 (185 reviews)
MiniOrange

MiniOrange takes a different position in the LastPass governance landscape by focusing on the SSO and authentication layer rather than deep identity governance. The platform can sit in front of LastPass as an SSO provider, giving organizations centralized control over who can authenticate into LastPass Business and under what conditions. That setup adds adaptive risk-based authentication to LastPass logins, evaluating factors like device posture, IP reputation, and geographic location before granting access to the vault. For organizations that want to tighten the front door to LastPass without deploying a full IGA platform, that authentication-layer approach covers the most immediate risk.
The SCIM provisioning gateway automates LastPass user lifecycle management through MiniOrange’s directory integration. New hires get provisioned into LastPass when they appear in the connected HR system or directory, and departing employees get deprovisioned automatically when their directory status changes. That automation eliminates the manual LastPass admin console work that creates gaps when someone forgets to remove a user. The bi-directional sync keeps LastPass account status aligned with the source of truth in your identity provider.
At $2-$3 per user per month, MiniOrange is significantly less expensive than most platforms in this comparison. That pricing makes it practical for organizations running LastPass Business with 50-500 users where a $75,000+ SailPoint deployment doesn’t make sense. The platform supports 6,000+ pre-built integrations and provides audit logs exportable in CSV, JSON, and PDF formats for compliance documentation. MiniOrange is a Gartner “Strong Performer” in the 2025 Voice of the Customer report for Identity and Access Management.
Pros:
- Adaptive risk-based authentication adds contextual security to LastPass login attempts
- SCIM provisioning automates LastPass user creation and deprovisioning through directory sync
- Pricing at $2-$3 per user per month makes it accessible for smaller LastPass deployments
Cons:
- Access review capabilities are limited compared to dedicated IGA platforms; primary governance app requires Jira
- Customer support quality varies significantly between experiences
- Lacks the AI-driven access analytics and peer group analysis found in specialized IGA tools
G2 Rating: 4.5/5 (264 reviews) · Capterra Rating: 4.5/5 (36 reviews)
Ping Identity

Ping Identity’s Autonomous Identity module applies machine learning to LastPass account data alongside the rest of your identity ecosystem. The system evaluates millions of permissions per minute and categorizes each LastPass account as low, medium, or high risk based on the user’s overall access profile, behavioral patterns, and peer group comparison. LastPass admin accounts that hold broader organizational privileges than similar roles typically carry are flagged automatically, and reviewers can focus their time on those high-risk accounts while the AI handles routine certifications.
The certification campaign framework supports multiple review types relevant to LastPass governance. Application access certification reviews all accounts in LastPass at once. Role membership certification validates that users assigned to LastPass admin or power user groups still belong there. Entitlement certification drills into specific shared folder permissions within LastPass. Micro-certifications handle ad hoc reviews triggered by events like a role change or a new shared folder assignment. That flexibility means the review process can match the specific LastPass governance requirements rather than forcing everything through a single campaign type.
Ping Identity serves 60% of Fortune 100 companies and holds nine consecutive years as a Gartner Magic Quadrant Leader for Access Management. The platform’s DaVinci orchestration engine connects to 350+ services with 6,500+ orchestrated capabilities. The hybrid deployment model supports cloud, on-premises, private cloud, and FedRAMP environments, which matters for organizations in regulated industries that need to govern LastPass within strict infrastructure requirements. More details at Ping Identity.
Pros:
- Autonomous Identity ML evaluates LastPass accounts against millions of permissions for risk scoring
- Multiple certification types cover account access, role membership, and folder-level entitlements
- Hybrid deployment flexibility including FedRAMP for regulated industries
Cons:
- Complex initial setup requiring specialized IAM expertise extends deployment timelines
- PingOne Identity Governance must be purchased separately from the core platform
- Starting at $16,000-$35,000 annually plus implementation costs puts it beyond most mid-market budgets
G2 Rating: 4.5/5 (264 reviews) · Capterra Rating: 4.7/5 (39 reviews)
Avatier

Avatier’s Identity Anywhere platform brings a password management background to the LastPass governance problem. The company built its reputation on reducing help desk calls related to password resets and access requests, and that expertise translates into practical LastPass access review capabilities. The Access Certification Snapshot creates a governance project that captures the current state of all LastPass accounts, their role assignments, and shared folder memberships for structured review. Delta Access Certification then narrows subsequent reviews to only the accounts and permissions that changed since the last snapshot, which reduces the review burden dramatically for stable LastPass environments.
The multi-channel reviewer experience sets Avatier apart for organizations where LastPass certification approvals need to happen quickly. Managers can review and approve LastPass access certifications through iOS, Android, Microsoft Teams, Outlook, Slack, ServiceNow, or SMS. That flexibility means a department head traveling for a conference can complete their LastPass certification from their phone rather than delaying the entire campaign until they’re back at a desk. Push notification workflows keep the review moving across platforms without requiring reviewers to log into a separate governance portal.
Avatier’s containerized Docker architecture lets the platform run on any cloud provider, on-premises, or in hybrid configurations without vendor lock-in. That deployment flexibility is relevant for organizations that chose LastPass specifically to avoid being locked into a single ecosystem and want the same freedom in their governance tooling. Avatier reports a 97% customer satisfaction rate and offers fixed-bid implementations that eliminate the professional services cost surprises common with enterprise IGA deployments.
Pros:
- Delta Access Certification reviews only changed LastPass accounts and permissions since the last audit
- Multi-channel approval through Teams, Slack, mobile, and SMS keeps reviews on schedule
- Fixed-bid implementations eliminate professional services cost overruns
Cons:
- Interface can overwhelm new users; training and phased rollout is recommended
- Only 0.04% IAM market share limits brand recognition and community resources
- Not listed in Gartner Magic Quadrants, which can complicate procurement approval processes
G2 Rating: 4.6/5 (31 reviews)
How to Choose the Right LastPass Access Review Tool
Selecting a governance platform for LastPass depends on where the biggest gap exists in your current process. If the primary problem is orphaned accounts and shadow LastPass usage that IT can’t see, Nudge Security’s email-based discovery finds those accounts faster than any other platform here. If the organization needs formal certification campaigns with audit trails for SOX or SOC 2 compliance, SailPoint and Saviynt provide the structured workflows that auditors expect.
For teams managing LastPass alongside a broader SaaS portfolio, Torii is the strongest starting point. It pulls more contextual data from LastPass than most governance tools, including last-used dates and license types that directly inform access and cost optimization decisions. The AI-driven anomaly detection works across your full application stack, so LastPass reviews benefit from cross-application intelligence rather than operating in a silo. Torii holds 2025 Gartner Magic Quadrant Leader recognition for SaaS Management Platforms, and pricing starts at $2.50 per employee per month, which keeps it accessible for mid-market organizations that aren’t ready for a six-figure IGA investment.
Confirm whether your organization runs LastPass Business ($7/user/month) or Enterprise ($10/user/month), because the available admin controls differ. Enterprise includes advanced SSO and MFA policies, an admin console API, SIEM integrations, and customizable security policies. Business plans support SCIM provisioning through select directory integrations but lack the deeper policy controls. Knowing your plan tier determines which external governance tools can pull data and which will need manual exports from the admin console to complete a review.
Budget is the fastest way to narrow the field. MiniOrange and Avatier serve organizations where the LastPass deployment is mid-sized and the governance budget is constrained. ConductorOne and Nudge Security occupy the modern mid-market with faster deployment and AI-assisted reviews. Okta makes sense when LastPass is already managed through Okta SSO and you want governance added to an existing identity platform. SailPoint, Saviynt, and Ping Identity are enterprise-grade platforms for organizations governing LastPass as part of a complex, regulated identity environment spanning hundreds of applications.
Frequently Asked Questions
A: LastPass vaults centralize credentials; orphaned or ex-employee accounts can retain access indefinitely. The 2022 breach and later crypto heist showed real-world impact. Because LastPass lacks built-in certification workflows and deprovisioning doesn’t rotate shared passwords, structured reviews are essential.
A: Audit Super Admins, Admins, Helpdesk Admins, regular users, and shared folder memberships. Review both account roles and folder-level entitlements because a nominally low-privilege user with write access to critical shared vaults may carry outsized risk.
A: No. SCIM deprovisioning removes the LastPass account but does not automatically rotate or revoke shared passwords that the user previously accessed. A structured access review or rotation workflow must cover both account termination and credential rotation to close that gap.
A: Use discovery tools that scan corporate email notifications and login confirmations to find shadow LastPass accounts. Nudge Security's email-based discovery identifies unmanaged vaults quickly and feeds responses into offboarding playbooks, but it requires Google Workspace or Microsoft 365 for email scanning to work.
A: Look for SCIM provisioning, entitlement-level certifications, event-triggered micro-certifications, AI trust scoring or peer-group analysis, just-in-time admin access, and hybrid deployment support. Those features ensure LastPass reviews cover lifecycle automation, granular folder permissions, risk scoring, and compliance requirements.
A: Start by identifying your biggest gap: orphaned accounts, shadow usage, formal SOX attestations, or cross-app visibility. Match budget and scale to vendors: MiniOrange or Avatier for constrained budgets; Torii for SaaS-wide visibility; SailPoint, Saviynt, or Ping for large regulated environments.