PagerDuty Access Reviews: 6 Platforms to Consider in 2026

The people who get added as PagerDuty admins during a production incident rarely have that access removed when the crisis passes. Someone escalates permissions to help with troubleshooting at 2 a.m., the outage gets resolved, and the access review that should clean up the damage never happens. Multiply this across on-call rotations that shift every quarter and you can end up with dozens of users holding Global Admin or Manager-level access to every escalation policy and service in your account without any legitimate current need.
On Business and Enterprise plans, PagerDuty uses a layered permission model where base roles, team roles, and object-level grants apply simultaneously. A user can hold Responder access as their base role while also holding Manager-level access on specific services or escalation policies assigned during previous projects. Revoking someone from a team does not automatically remove object-level grants they accumulated separately, which creates access hygiene gaps that manual reviews miss unless they check all three permission layers.
PagerDuty’s advanced permission model makes access governance harder than it appears. Beyond the five basic roles (Stakeholder through Account Owner), Business and Enterprise plans introduce Restricted Access, Observer, Responder, and Manager roles that apply at both the team and object level independently. A former on-call engineer who moved to a non-engineering role might retain Responder access on three production services that nobody assigned intentionally. Auditors preparing for SOC 2 Type II require documented evidence that only current, authorized users hold appropriate PagerDuty roles.
The six platforms reviewed here connect to PagerDuty through direct integrations, identity provider connections, or email-based discovery to surface dormant accounts, flag overprivileged roles, and produce certification evidence for compliance audits. Each section covers what the tool does well for PagerDuty governance, where it falls short, and review ratings from G2 and Capterra.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| Nudge Security | ★★★ | ★★ | ★★ | ★ |
| Lumos | ★★ | ★★ | ★★★ | ★ |
| MiniOrange | ★★ | ★★★ | ★ | ★★ |
| CloudEagle | ★★ | ★★ | ★★ | ★★ |
| Avatier | ★★ | ★★★ | ★★ | ★ |
Table of Contents
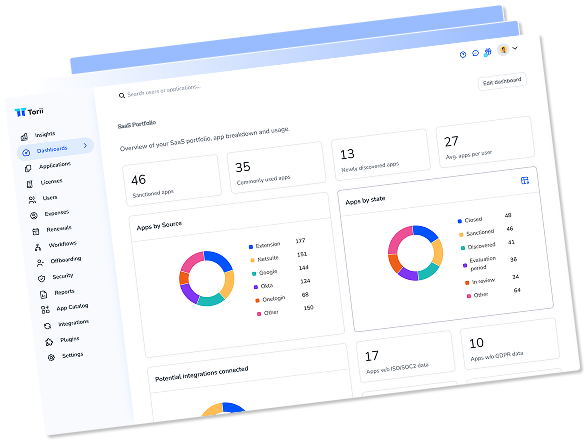
Torii
Torii connects to PagerDuty through a direct integration that pulls employee names, email addresses, job titles, departments, user status, license assignments, and license types into a centralized dashboard. For IT and security teams reviewing PagerDuty access as part of a broader SaaS audit, that organizational context changes the review process. A reviewer can see that a contractor’s PagerDuty Admin seat remained active six months after their other application access was removed, a correlation that requires no manual investigation when everything feeds into the same identity view.
Torii’s AI-powered discovery goes beyond what the PagerDuty API exposes directly. The platform cross-references SSO data, browser extension telemetry, and financial records to surface accounts that exist outside your formally provisioned users, including PagerDuty seats created using work email addresses during trial periods or departmental experiments. When a team spins up a PagerDuty account to test an integration without going through IT, Torii flags it alongside your governed accounts for review.
The in-place attestation workflow routes certification requests to managers with PagerDuty user context surfaced inside the notification, letting reviewers certify access directly from a Slack alert without navigating to a separate governance portal. Torii’s offboarding automation revokes PagerDuty access as part of a complete deprovisioning sequence across all integrated applications, which eliminates the gap between an employee departure and the access cleanup that compliance auditors flag.
Pros:
- Direct PagerDuty integration pulls employee names, titles, departments, license status, and user status into a cross-SaaS identity view
- AI-powered discovery identifies PagerDuty accounts created outside official provisioning workflows and orphaned seats from departed employees
- Automated offboarding removes PagerDuty access as part of deprovisioning across the full application stack
- In-place attestations route PagerDuty certification tasks to managers through Slack with full organizational context
Cons:
- Enterprise-oriented pricing is a step above point solutions, though the combined SaaS management and IGA value typically covers more than PagerDuty reviews alone
- Cloud-only architecture means no on-premise deployment option for organizations with those requirements
G2 Rating: 4.5/5 (302 reviews)
Capterra Rating: 4.9/5 (26 reviews)
Nudge Security
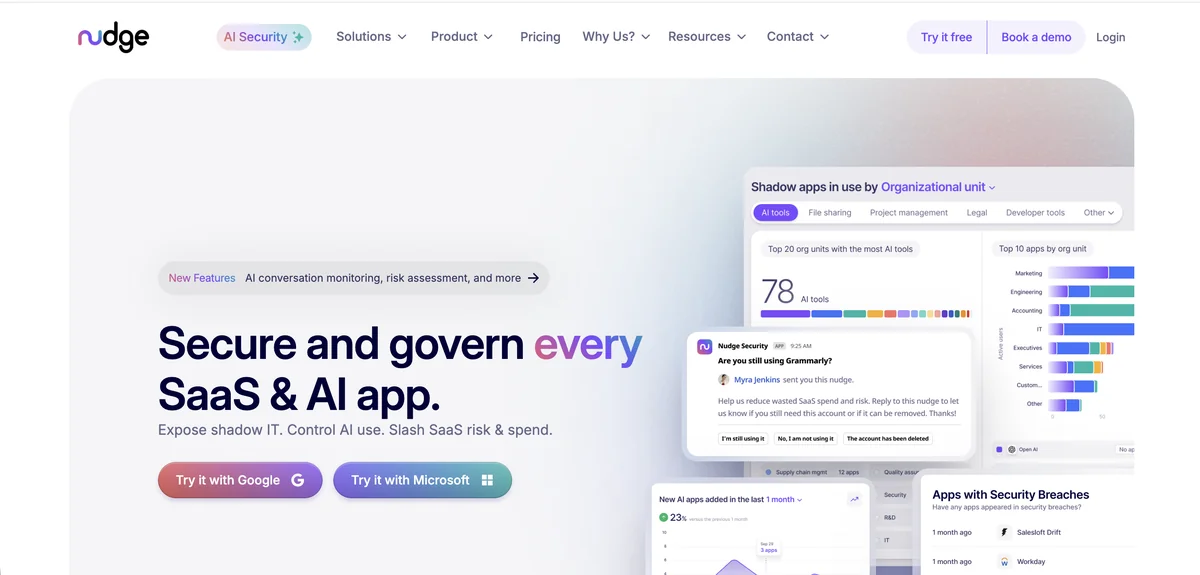
Nudge Security’s email-based discovery finds PagerDuty accounts that standard API connectors cannot reach. When an engineer signs up for PagerDuty using their work email to evaluate a trial, or when a team creates a departmental account outside of official IT channels, those accounts generate email confirmations that Nudge Security picks up through its patented monitoring process. The result is a complete inventory of PagerDuty accounts across your organization that includes both IT-managed seats and the accounts that accumulated without formal provisioning.
For PagerDuty-specific governance, Nudge Security tracks which accounts authenticate through SSO and which fall back to direct username and password logins. This distinction matters for audit purposes: a PagerDuty Admin account that bypasses your identity provider creates a gap in your access controls that periodic reviews should document and address. The platform also monitors third-party OAuth applications connected to PagerDuty, flagging integrations that hold broader permission scopes than necessary.
The behavioral nudge mechanism works differently from traditional certification workflows. Rather than generating a formal approval chain, the platform sends targeted messages via Slack or email prompting users to confirm they still need their PagerDuty access, typically achieving compliance rates around 83%. Organizations with strict mandatory revocation requirements should note that nudges rely on user response rather than enforced policy changes.
Pros:
- Discovers PagerDuty accounts created outside official IT provisioning through email-based monitoring
- Tracks SSO vs. direct-login authentication for every PagerDuty account, identifying access control gaps
- Monitors OAuth integrations connected to PagerDuty for excessive permission scopes
- Supply chain breach monitoring alerts when PagerDuty or connected vendors have a security incident
Cons:
- Email-based discovery requires Google Workspace or Microsoft 365, limiting use in organizations running other email platforms
- Behavioral nudges cannot force access revocation when users do not respond
- Limited public review volume with only 22 Gartner ratings makes independent peer validation harder
G2 Rating: 5.0/5 (limited reviews)
Gartner Rating: 4.7/5 (22 reviews)
Lumos
Lumos takes an AI-native approach to PagerDuty access reviews through its Albus AI agent, which evaluates role assignments against peer group behavior and usage patterns rather than sending decisions to a human reviewer for every account. For PagerDuty environments where engineering teams rotate on-call responsibilities quarterly, the platform compares each user’s role level against colleagues in the same team with similar functions, flagging accounts where the assigned permissions look anomalous without requiring a manager to assess each one individually. The company reports that review campaigns complete roughly seven times faster using Albus than with traditional manual workflows.
Lumos also enables self-service access requests for PagerDuty through a Slack-based app portal. When an engineer joins a new on-call rotation, they can request Responder access through the portal, route the approval to their team lead, and receive provisioned access without submitting a help desk ticket. Delta Reviews make recurring campaigns more manageable by focusing only on PagerDuty role changes since the last review cycle, so teams that run quarterly certifications are not re-examining the same stable accounts every time.
Time-based access controls allow Lumos to provision PagerDuty admin roles with automatic expiration. For incident response scenarios where someone needs temporary elevated access, the platform can grant Manager-level permissions on specific services with a defined end date rather than requiring a manual revocation step that often gets skipped.
Pros:
- Albus AI agent evaluates PagerDuty role assignments against peer groups and automatically approves or flags based on usage context
- Self-service Slack portal lets engineers request PagerDuty Responder access when joining on-call rotations without IT intervention
- Delta Reviews focus subsequent campaigns only on PagerDuty access changes since the last cycle, reducing certification fatigue
- Time-based access controls expire elevated PagerDuty permissions automatically after an incident-response window closes
Cons:
- No live chat support, which creates slower resolution paths for governance issues that need immediate attention
- Initial setup and workflow configuration require more time to master than the platform's marketing suggests
G2 Rating: 4.7/5 (54 reviews)
Gartner Rating: 4.7/5 (47 reviews)
MiniOrange

MiniOrange governs PagerDuty access through SCIM provisioning connected to Okta, Microsoft Entra ID, or OneLogin, keeping PagerDuty user status synchronized with your identity provider automatically. When an engineer’s department changes in your HR system, the updated role mapping propagates through the IdP to PagerDuty without a manual provisioning step. When someone is deactivated in your identity provider, the SCIM connection removes their PagerDuty account immediately. This automated lifecycle management reduces the window between an employment status change and the corresponding access update that creates audit gaps.
MiniOrange’s Access Governance Automation app routes PagerDuty access requests through Jira Service Management, creating a structured approval record for every permission grant. An engineer requesting on-call Responder access submits through the Jira portal, the request routes to their team lead based on policy-defined rules, and the approved provisioning action logs automatically as part of your audit trail. This ticketing approach produces evidence that SOC 2 auditors can examine directly, showing both the request and the approval decision for each PagerDuty permission grant.
The platform’s adaptive risk-based authentication evaluates login attempts against behavioral patterns, device posture, and geographical context, stepping up authentication requirements when PagerDuty logins look anomalous without blocking legitimate access during actual incidents.
Pros:
- SCIM provisioning keeps PagerDuty user status synchronized with your identity provider for automated lifecycle management
- Jira-based access request workflows create structured approval records for every PagerDuty permission grant
- Adaptive risk authentication adds step-up requirements for suspicious PagerDuty logins without creating friction during legitimate incidents
Cons:
- Periodic access certification campaigns with formal manager attestations are less developed than purpose-built IGA platforms
- Governance workflow automation requires Jira Service Management, creating a tooling dependency not every organization has in place
- Customer support quality has varied across user reports, which creates risk for teams relying on responsive help during compliance timelines
G2 Rating: 4.5/5 (264+ reviews)
Capterra Rating: 4.5/5 (36 reviews)
PagerDuty's native Audit Trail (available on Business and Enterprise plans) logs changes to users, teams, services, and escalation policies, but it does not record individual user additions or removals from escalation policy steps. This means a user could be added to an escalation policy route during an incident and removed afterward with no log entry that traditional access reviews can reference. Identity governance platforms that pull PagerDuty data through direct API or SCIM integrations can surface current membership states for certification, even when PagerDuty's own audit log does not capture every historical change.
CloudEagle
CloudEagle connects to PagerDuty through SSO integrations and identity providers, pulling user license data and access status into its governance dashboard. The platform’s AI-driven risk flagging surfaces PagerDuty accounts where users have not logged in for 90 or more days, a particularly useful filter for PagerDuty environments with large Stakeholder populations. Many organizations add executives and cross-functional team members as Stakeholders during an incident so they can monitor status updates, then never remove them when their monitoring period ends. CloudEagle brings these inactive accounts to the top of review queues where they would otherwise blend into a long user list.
CloudEagle’s Slack-native workflow engine reduces the friction that leads to incomplete access reviews. Rather than asking managers to log into a separate governance portal to certify PagerDuty access, the platform routes review requests directly into Slack with approve and reject options that trigger deprovisioning automatically. For engineering managers who spend most of their day in Slack, completing a PagerDuty certification without context switching makes higher completion rates realistic. User feedback consistently cites an 80% reduction in review time compared to manual processes.
One practical limitation: CloudEagle’s governance module starts at $2,000 per month, which positions it toward mid-market and enterprise organizations with enough SaaS complexity to justify the investment. Teams looking for PagerDuty governance as a single use case may find the pricing structure broader than their needs.
Pros:
- AI risk flagging surfaces inactive PagerDuty accounts and users who haven't logged in for 90+ days without requiring manual filtering
- Slack-native approvals let managers complete PagerDuty access certifications from their primary communication tool
- Review automation delivers an 80% reduction in time spent compared to manual certification processes
- SOC 2 compliance reports generate in approximately 15 minutes according to published customer feedback
Cons:
- Governance module pricing starts at $2,000 per month, which is difficult to justify if PagerDuty is the only application under review
- No API access limits organizations that need to pull CloudEagle governance data into external reporting tools
- Initial platform configuration involves a steeper learning curve than the workflow simplicity suggests
G2 Rating: 4.7/5 (150+ reviews)
Gartner Rating: 4.6/5 (53 reviews)
Avatier

Avatier’s Identity Anywhere platform approaches PagerDuty governance through its Delta Access Certification model, which audits only the access that changed since the previous review cycle. For organizations running quarterly PagerDuty certifications, this means the second review does not require re-examining every stable account that has been in place since the last audit. Reviewers see only the new role assignments, role changes, and account additions that occurred during the intervening period, which makes recurring certification cycles faster to complete and less prone to the rubber-stamping that undermines formal review programs.
Avatier supports multi-channel PagerDuty access reviews through native integrations with Microsoft Teams, Outlook, Slack, ServiceNow, and mobile apps. Engineering managers who are themselves on-call and working from mobile devices can complete PagerDuty certifications from the same phone they use to respond to incidents, removing the scheduling constraint that comes with requiring desktop-based portal access during active review windows. The platform’s AI-powered access pattern analysis flags PagerDuty accounts with role assignments that deviate from what users in comparable positions typically hold.
Avatier’s containerized architecture, built on Docker containers, deploys on any cloud or on-premise infrastructure without vendor lock-in. For enterprises running PagerDuty alongside SAP, Oracle, or other core systems in specific hosting environments, this deployment flexibility accommodates data residency constraints that cloud-only platforms cannot address.
Pros:
- Delta certification audits only PagerDuty access changes since the last review cycle, keeping recurring campaigns focused and reducing reviewer fatigue
- Multi-channel review support lets managers certify PagerDuty accounts from Teams, Slack, Outlook, or mobile without desktop portal access
- AI pattern analysis flags PagerDuty role assignments that look anomalous compared to users in similar positions
- Containerized architecture deploys on any cloud or on-premise environment, accommodating organizations with specific hosting constraints
Cons:
- Small market presence with 0.04% IAM share means limited community resources, third-party integrations, and no current Gartner or Forrester analyst recognition
- Interface complexity can overwhelm new users and certain workflows require more navigation steps than competing platforms
G2 Rating: 4.6/5 (31 reviews)
How to Choose
Selecting a PagerDuty access review platform depends on what problem is driving the need. If your team manages PagerDuty alongside a large SaaS portfolio and wants a single platform handling both identity governance and SaaS spend, Torii’s unified approach covers PagerDuty reviews as part of your complete application stack with AI-powered discovery that catches accounts your identity provider never provisioned.
Confirm whether the platform connects directly to PagerDuty through the API or relies entirely on your identity provider for user data. Ask whether it surfaces all three permission layers (base roles, team roles, object-level grants) or only top-level role assignments. Verify what evidence it produces for SOC 2 auditors and whether recurring certification campaigns can run automatically without manual setup each cycle. Also check whether deprovisioning after a review decision happens automatically or creates a ticket someone else must action.
Teams where shadow IT discovery is the primary concern tend to favor Nudge Security, which finds PagerDuty accounts that API-based platforms cannot see. Lumos works well for organizations where AI-driven review automation and self-service access request workflows matter more than breadth of SaaS discovery. MiniOrange fits smaller organizations that need structured SCIM-driven lifecycle management and Jira-based approval records without enterprise IGA pricing. CloudEagle and Avatier both offer strong automation for teams that want Slack-native workflows or cloud-agnostic deployments respectively.
Pricing varies significantly across this group, and the gap shapes what is realistic for most teams. Enterprise IGA deployments can run six figures annually with months of implementation work. Mid-market platforms like MiniOrange and Avatier offer lower per-user costs and faster onboarding for organizations that cannot justify that scale. Torii’s per-employee model makes the most sense when PagerDuty governance is one part of a broader SaaS management strategy covering automated license reclamation, shadow IT controls, and IT automation across your full application portfolio.
Frequently Asked Questions
On Business and Enterprise plans base roles, team roles, and object-level grants apply simultaneously. Revoking a team role doesn’t remove separate object grants, so users can retain elevated access unnoticed unless reviews inspect all three permission layers and object memberships.
Use direct API or SCIM/SSO integrations, email-based discovery, cross-referenced SSO and telemetry, financial records, and identity provider signals. Platforms combining API, email monitoring, and AI-powered discovery surface orphaned seats, trial accounts, and departmental test instances outside provisioning.
Auditors expect documented certification records proving only current authorized users hold appropriate PagerDuty roles, plus evidence of recurring reviews, approval workflows, deprovisioning actions, and generated reports. Because PagerDuty audit logs miss some membership changes, governance platforms must supply certification artifacts.
Time-bound access grants, automated expiration for Manager-level roles, automated offboarding tied to identity lifecycle, delta reviews that focus on recent changes, and enforced deprovisioning after certification prevent elevated incident permissions from persisting after the crisis.
Compare whether it connects via PagerDuty API or relies on IdP, whether it surfaces base, team, and object-level grants, what audit evidence it produces, automation for recurring certifications, deprovisioning after reviews, discovery breadth, and total cost of ownership.
Torii offers broad SaaS discovery and AI but higher enterprise pricing; Nudge finds shadow accounts via email but cannot force revocations; Lumos emphasizes AI automation and time-based access; MiniOrange focuses on SCIM lifecycles; CloudEagle delivers Slack-native workflows; Avatier supports on-prem delta certifications.