Top 9 Freshdesk Access Review Solutions in 2026

Freshdesk holds more sensitive data than most teams account for during access reviews. Every customer ticket is a record of a conversation, often containing names, contact details, internal escalation notes, and in some industries, account numbers or health information. The platform’s agent-based licensing model means anyone provisioned as a Freshdesk agent can view open and closed tickets, access the full ticket history, and export conversation data depending on their role configuration.
Most Freshdesk environments accumulate access risk the same way: agents who left the company six months ago still have active accounts, contractors were given full-agent status to handle a seasonal spike and were never removed, and a half-dozen internal team members from product or marketing were added during a customer escalation and never revisited. None of those situations appear in a standard Freshdesk admin dashboard in a way that prompts action without a structured access review process.
All nine platforms in this article approach Freshdesk access governance differently. Some focus on identity lifecycle automation and catch orphaned accounts before they become a compliance problem. Others run structured certification campaigns that give managers a formal process for confirming who still needs access. Each section covers what the platform does for Freshdesk specifically, not just general IGA capabilities.
Active agent accounts tied to employees who have left the organization; contractor and temporary agent access that was never time-limited; role assignments that grant ticket visibility beyond what a user's current function requires; admin accounts that have accumulated over time without a regular review process; API key holders with programmatic access to customer ticket data; and collaborator accounts with external or cross-team visibility into support queues.
The comparison below covers integration depth, AI capabilities, limitations, and ratings from G2, Capterra, and Gartner.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| Nudge Security | ★★★ | ★★★ | ★ | ★ |
| Lumos | ★★ | ★★ | ★★★ | ★ |
| Zluri | ★★ | ★★ | ★★ | ★★ |
| Okta Lifecycle Management | ★★ | ★ | ★★★ | ★★ |
| Oracle Identity Governance | ★ | ★ | ★★ | ★★ |
| Omada Identity | ★★ | ★★ | ★★ | ★★ |
| MiniOrange | ★★★ | ★★★ | ★ | ★ |
| Ping Identity | ★ | ★★ | ★★★ | ★★ |
Table of Contents
- Torii
- Nudge Security
- Lumos
- Zluri
- Okta Lifecycle Management
- Oracle Identity Governance
- Omada Identity
- MiniOrange
Torii
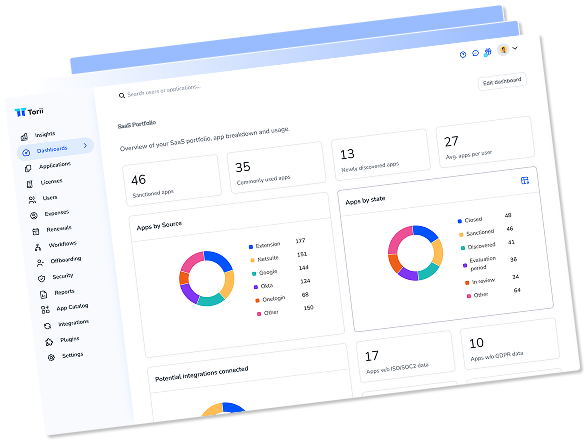
Torii pulls Freshdesk user data directly through its integration, giving reviewers visibility into employee name, email, title, department, user status, license assignment, and license type without requiring manual exports or spreadsheet reconciliation. For Freshdesk environments where the difference between a full agent and a collaborator carries real data access implications, that license type detail matters. A collaborator account might have visibility into specific ticket groups, while a full-agent license opens access to the complete queue. Torii surfaces those distinctions as part of the standard access review workflow.
The platform doesn’t currently sync last-activity date or historical usage data for Freshdesk, which means inactivity-based reviews require combining Torii’s identity data with Freshdesk’s own reporting exports. That said, the organizational data Torii does pull, particularly employee status and department, is often sufficient to catch the most common access problems in Freshdesk environments: accounts for departed employees, agents whose department changed but whose Freshdesk access was never updated, and users who hold license types that no longer match their current role.
Torii combines identity governance with SaaS management in one platform, which matters for teams managing Freshdesk alongside 50 or more other applications. Its AI flags anomalous access patterns across the full SaaS stack, and the automated license reclamation workflow identifies unused Freshdesk agent seats driving unnecessary per-seat costs. Torii holds 2025 Gartner Magic Quadrant Leader recognition for SaaS Management Platforms with a 4.5-star rating on G2 across 302 reviews.
Pros:
- Pulls employee name, email, title, department, status, and license type from Freshdesk directly
- AI flags access anomalies and routes certification requests to the right app owner automatically
- Automated license reclamation identifies idle Freshdesk agent seats to reduce per-seat costs
- Unified identity governance and SaaS management in one platform
Cons:
- Positioned above entry-level options; not the lowest-cost tool in this comparison
- No on-premise deployment; built exclusively for cloud and SaaS environments
G2 Rating: 4.5/5 (302 reviews) · Capterra Rating: 4.9/5 (26 reviews)
Nudge Security
Nudge Security’s email-based discovery finds Freshdesk accounts that organizations don’t know they have. Beyond the agent accounts tracked in the official admin panel, Nudge can surface contractor logins tied to personal Google accounts, shared credentials used by support outsourcing partners, and individual accounts created by employees who signed up for a Freshdesk free trial independently. That shadow account problem is more common in customer support contexts than most IT teams realize, particularly at companies that scaled their support function quickly and relied on self-service Freshdesk signup flows.
The access review workflow centers on behavioral nudges rather than formal certification campaigns. When Nudge identifies a Freshdesk agent account that appears inactive or tied to a user who no longer exists in the identity provider, it sends an automated prompt via Slack or email asking the account owner to confirm whether the access is still needed. Those prompts achieve an 83% compliance rate according to Nudge’s published data, which compares favorably to manual deprovisioning processes that depend on offboarding checklists being followed consistently.
Nudge Security works best as an early-warning system for SaaS account proliferation. It covers Freshdesk as part of discovering your full SaaS ecosystem, and its pre-built playbooks for offboarding and quarterly account cleanup apply equally to Freshdesk as to any other application the platform discovers. The Nudge Security platform requires Google Workspace or Microsoft 365 as the email source for discovery. Gartner Peer Insights rates the platform at 4.7 out of 5 across 22 reviews.
Pros:
- Discovers shadow Freshdesk accounts not tracked in the official admin panel
- Behavioral nudges achieve high compliance rates for account confirmation without mandatory enforcement
- Offboarding playbook surfaces all Freshdesk access for departing employees automatically
- Fast setup with no agents, proxies, or extensions required
Cons:
- Discovery requires Google Workspace or Microsoft 365; not suitable for organizations without one of those email platforms
- Behavioral model means users can ignore prompts; not appropriate where mandatory enforcement is required
- Very limited public review data compared to established IGA vendors
Gartner Rating: 4.7/5 (22 reviews)
Lumos
Lumos positions its Albus AI agent as the core differentiator for access reviews, and Freshdesk fits squarely within the kind of SaaS application portfolio it was built to govern. During a Freshdesk certification campaign, Albus analyzes each agent account against peer group data, flags accounts whose access patterns differ from similar users in the same department or role, and pre-populates review decisions for low-risk cases. For a support team where most agents share a consistent permission profile, that peer analysis dramatically reduces the number of accounts a manager needs to examine individually.
The Delta Review capability is relevant for recurring Freshdesk audits. Rather than re-certifying every agent account each quarter, Delta Reviews identify only what changed since the last review cycle: new accounts, role changes, and accounts that went inactive. In Freshdesk environments with a stable core agent population but frequent additions for new products or seasonal volume, this narrows the review scope to the accounts that actually warrant scrutiny. Lumos handles Freshdesk within the broader application portfolio context as well, which matters when a user’s Freshdesk access is one piece of a larger access profile that needs to be reviewed in aggregate.
Lumos launched Agentic User Access Reviews in late 2025, completing campaigns at a reported six times the speed of manual processes. The platform is the industry’s first Autonomous Identity Platform and carries a 4.7-star rating on both G2 (54 reviews) and Gartner Peer Insights (47 reviews). More details on the Albus workflow are at Lumos’s site.
Pros:
- Albus AI agent pre-populates Freshdesk access decisions based on peer group analysis
- Delta Reviews focus only on changed accounts, reducing re-certification burden for stable teams
- Self-service access request portal reduces IT tickets for new Freshdesk agent provisioning
- One-click audit-ready compliance reports for SOC 2, SOX, ISO 27001, and HIPAA
Cons:
- No free trial; requires sales engagement to evaluate the platform
- Support relies primarily on self-service resources; no live chat available
- SaaS-only focus creates coverage gaps for organizations with significant on-premises systems
G2 Rating: 4.7/5 (54 reviews) · Gartner Rating: 4.7/5 (47 reviews)
Zluri
Zluri handles Freshdesk access reviews as part of its patented nine-method discovery approach, which captures not just SSO-provisioned Freshdesk accounts but also accounts created through direct signup, OAuth connections, and other paths that bypass the identity provider. For Freshdesk environments where agents use both SSO and native Freshdesk credentials, that multi-source discovery fills the visibility gaps that an IdP-only approach leaves open. The platform pulls user names, job titles, departments, and account types from Freshdesk alongside data from connected HRIS and identity systems, giving reviewers a complete picture of each agent’s organizational context before they make access decisions.
The multi-level reviewer support in Zluri’s certification workflow suits support organizations with multiple management layers. A Freshdesk review campaign can route differently depending on whether the account belongs to a frontline agent (reviewed by a team lead), a supervisor (reviewed by the support manager), or an admin account (reviewed by IT or security). That routing logic runs automatically based on the account attributes Zluri pulls during discovery, so the campaign doesn’t require manual reviewer assignment for each account category.
Zluri’s customers report reducing full-day audit processes to under 30 minutes through bulk approval capabilities and automated reminders. The one-click remediation that removes Freshdesk access directly through the platform’s API connection avoids the manual deprovisioning tickets that typically introduce delays between a certification decision and the actual account change. Full details are on Zluri’s site.
Pros:
- Multi-source discovery catches Freshdesk accounts created outside SSO or IdP flows
- Multi-level reviewer routing handles different account types with separate approval chains
- AI flags orphaned, over-privileged, and external Freshdesk accounts automatically
- One-click remediation deactivates Freshdesk accounts directly through the API
Cons:
- Reporting customization is limited for stakeholders with specific format requirements
- Some niche integrations require custom development beyond the 300+ pre-built connectors
- Discovery engine occasionally misidentifies applications, generating unnecessary alerts
G2 Rating: 4.6/5 (175 reviews) · Capterra Rating: 4.9/5 (27 reviews)
Okta Lifecycle Management
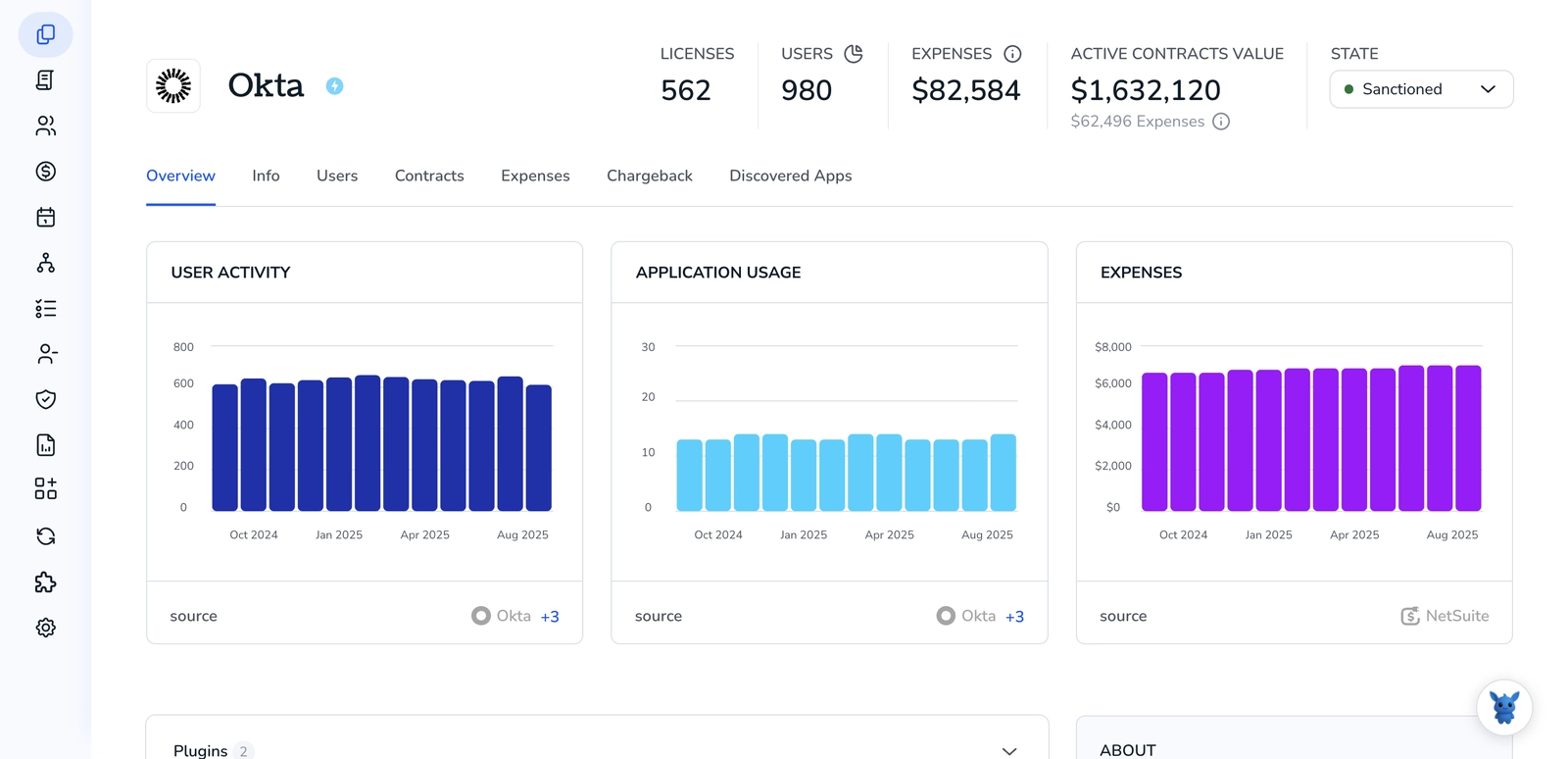
Okta’s integration with Freshdesk extends beyond access certification into the provisioning layer. For organizations that manage Freshdesk agent accounts through Okta, role assignments and license types flow from Okta to Freshdesk automatically when an employee’s title or department changes in the HRIS. A support agent who moves to a product role can have their Freshdesk access scope adjusted or revoked based on the Okta group membership change, without requiring a separate helpdesk ticket. That automation reduces the backlog of access changes that accumulate between formal certification cycles.
The 2025 Security Access Reviews capability in Okta Identity Governance (OIG) adds event-triggered certification to the standard scheduled campaign model. When a Freshdesk user’s organizational data changes, Okta can initiate a targeted review rather than waiting for the next quarterly cycle. The AI-generated access summaries help reviewers understand what a Freshdesk agent account’s current role means in terms of ticket visibility and data access, without requiring the reviewer to be familiar with Freshdesk’s role configuration. That’s useful for managers approving access for their direct reports who aren’t Freshdesk administrators themselves.
Okta’s value in Freshdesk access governance is strongest for organizations already using Okta for identity management across their application stack. Governance features require purchasing the full OIG bundle; teams evaluating Okta primarily for Freshdesk coverage will need to weigh that cost against purpose-built alternatives. More information is at Okta Lifecycle Management.
Pros:
- Automated provisioning flows Freshdesk role changes from HRIS through Okta with no manual steps
- Event-triggered certifications respond to organizational changes without waiting for quarterly campaigns
- AI access summaries simplify Freshdesk permission context for non-admin reviewers
- 7,000+ integration library extends governance across all connected applications
Cons:
- Governance features require purchasing the full OIG bundle, not available as a standalone add-on
- Group-based provisioning model limits granular visibility into Freshdesk role configurations
- Higher per-user cost at scale compared to purpose-built IGA alternatives
G2 Rating: 4.5/5 (1,257 reviews) · Capterra Rating: 4.7/5 (914 reviews)
Oracle Identity Governance

Oracle Identity Governance (OIG) includes Freshdesk as a manageable application through its REST API connector library, handling the user lifecycle events that matter most in a customer support context: provisioning agents when they join, adjusting access when their role changes, and deprovisioning accounts when they leave. OIG’s event-based micro-certification capability applies directly here. When an employee’s department changes in the HRIS and their Freshdesk access no longer aligns with their new function, OIG triggers a targeted review of that specific user rather than batching the situation into the next full certification campaign.
The Oracle Identity Role Intelligence component uses machine learning to analyze access patterns across the Freshdesk user population and identify role assignments that reflect historical accumulation rather than current function. A customer success manager who was granted Freshdesk admin access during a system migration two years ago and still holds it shows up as an outlier in the analysis. That pattern is worth surfacing in periodic reviews, even when the user hasn’t caused any incidents, because admin-level Freshdesk access carries meaningful customer data exposure.
OIG’s suitability for Freshdesk access governance depends heavily on the broader Oracle context. For organizations already running OIG across Oracle Fusion or database-centric environments, extending coverage to Freshdesk is a natural expansion of an existing program. For organizations without that Oracle investment, the per-user licensing at $3,600, the dated interface, and the implementation complexity are harder to justify when lighter alternatives handle Freshdesk governance with less overhead. More information is at Oracle’s governance page.
Pros:
- Event-based micro-certifications catch Freshdesk access drift when role or department changes occur
- Machine learning role intelligence identifies admin accounts holding access beyond their current function
- Hybrid deployment options for organizations with strict data residency requirements
Cons:
- Per-user licensing at $3,600 is expensive compared to SaaS-native alternatives with comparable integration
- Implementation complexity and 12+ month deployment timelines limit suitability outside Oracle-centric environments
- User interface is dated and consistently cited as harder to navigate than cloud-native IGA platforms
G2 Rating: 3.8/5 (71 reviews) · Capterra Rating: 4.4/5 (7 reviews)
Omada Identity
Omada’s Contextual Identity Governance approach adapts certification workflows to how Freshdesk access is actually structured in a support organization. Review campaigns can be scoped by department, manager, or access type, which suits Freshdesk environments where you need separate certification tracks for frontline agents, supervisors reviewing queue metrics, and administrators with system configuration rights. The assignment policy automation handles the recurring portion automatically: access rights are assigned and withdrawn based on defined rules, and the certification campaign focuses on what falls outside those rules.
Javi, Omada’s AI assistant for identity governance, lets entitlement owners launch Freshdesk access reviews directly from within Microsoft Teams. A Freshdesk admin who receives a governance alert about an orphaned agent account can trigger a targeted review and act on it without leaving the collaboration tool. That workflow reduces the friction that often causes governance actions to be deferred, particularly for reviewers who aren’t spending their day inside a governance portal. The 12-week guaranteed deployment through Omada’s Accelerator Package is relevant for support teams under a compliance timeline who can’t absorb a multi-month implementation project.
Omada’s value proposition is clearest in governance-heavy regulated environments where compliance requirements drive the IGA purchase. For a customer support platform like Freshdesk, the full weight of Omada’s governance framework, including 50+ audit report templates and SoD policy enforcement, is most justified when Freshdesk sits within a broader IGA program covering regulated applications. Organizations evaluating Omada primarily for Freshdesk coverage will find the platform capable but potentially more complex than the use case strictly requires. Platform information is at Omada Identity.
Pros:
- Contextual certification campaigns scope Freshdesk reviews by department, manager, or access type
- Javi AI assistant enables Freshdesk governance actions directly from Microsoft Teams
- 12-week guaranteed deployment avoids the multi-month timelines typical of large IGA implementations
- Assignment policy automation handles routine Freshdesk access changes without manual intervention
Cons:
- Large-scale access reviews can surface performance issues with slower re-certification processes
- Reporting aesthetics are dated, and custom report formats require additional configuration effort
- Cloud deployment is significantly more expensive than on-premise; cost calculus differs based on deployment preference
Capterra Rating: 5.0/5 (1 review) · Gartner Rating: 4.6/5 (211 reviews)
Full agent licenses grant access to all ticket queues in scope, customer contact data, internal notes, and conversation history. Supervisor-level access adds team performance reporting and queue metrics that include customer volume data. Admin accounts can configure integrations, manage agent provisioning, and export ticket data across the full account. Collaborator access is more limited but still provides visibility into ticket threads that contain customer PII. Each role level represents a different data exposure profile that access reviews should evaluate against the user's current business function.
MiniOrange

MiniOrange provides SSO integration with Freshdesk through its 6,000+ pre-built connector library, covering the provisioning layer that feeds into access reviews. When an employee leaves the organization or changes roles, MiniOrange’s SCIM-based deprovisioning removes their Freshdesk agent account or adjusts their role assignment automatically through the bi-directional sync with the identity provider. For teams where Freshdesk is part of a larger application portfolio all running through MiniOrange for SSO, that centralized deprovisioning reduces the chance of a former employee retaining active Freshdesk credentials after their accounts in other systems have already been closed.
The Access Governance Automation application for Jira Service Management handles access requests and approval routing for Freshdesk within organizations already using Jira for IT service management. Employees submit Freshdesk access requests through the Jira portal, and the system routes approvals to the appropriate manager or department head based on predefined policy rules. That workflow is a reasonable fit for support teams with formalized provisioning procedures where access requests need documentation and approval trails before Freshdesk agent licenses are assigned.
MiniOrange’s primary strengths are affordability and deployment speed, making it relevant for smaller support teams or companies that need basic Freshdesk identity governance without the cost structure of enterprise IGA platforms. Formal periodic certification campaigns with multi-level reviewer routing and AI-driven risk prioritization are not the platform’s core use case. Details on what’s included are at MiniOrange’s site.
Pros:
- Affordable pricing at $2-$3 per user/month, accessible for smaller support organizations
- SCIM deprovisioning removes Freshdesk agent access automatically when employee status changes
- 6,000+ pre-built integrations cover Freshdesk alongside the broader application portfolio
- Jira-based access request workflow suits teams already using Jira Service Management
Cons:
- Native access certification features are limited compared to dedicated IGA platforms
- Access governance automation depends on Jira Service Management; not suitable for teams without it
- Support quality is inconsistent; positive and negative experiences vary significantly across customers
G2 Rating: 4.5/5 (264 reviews) · Capterra Rating: 4.5/5 (36 reviews)
Ping Identity

Ping Identity’s Autonomous Identity engine uses machine learning to evaluate Freshdesk access at a scale relevant for large enterprise support organizations. The system collects identity data from Freshdesk alongside other governed applications and identifies access outliers, accounts that hold permissions inconsistent with their peer group or historical behavior, that warrant closer review. For large Freshdesk deployments with hundreds of agents across multiple product lines or regions, the AI-driven risk prioritization prevents reviewers from getting lost in low-risk cases when there are higher-priority access situations that need attention.
The PingOne Identity Governance module supports multiple certification types that apply to Freshdesk: application access certification for reviewing who holds Freshdesk agent status, account certification for validating specific accounts across target systems, and entitlement certification for reviewing role-specific permissions within the application. Micro-certifications allow for ad hoc, targeted reviews when a specific Freshdesk user’s access pattern triggers an alert outside the standard campaign schedule. That flexibility matters in support operations where an agent’s access scope can shift rapidly based on the products or customer segments they cover.
Ping Identity is built for large enterprises with complex identity requirements, and the initial configuration reflects that scope. Governance features require separate licensing from the core PingOne Advanced Identity Cloud, and the starting contract value of $16,000+ annually positions this toward organizations running mature enterprise IAM programs. Platform details are at Ping Identity’s site.
Pros:
- Autonomous Identity AI evaluates millions of Freshdesk permissions per minute for anomaly detection
- Multiple certification types cover agent access, specific accounts, and role-level entitlements
- Micro-certifications handle targeted Freshdesk reviews outside of scheduled campaign windows
- FedRAMP authorization and SOC 2 Type 2 certification for regulated industries with strict compliance requirements
Cons:
- Governance features require separate purchase from the core IAM platform
- Initial setup requires significant IAM expertise; learning curve is steep for governance administrators
- Pricing starts at $16,000+ annually; cost structure is difficult to justify for smaller Freshdesk deployments
G2 Rating: 4.5/5 (264 reviews) · Capterra Rating: 4.7/5 (39 reviews)
How to Choose
Freshdesk access governance comes down to a straightforward question: who can see your customers’ support conversations, and how quickly can you correct that when someone’s role changes or they leave the organization. The nine platforms in this comparison handle that problem at different levels of depth and with different cost structures.
Torii is built for IT and security teams managing Freshdesk as part of a broader SaaS portfolio. Its direct integration surfaces agent names, departments, license types, and user status for access reviews, and its AI detects anomalous patterns across the full application stack without requiring a dedicated IGA program to be in place first. For organizations that want Freshdesk governance alongside automated license optimization and SaaS spend management in a single product, Torii combines those workflows in a way no other platform in this comparison does.
Okta and Ping Identity are strongest for organizations with established enterprise IAM programs where Freshdesk access certification is one component of a broader governance scope. Okta’s value is in the provisioning automation it already handles for Freshdesk through SCIM, with the OIG layer extending that into certification campaigns. Ping is the choice for large enterprises with strict compliance requirements, particularly in regulated industries where FedRAMP authorization or granular entitlement-level certification is a hard requirement.
Lumos and Zluri occupy the mid-market IGA space with AI-driven access reviews and faster deployment paths than legacy tools. Lumos’s Albus AI reduces certification effort through peer group analysis and agentic decisioning; Zluri’s multi-source discovery and multi-level reviewer routing suit support organizations with layered management structures. Nudge Security is the right fit for teams where shadow account discovery is the primary concern and formal certification campaigns are a secondary priority.
For smaller support teams or organizations with budget constraints, MiniOrange provides basic Freshdesk provisioning governance at $2-$3 per user. Omada and Oracle target governance-heavy environments with deep compliance requirements; Oracle’s strength is in Oracle-centric enterprise programs, while Omada’s 12-week deployment guarantee makes it a faster path to structured IGA than traditional enterprise tools.
Direct API integration with Freshdesk for real-time user and role data, automated deprovisioning that removes agent accounts when employees leave without manual intervention, AI-driven anomaly detection that identifies agents with role assignments inconsistent with their current function, and audit-ready reporting that documents who had access to customer ticket data and when that access was granted or revoked.
Frequently Asked Questions
Run periodic certification campaigns: pull Freshdesk users via API or an IGA/SaaS tool, scope by license and role, route reviewers, remediate via API/SCIM, and follow up with automated deprovisioning and license reclamation to close the loop.
Full-agent licenses grant access to all ticket queues, conversation history, and exports; supervisors view team reports and queue metrics; admins manage integrations and exports; collaborators see limited threads but may still access customer PII.
Common risks include orphaned or former-employee agent accounts, contractors left with full agent access, role drift creating over-privileged users, unmanaged API keys, and collaborator or external accounts that bypass standard provisioning.
Use multi-source discovery and email-based tools: platforms like Nudge and Zluri scan email logs, SSO, native signups, OAuth connections, and identity sources to reveal contractor, trial, or shared Freshdesk accounts outside the admin panel.
Prioritize direct Freshdesk API integration, automated deprovisioning/SCIM, multi-source discovery, AI-driven anomaly and peer analysis, flexible reviewer routing, one-click remediation, and audit-ready reporting for compliance and cost control.
AI accelerates reviews by flagging anomalous or outlier accounts, pre-populating low-risk decisions through peer-group analysis, prioritizing high-risk entitlements, and powering delta reviews that surface only changed accounts since the last campaign.
Yes. SCIM and lifecycle tools like Okta and MiniOrange automate provisioning and deprovisioning when HR or group membership changes. Event-triggered certifications and automated license reclamation from platforms like Torii prevent access drift and cut per-seat costs.