Enterprise Marketo Access Management: 6 Solutions in 2026

Marketo access control is one of those areas where problems accumulate slowly and surface all at once. The platform sits at the intersection of customer data, campaign automation, and revenue pipeline, and its user permissions model has grown more layered since Adobe acquired Marketo Engage and migrated access management to the Adobe Admin Console.
Access tends to accumulate in marketing automation tools quietly, well outside normal visibility. An ops contractor gets admin credentials for a campaign launch, that role persists through an organizational restructure, and three years later the account is still active when your security team pulls a Marketo user list ahead of a SOC 2 audit. Marketo’s role structure spans full administrator privileges down to narrow custom read-only configurations, and the gap between what users need and what they actually have tends to widen between review cycles.
The six platforms in this article all handle Marketo access certification in different ways. Some connect via SCIM and pull granular entitlement data; others work through REST API or SSO-based identity tracking. Each section addresses what the platform does specifically for Marketo governance, not just general IGA capabilities.
Administrator accounts with full platform access, standard user roles scoped to specific workspaces or programs, custom roles built for agency partners or contractors, API-only users tied to integrations, and service accounts used by third-party tools connecting via the Marketo REST API. The Adobe Admin Console now manages authentication for Marketo Engage instances, so access reviews should account for both the Marketo role layer and the Adobe IMS user layer.
The comparison below covers integration depth, AI review capabilities, limitations, and ratings from major review platforms.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| Lumos | ★★ | ★★ | ★★★ | ★ |
| SailPoint IdentityIQ | ★ | ★ | ★★★ | ★★★ |
| Oracle Identity Governance | ★ | ★ | ★★ | ★★ |
| Omada Identity | ★★ | ★★ | ★★ | ★★ |
| Avatier | ★★ | ★★★ | ★★ | ★ |
Table of Contents
Torii
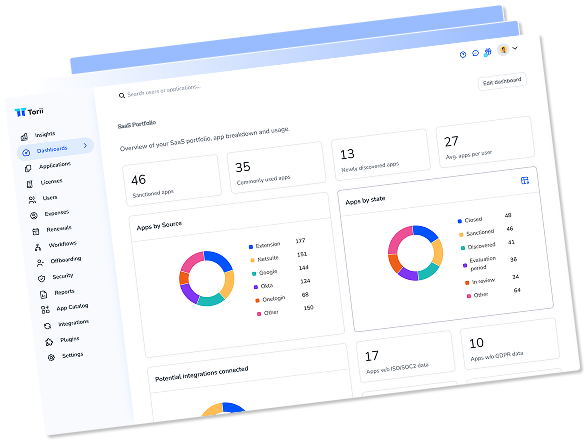
Torii approaches Marketo access reviews as part of a broader SaaS governance picture rather than as an isolated certification exercise. The platform connects to Marketo through a direct integration and captures employee name, email, title, department, user status, last used date, license assignment, and license type for each account. That breadth of context is significant for Marketo specifically, where a user’s organizational role should determine what they can do inside campaign workspaces, not just whether they have an active license.
The field-level data matters most when identifying accounts that have drifted out of alignment with an employee’s current role. Seeing that a user’s department changed six months ago but their Marketo admin access never got adjusted, or that an account with workspace-level permissions belongs to a contractor whose employment ended, gives reviewers the data to make a real decision rather than clicking through a list of usernames. Torii’s AI flags unusual access patterns and routes certification requests to the correct app owner or manager automatically, which reduces the back-and-forth that typically slows Marketo review campaigns.
Torii is the only platform in this comparison that combines identity governance with SaaS spend management in the same interface. For organizations where Marketo sits alongside 50 or 100 other SaaS tools, that eliminates the need to run separate processes for access reviews and license optimization. The audit trail is retained automatically for compliance evidence, simplifying SOC 2 reporting cycles for organizations that include Marketo in scope. Torii’s 2025 Gartner Magic Quadrant Leader recognition for SaaS Management Platforms reflects its position as a mature choice for cloud-first IT teams.
Pros:
- Captures Marketo account context including status, last used date, department, and license type
- AI-powered anomaly detection flags role creep and unusual permission patterns
- In-place attestations with automated reviewer routing reduce campaign completion times
- Unified SaaS management and identity governance in one platform
Cons:
- Pricing positions it above entry-level SaaS governance tools
- No on-premise deployment; built for cloud/SaaS environments only
G2 Rating: 4.5/5 (302 reviews) · Capterra Rating: 4.9/5 (26 reviews)
Lumos
Lumos is built around the idea that most access reviews waste time on obvious decisions. Its Albus AI agent handles routine certification judgments automatically by comparing a user’s Marketo access against peer group benchmarks and actual usage patterns, so reviewers focus on anomalies rather than approving clear-cut cases one by one. For Marketo environments with large marketing ops teams that turn over regularly, that filtering saves real time across recurring quarterly campaigns.
The Delta Reviews feature is worth calling out for recurring Marketo certification cycles. Instead of reviewing every account in the instance each quarter, Delta Reviews surface only what changed since the last campaign ran, a meaningful reduction in reviewer burden for instances where the core user base is stable but individual permissions shift during campaign launches and agency onboarding cycles. Lumos also supports self-service access requests via Slack and Teams integrations, which reduces the IT ticket volume for routine Marketo role assignments without requiring employees to navigate a separate governance portal.
The platform deploys in days rather than months, which is a genuine differentiator for organizations that need structured Marketo governance in place quickly. Lumos has fewer independent customer reviews than established enterprise IGA vendors, but its Gartner Peer Insights rating of 4.7 across 47 reviews reflects strong satisfaction among enterprise customers that have adopted it.
Pros:
- Albus AI agent handles routine Marketo certification decisions automatically, cutting reviewer time significantly
- Delta Reviews target only changed access since the last cycle, reducing quarterly campaign overhead
- Fast deployment timeline compared to traditional enterprise IGA platforms
Cons:
- Fewer published reviews than larger vendors; less external peer validation available
- No live chat support; implementation questions get resolved asynchronously
- Custom connectors for specialized Marketo configurations take longer to set up than core integrations
G2 Rating: 4.7/5 (54 reviews)
SailPoint IdentityIQ
SailPoint IdentityIQ handles Marketo access reviews through its connector ecosystem, and at 1,100+ enterprise application connectors, Marketo fits into a much larger governance framework. The peer group analysis is particularly applicable to large Marketo environments, where access levels across campaign managers, automation builders, and admin users can be hard to benchmark without a structured comparison point. SailPoint’s AI identifies users who have accumulated more access than their cohort and flags them for review, which directly addresses the role creep problem in long-running Marketo instances.
For enterprises where Marketo is one of a dozen platforms under governance, SailPoint’s breadth is a practical advantage. Running Marketo certification campaigns alongside Salesforce, Workday, and Active Directory under a single compliance program eliminates the operational fragmentation of managing separate review processes per application. SailPoint holds a six-time consecutive Gartner Magic Quadrant Leader position for IGA, and 53% of Fortune 500 companies use it, figures that reflect genuine capability at enterprise scale.
Administrator privileges in Marketo Engage grant access to workspace configuration, lead database management, user provisioning, API credential management, and campaign folder permissions across the entire instance. Organizations running large-scale demand generation programs often find their admin-to-standard-user ratio higher than expected, particularly after agency onboarding cycles, acquisitions, or multi-year platform expansions where access was never systematically reviewed.
The IdentityIQ platform is a difficult choice to justify for organizations primarily focused on Marketo governance. Implementations run six to twelve months, entry pricing starts at $75,000, and the professional services investment often matches the software license cost. Organizations without dedicated IAM engineering teams generally find the complexity exceeds what Marketo access management requires.
Pros:
- Peer group analysis identifies Marketo admin role creep across large user populations
- Handles Marketo certifications alongside every other enterprise system under one compliance program
- Deepest entitlement modeling available for complex permission structures
Cons:
- Six to twelve month implementation timelines limit deployment flexibility
- Entry pricing of $75,000+ excludes most mid-market organizations
- Requires dedicated IAM engineering expertise to maintain and customize effectively
G2 Rating: 4.5/5 (161 reviews) · Capterra Rating: 4.2/5 (21 reviews)
Oracle Identity Governance

Oracle Identity Governance connects to Marketo through REST API and third-party connector configurations, making it a reasonable option for organizations already running Oracle’s broader ecosystem that want their marketing automation platform governed alongside other enterprise applications. The event-based micro-certifications are directly relevant for Marketo: when a user’s job code changes, they transfer departments, or an org restructure occurs, OIG triggers an automatic access review for that user’s Marketo permissions without waiting for the next scheduled campaign cycle.
The Oracle Identity Role Intelligence feature uses machine learning to identify access patterns across the Marketo user population and suggest role structures that reflect actual usage rather than accumulated permissions over time. For large organizations where Marketo workspaces have grown through acquisitions or team expansions, that analytical layer can surface cleanup opportunities that would require significant manual analysis otherwise. SOX compliance templates and detailed audit trails support organizations that include Marketo in their revenue operations audit scope.
Oracle Identity Governance is realistically best suited for organizations already invested in Oracle infrastructure. Deploying OIG specifically to govern Marketo access is hard to justify given the implementation complexity, per-user pricing at $3,600, and the interface that reviewers consistently describe as dated compared to cloud-native alternatives. More detail on the platform’s governance capabilities is on Oracle’s site.
Pros:
- Event-based micro-certifications trigger Marketo reviews automatically when org changes occur
- Machine learning role intelligence identifies access patterns and cleanup opportunities
Cons:
- Complex implementation process; not suited for organizations without existing Oracle infrastructure
- Per-user pricing at $3,600 is high relative to alternatives with similar Marketo integration
- Interface is dated and less intuitive than newer cloud-native platforms
- Technical support quality receives consistent criticism across customer review platforms
G2 Rating: 3.8/5 (71 reviews) · Capterra Rating: 4.4/5 (7 reviews)
Omada Identity
Omada Identity connects to Marketo through pre-built connectors and REST API support, and its AI assistant “Javi” lets entitlement owners launch Marketo access reviews directly from Microsoft Teams without opening a separate governance portal. For marketing operations teams that work in Teams day-to-day, that workflow fits naturally into how they already operate. Completion rates on recurring certification campaigns tend to be higher when reviewers don’t need to context-switch to a dedicated governance platform.
The 12-week deployment guarantee sets Omada apart from most enterprise IGA platforms, where implementations typically run six months to a year. Omada’s Accelerator Package covers full deployment within that 12-week window, including Marketo connector setup and workflow configuration. That timeline matters for organizations building a Marketo governance program ahead of a scheduled audit. The 50+ pre-built compliance report templates address GDPR requirements that are particularly relevant to Marketo, since the platform holds customer data from across campaigns and its access controls directly affect data privacy compliance posture.
Omada’s platform performs best for organizations in regulated industries where compliance reporting demands are significant and the Microsoft ecosystem anchors day-to-day operations. The cloud version carries higher pricing than on-premise deployment, and organizations needing heavily customized reporting workflows may find the out-of-the-box templates less flexible than expected.
Pros:
- AI assistant (Javi) enables Marketo access reviews from within Microsoft Teams
- 12-week deployment guarantee is significantly faster than typical enterprise IGA timelines
- 50+ compliance templates cover GDPR, SOX, and other frameworks relevant to Marketo’s data scope
- Clean interface with straightforward user permission management
Cons:
- Cloud version carries notably higher pricing than on-premise deployment
- Reporting customization is more restrictive than the template count suggests
Gartner Peer Insights Rating: 4.6/5 (211 reviews)
Avatier

Avatier’s Identity Anywhere platform reaches Marketo through a connector library covering 90+ enterprise applications via REST API and SCIM 2.0. The Delta Access Certification feature handles recurring Marketo reviews by focusing only on accounts where something changed since the last audit, which cuts reviewer workload for instances where the core user base is stable but individual permissions shift regularly during campaign cycles. For Marketo environments supporting large marketing teams with agency contractors cycling in and out, reviewing only changed access is more practical than full quarterly audits.
The mobile certification capability is particularly relevant for Marketo governance. Marketing managers and program owners who are responsible for approving Marketo access but don’t sit at a desk typically avoid governance systems that require desktop logins. Avatier’s iOS and Android support, alongside native Microsoft Teams and Outlook integration, means those reviewers can certify Marketo access from wherever they’re working. The platform ships with HIPAA, SOX, and FISMA compliance support out of the box, covering the most common audit frameworks for Marketo users in healthcare and financial services.
Avatier’s pricing is among the more transparent in this category, starting at $1.50 to $5 per user per month with all-inclusive packages covering IGA, SSO, and password management together. That bundling removes the integration overhead of running separate tools for access governance and lifecycle management. The trade-off is limited market presence compared to SailPoint or Oracle, which can complicate procurement at organizations that require Gartner Magic Quadrant validation.
Pros:
- Delta Certification reviews only changed Marketo permissions, reducing recurring audit overhead
- Mobile-native for marketing managers who review access outside of traditional desktop environments
- All-in-one pricing covers IGA, SSO, and lifecycle management without separate licensing fees
Cons:
- Not featured in Gartner Magic Quadrant, which can complicate enterprise procurement processes
- Initial interface complexity requires structured onboarding and a phased rollout approach
G2 Rating: 4.6/5 (31 reviews)
How to Choose the Right Platform for Marketo Access Management
Marketo governance decisions generally come down to two factors: how many other systems you’re governing alongside Marketo, and how quickly you need production-ready access reviews running.
For IT and security teams managing a broad SaaS portfolio where Marketo sits alongside dozens of other applications, a platform that handles both SaaS financial governance and identity governance together makes operational sense. Torii fits that profile directly, particularly for mid-market organizations that want AI-driven shadow IT discovery, automated license remediation, and access certification without maintaining separate toolsets. The depth of Marketo field coverage and automated reviewer routing are practical advantages for teams running recurring compliance programs.
For large enterprises that require Marketo certification to sit inside an existing SailPoint or Oracle deployment alongside Active Directory, SAP, and financial systems, extending coverage to Marketo through the existing platform is often more efficient than introducing a new tool. Both handle the Marketo integration, though SailPoint requires significantly more upfront implementation investment.
Lumos and Omada both offer faster paths to production for organizations building a Marketo governance program from scratch. Lumos’s AI-driven automation reduces reviewer burden on recurring campaigns; Omada’s Teams-native workflow and 12-week deployment guarantee address two of the most common implementation obstacles. Avatier is worth evaluating for organizations that want all-in-one IT automation coverage with transparent per-user pricing and strong mobile reviewer support.
Pull your current Marketo user list and note how many accounts have administrator-level access versus standard or custom roles. Identify any API-only users tied to integrations and service accounts used by third-party tools. Check last-login dates for all accounts, particularly those tied to contractors or former employees. This inventory makes vendor demos significantly more productive and helps you gauge what field coverage and integration depth you actually need.
Frequently Asked Questions
Start by exporting your Marketo user list and Adobe IMS mapping. Review administrator counts, custom roles, API/service accounts, and last-login dates. Reconcile each account with current job function, remove stale access, and document attestations for SOC 2 and compliance evidence.
Include administrator accounts, standard and workspace-scoped roles, custom roles used by agencies or contractors, API-only users tied to integrations, and service accounts. Also verify the Adobe IMS user layer when authentication is managed through the Adobe Admin Console.
Platforms connect via SCIM, REST API, or SSO/Adobe IMS mapping. They vary by connector depth: whether they pull field-level entitlements, last-used dates, license types, support delta-change detection, or provide automated reviewer routing and audit trails.
AI flags unusual permission patterns and role creep, benchmarks users against peer groups, auto-approves routine cases, surfaces only changed accounts since the last campaign, and routes certification tasks to the correct owners to reduce reviewer burden and speed completion.
Choose a unified SaaS+IGA tool if Marketo sits among many cloud apps and you need license optimization plus access reviews. Pick enterprise IGA (SailPoint/Oracle) if you must govern Marketo alongside AD, SAP, and complex on-prem systems at large scale.
Export your Marketo accounts, count admin versus standard roles, identify API and service accounts, check last-login dates, and flag contractors or inactive users. This inventory helps test connector depth, required field coverage, delta reviews, and realistic demo scenarios.