7 Ways to Run OneLogin Access Audits in 2026

OneLogin sits at the authentication layer for every application it protects. When an employee leaves, changes roles, or accumulates app assignments over time, the SSO layer is often the first place that access needs to be reviewed. In 2026, audit cycles, compliance frameworks, and security team mandates have made that review process non-negotiable for most organizations using OneLogin as their primary identity provider.
The admin console in OneLogin shows active users, application assignments, and group memberships. What it doesn’t offer is a structured certification workflow. There’s no built-in mechanism to route a user’s application list to their manager for attestation, track which accounts were reviewed in a given quarter, or produce an evidence package for a SOC 2 Type II auditor who needs documentation of your review process.
Active user accounts and their application assignments through the SSO catalog, group and role memberships that determine downstream application access, API credentials and service accounts tied to OneLogin, inactive or suspended accounts still consuming licenses, contractor and shared accounts without a corresponding active HRIS record, and MFA enforcement status across the user population.
This comparison covers seven platforms for OneLogin access audits in 2026, from SaaS governance tools that handle OneLogin as part of a broader application stack to enterprise IGA platforms that connect directly to OneLogin’s directory and provisioning layer.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| ConductorOne | ★★★ | ★★ | ★★★ | ★ |
| Nudge Security | ★★★ | ★★ | ★★ | ★ |
| Lumos | ★★ | ★ | ★★★ | ★★ |
| SAP Cloud IAG | ★ | ★ | ★★ | ★★ |
| One Identity | ★ | ★★ | ★★ | ★★ |
| Omada Identity | ★★ | ★ | ★★ | ★★ |
Table of Contents
- Torii
- ConductorOne
- Nudge Security
- Lumos
- SAP Cloud Identity Access Governance
- One Identity
- Omada Identity
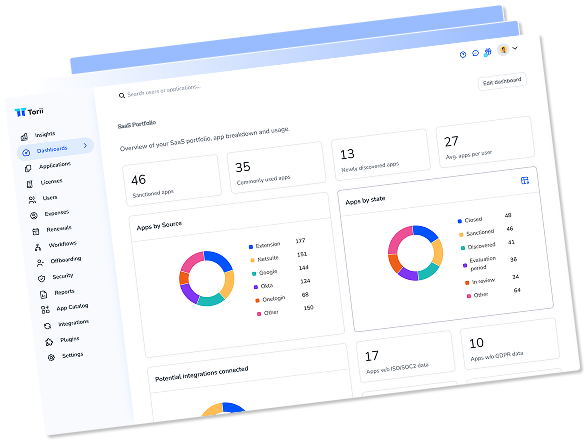
Torii
Torii connects to OneLogin and pulls employee name and email, job title, department, user status, license status, license types, and historical usage by employee for every OneLogin account tied to an active HR record. That combination gives reviewers a complete picture during quarterly certification campaigns: who the user is, what their current role is, whether the OneLogin license is active, and how recently they’ve authenticated through the platform, without cross-referencing the OneLogin admin panel against a separate HR export.
Historical usage data is where OneLogin reviews often surface the most actionable findings. An employee whose account is active and licensed but who hasn’t authenticated through OneLogin in several months is a common access drift scenario, particularly in organizations where SSO enforcement isn’t universal across every application. Torii flags those patterns automatically, and accounts that exist in OneLogin with no corresponding active HRIS record surface alongside them, covering the orphaned account scenario that accumulates after org restructures and contractor offboarding.
Torii’s certification campaigns log every approval and revocation with a timestamp and reviewer attribution, generating an audit trail that satisfies SOC 2 and ISO 27001 requirements. OneLogin governance runs within the same platform managing the rest of the SaaS stack, so IT teams aren’t operating a separate review program just for the identity layer. Torii holds the number-one ranking in G2’s inaugural SaaS Management Platform Grid Report and is recognized as a 2025 Gartner Magic Quadrant Leader for SaaS Management Platforms.
Pros:
- Surfaces employee name/email, title, department, user status, license data, and historical usage directly from OneLogin
- Identifies OneLogin accounts with no matching active HRIS record, flagging orphaned accounts for cleanup
- Routes certification tasks automatically with a complete, timestamped audit trail for SOC 2 and ISO 27001
- Manages OneLogin governance within the same platform handling SaaS spend, shadow IT, and the rest of the application stack
Cons:
- Pricing reflects an enterprise-grade feature set, positioning it above entry-level point solutions
- Designed for SaaS-first environments; on-premise deployments are not supported
| G2: 4.5/5 (302 reviews) | Capterra: 4.9/5 (26 reviews) |
ConductorOne
ConductorOne integrates with OneLogin through its Unified Identity Graph, syncing user accounts, application assignments, group memberships, and role entitlements in real time. For teams managing OneLogin alongside other identity providers such as Azure AD or a legacy on-premise directory, ConductorOne consolidates those sources into a single certification interface. Reviewers work from one view rather than switching between admin consoles for each identity layer.
Access review campaigns for OneLogin in ConductorOne can be scoped at the application level rather than the entire user directory. If the question is whether everyone assigned to a specific SaaS application through OneLogin actually needs it, reviewers run a targeted campaign against that assignment rather than certifying the full directory. ConductorOne’s AI agents handle routine certifications automatically based on peer group analysis and usage patterns, surfacing only the exceptions for human review. Customers report an 85 percent reduction in review time, with campaigns that previously took two weeks finishing in under 24 hours.
When a reviewer denies an application assignment in OneLogin, ConductorOne triggers the revocation across connected systems automatically without requiring a separate IT ticket. The platform also supports just-in-time access conversion, which removes standing OneLogin application assignments and replaces them with time-bound grants that expire after a defined window. Visit ConductorOne’s website to see the full connector list and trial access options.
Pros:
- Real-time sync with OneLogin pulls user accounts, app assignments, and group memberships into a single certification view
- AI agents automate routine OneLogin certifications, routing only exceptions to human reviewers
- Just-in-time access converts standing OneLogin application assignments to time-bound grants that expire automatically
Cons:
- No public pricing; evaluation requires a sales conversation before any budget comparison is possible
- Access reviews can only revoke assignments, not modify permission levels within a given application
- 13 G2 reviews indicates a smaller market footprint compared to platforms with hundreds of verified ratings
- No Capterra listing, limiting review coverage for procurement teams using that platform
G2: 4.8/5 (13 reviews)
Nudge Security
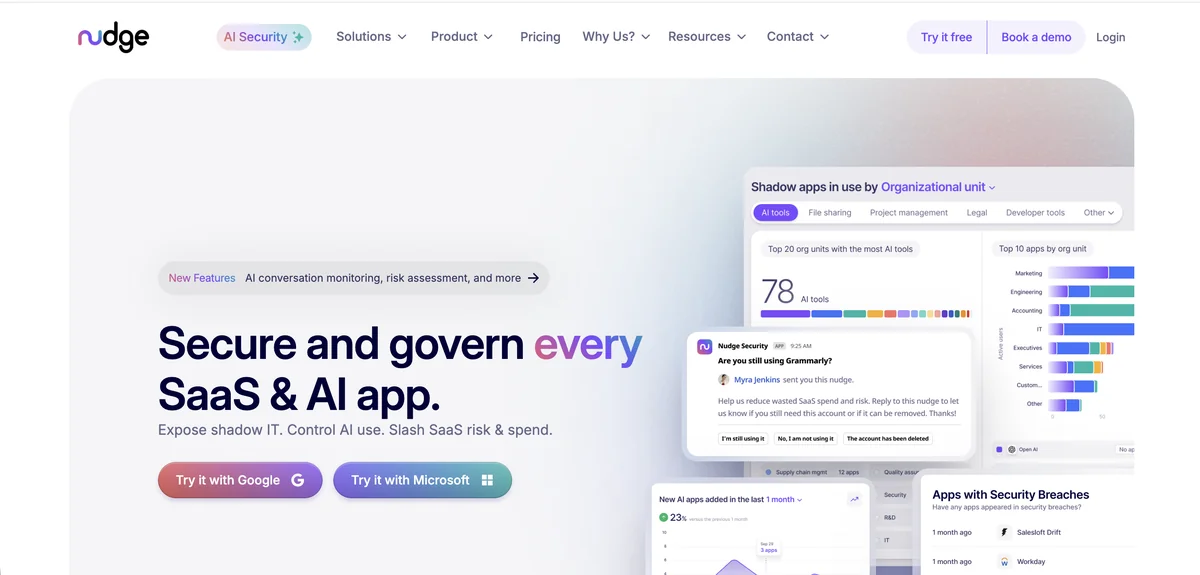
Nudge Security’s approach to OneLogin starts at the discovery layer. Its patented email-based detection finds all OneLogin accounts across the organization, including accounts that predate the formal SSO rollout, shared accounts used by multiple people, and OAuth grants connected through OneLogin that are no longer actively used. For organizations where OneLogin was adopted incrementally rather than all at once, that historical visibility matters before any meaningful review can begin.
Once accounts are cataloged, Nudge Security tracks whether OneLogin is actually being used as the SSO provider for each connected application or whether users have parallel direct-login credentials that bypass SSO entirely. That distinction is relevant for OneLogin access reviews specifically: removing a user’s OneLogin account doesn’t revoke access to an application where they also have a direct password stored in their browser. Nudge Security’s discovery surfaces those parallel credentials so the scope of an access review is accurate rather than incomplete. More details on the methodology are available at Nudge Security’s website.
The review workflow uses behavioral nudges delivered through Slack or email, prompting users to confirm whether their access is still needed and routing flagged accounts to owners for action. Nudge Security reports an 83 percent compliance rate with this approach. Teams whose primary OneLogin challenge is sprawl and shadow accounts will find it a solid fit. Those needing formal certification campaigns with manager sign-off workflows and SOC 2 audit evidence packages should evaluate a tool with more structured governance capabilities.
Pros:
- Discovers OneLogin accounts and downstream app connections that predate or bypass formal IT provisioning
- Shows which applications rely on OneLogin SSO versus which have parallel direct-access credentials that survive a OneLogin deprovisioning
- Behavioral nudge approach achieves high response rates without requiring manager login to a separate certification portal
Cons:
- Formal certification campaigns with structured manager review queues and SOC 2 audit evidence are not a core capability
- Requires Google Workspace or Microsoft 365 as the email discovery foundation; the platform doesn’t work without one of those
- MFA tracking is visible but enforcement relies on behavioral change rather than automated policy controls
Gartner Peer Insights: 4.7/5 (22 reviews)
Organizations where OneLogin is the only login method for every application have a cleaner review problem: remove someone from OneLogin and their downstream application access stops. Organizations where SSO is optional or enforced only for selected applications face a broader challenge: a OneLogin review alone doesn't capture every active credential that user holds across the environment. Tools that track both SSO-managed and direct application access handle the full picture.
Lumos
Lumos connects to OneLogin and maps every user, application assignment, and role entitlement through its centralized access visibility layer. Its Albus AI agent handles certification decisions automatically based on peer group analysis and usage anomalies, approving or flagging access rather than routing every assignment to a human reviewer. For OneLogin environments with hundreds of application assignments across a large user base, that automation is practical: Lumos reports completing access reviews seven times faster, with 50 or more hours saved per quarter per review cycle.
Delta Reviews are particularly relevant for ongoing OneLogin governance. Rather than re-certifying the entire OneLogin user directory each quarter, subsequent campaigns are scoped to only the accounts and assignments that changed since the last cycle. Employees who joined, changed roles, or received new application assignments through OneLogin get reviewed. Accounts that haven’t changed and were already certified stay out of scope. That scoping keeps campaigns manageable as the OneLogin user base grows without creating compliance gaps in the coverage.
Lumos also handles self-service access requests for OneLogin application assignments through Slack or Microsoft Teams. Employees request application access through a workflow, triggering an approval chain before provisioning through OneLogin. The request history becomes part of the access record reviewers see during certification, giving context for why a user holds a particular assignment rather than asking reviewers to make a decision without any background. The full feature list is on Lumos’s website.
Pros:
- Albus AI agent automates OneLogin certification decisions using peer analysis and usage data, cutting manual reviewer load significantly
- Delta Reviews scope campaigns to changed accounts only, keeping quarterly OneLogin audits proportional as the user base scales
- Self-service access request history gives reviewers context about the origin of a OneLogin application assignment during certification
- One-click audit-ready compliance reports reduce the manual documentation burden for SOC 2 and ISO 27001 evidence preparation
Cons:
- No free trial; platform evaluation requires a sales conversation before any hands-on testing
- Some users report a steeper learning curve than initial onboarding timelines suggest, with weeks spent configuring workflows
| G2: 4.7/5 (54 reviews) | Gartner Peer Insights: 4.7/5 (47 reviews) |
SAP Cloud Identity Access Governance
SAP Cloud Identity Access Governance connects to OneLogin through SCIM-based integration, pulling user accounts and role assignments into its Access Certification module. For organizations already running SAP Cloud IAG for governance across S/4HANA Cloud, SuccessFactors, or Ariba, adding OneLogin to the same campaign framework consolidates identity reviews without running a parallel process for the SSO layer. The platform’s SoD engine can run cross-system conflict checks spanning both SAP application roles and OneLogin-managed application assignments in a single pass.
The Access Certification module supports scheduled campaigns with configurable reviewer workflows, automated escalation when deadlines are missed, and a compliance dashboard tracking campaign completion rates. OneLogin user accounts can be included in both user attestation campaigns and role certification campaigns depending on what the review is designed to address. SAP IAG’s role design module, which uses machine learning to optimize access structures, can also surface OneLogin application assignments that fall outside the expected pattern for a given job function.
SAP Cloud IAG is engineered for enterprises deeply invested in the SAP ecosystem. For teams without SAP infrastructure, the SCIM-based OneLogin connector works at a technical level, but the implementation overhead involved in configuring and operating SAP IAG makes it difficult to justify for OneLogin governance alone. Pricing is enterprise-only with no public rate card, and running campaigns effectively requires specialized SAP expertise. Check the SAP Cloud IAG product page for module details and trial access options.
Pros:
- SCIM integration pulls OneLogin users and app assignments into the same certification campaigns covering SAP application environments
- Cross-system SoD checks span OneLogin assignments alongside SAP roles in a single conflict detection pass
Cons:
- Implementation overhead is difficult to justify for OneLogin governance in organizations without existing SAP infrastructure
- Enterprise-only pricing with no public rate card; trial access is limited to a 50-user BTP sandbox
- Performance issues reported during large-scale certification campaigns involving many identities
| G2: 3.0/5 (limited reviews) | Gartner Peer Insights: 4.4/5 (114 reviews) |
One Identity
One Identity and OneLogin are products from the same company. The company’s portfolio includes Identity Manager for IGA, Safeguard for privileged access management, and OneLogin for access management. That vendor relationship means Identity Manager has governance capabilities designed to work with the OneLogin access layer rather than connecting to it through a generic SCIM integration. For enterprises already standardized on OneLogin as their SSO, One Identity Identity Manager provides a governance layer that shares a product lineage with the identity provider it’s auditing.
Identity Manager’s attestation framework defines what gets reviewed, who reviews it, and on what schedule. OneLogin user accounts, application assignments, and role memberships can all be included in structured certification campaigns. Managers receive attestation cases through One Identity’s web portal or integrated ITSM workflows and either certify or deny the access items presented. Every step in the process generates an audit-proof record that can be reconstructed during regulatory examinations. The platform manages over 500 million identities across 11,000 organizations, with particular depth in hybrid environments where OneLogin SSO sits alongside on-premise Active Directory and enterprise systems.
The practical constraints are implementation complexity and access certification usability. OneLogin’s admin interface is modern and intuitive. One Identity’s attestation UI is not, and multiple Gartner reviewers explicitly flag the certification interface as dated and difficult to use for end reviewers who aren’t IAM specialists. Implementation costs run from $5,000 to $50,000, and a deployment partner is typically required. Learn more at One Identity’s website.
Pros:
- Shares vendor lineage with OneLogin, providing governance designed around the OneLogin access model rather than a generic connector
- Attestation policies cover OneLogin user accounts, app assignments, and group memberships with full audit-proof record keeping
- Unified IGA and PAM platform eliminates the need for separate privileged access management tooling alongside governance
Cons:
- Attestation user experience is dated; multiple Gartner reviewers describe the certification interface as unintuitive for non-IAM users
- Implementation typically requires a specialized partner and costs $5,000 to $50,000 before configuration work begins
- Not suited to cloud-only environments; strongest value is in hybrid landscapes with on-premise identity infrastructure
| Capterra: 5.0/5 (2 reviews) | Gartner Peer Insights: 4.4/5 (155 reviews) |
Omada Identity
Omada connects to OneLogin through SCIM 2.0 and its API-based connector framework, pulling user accounts, application assignments, and role memberships into its certification campaign engine. Its IdentityPROCESS+ framework delivers a pre-configured governance process rather than requiring teams to design certification workflows from scratch. For organizations deploying IGA for the first time with OneLogin as their identity foundation, that accelerated model reduces the time between project kick-off and first certification campaign. Omada guarantees implementation in 12 weeks, which is faster than the six to twelve month timelines common with enterprise IGA platforms.
Access reviews in Omada support cross-system certification campaigns, meaning OneLogin application assignments can be reviewed in the same campaign covering Active Directory groups, Salesforce profiles, or any other connected system. Automated data gathering eliminates the manual collection work that typically precedes campaign launch. Managers and resource owners can also start self-service reviews directly from Javi, Omada’s AI assistant embedded in Microsoft Teams, without logging into a separate governance portal. That Teams integration is practical for organizations where OneLogin users are primarily Microsoft-ecosystem workers.
Omada’s reporting engine generates comprehensive audit trails for OneLogin reviews, and its architecture archives every access decision, justification, and timestamp; the platform holds 211 Gartner Peer Insights reviews at 4.6 out of 5. Cloud adopters should factor in both cost and feature availability before committing: the SaaS version of Omada is significantly more expensive than on-premise, and some advanced governance capabilities are only available in the on-premise deployment. Visit Omada Identity’s website for current deployment and pricing details.
Pros:
- SCIM 2.0 connector pulls OneLogin users and app assignments into cross-system certification campaigns alongside other connected directories
- 12-week implementation guarantee is significantly faster than typical enterprise IGA deployment timelines
- Javi AI assistant lets managers launch OneLogin access reviews from Microsoft Teams without a separate portal login
Cons:
- Cloud version is significantly more expensive than on-premise and carries feature limitations compared to the on-premise deployment
- Performance slows during large-scale recertification campaigns with many OneLogin users based on user feedback
- Custom reporting is restricted despite 50-plus pre-built templates; organizations needing tailored audit outputs may find the options limiting
| G2: 4.5/5 (limited reviews) | Gartner Peer Insights: 4.6/5 (211 reviews) |
How to Choose a OneLogin Access Review Tool
OneLogin’s role as an SSO gateway shapes what access reviews need to accomplish. For most organizations, the core questions are the same: who has active OneLogin accounts, what applications can they reach through SSO, and does that access still match their current job function.
If your primary concern is aligning OneLogin access with current HRIS data and running reviews alongside the rest of your SaaS stack, SaaS governance platforms like Torii cover that without dedicated IGA infrastructure. If your OneLogin environment includes complex group hierarchies, cross-system SoD requirements, or privileged admin account governance, dedicated IGA platforms like One Identity or Omada provide the certification depth those scenarios require.
For teams where OneLogin governance is one part of a broader SaaS management program, Torii handles the review within the same platform tracking SaaS spend, shadow IT discovery, and automated license remediation across the rest of the stack. That consolidation tends to reduce operational overhead compared to running separate certification workflows for each tier of the identity environment.
ConductorOne and Lumos work well for cloud-first organizations that want fast deployment and AI-assisted review automation. ConductorOne’s just-in-time access model removes standing OneLogin application assignments in favor of time-bound grants, which addresses the over-provisioning problem directly for teams building toward least-privilege access policies. Lumos’s Delta Review capability works well when the OneLogin user base is relatively stable and quarterly campaigns should focus on what actually changed rather than re-certifying the full directory each time.
Request a demo of the attestation workflow specifically. The product relationship between Identity Manager and OneLogin is a genuine advantage, but the certification UI is a known friction point. Seeing it firsthand before committing is time well spent.
One Identity is worth a serious look specifically for enterprises already running OneLogin and interested in a governance layer from the same vendor. The native product relationship between Identity Manager and OneLogin means governance is built around the access model rather than bolted onto it. That advantage comes with implementation complexity and UI limitations that cloud-native alternatives avoid, so the fit is strongest for large enterprises with dedicated IAM teams.
Omada makes the most sense for mid-market companies in regulated industries that need structured IGA without a year-long implementation project. Its 12-week deployment and compliance-oriented reporting are practical for teams facing audit deadlines with a well-defined scope.
Frequently Asked Questions
They assess active OneLogin accounts and SSO application assignments, group and role memberships, API/service credentials, inactive or suspended accounts still consuming licenses, contractor/shared accounts without HRIS records, and MFA enforcement status across the user population.
The admin console shows users, apps, and groups but lacks structured certification: no manager attestation routing, no campaign tracking, no automated revocation workflows, and no packaged audit evidence for SOC 2 or ISO 27001 auditors.
SaaS governance platforms like Torii integrate OneLogin with HRIS and SaaS spend management, offering faster deployment and unified review within a single platform; enterprise IGA tools provide deeper role design, cross-system SoD checks, and governance for hybrid on-prem environments.
Look for HRIS and SCIM sync, real-time user and group sourcing, manager attestation and escalation, audit-ready timestamped logs, automated revocation or JIT access, shadow-account discovery, AI-assisted exception handling, and integrations with Slack, Teams, or ITSM.
AI agents auto-certify routine assignments using peer-group analysis and usage patterns, flag exceptions for human review, scope delta-based campaigns to recent changes, and reduce review time significantly while routing only contested items to managers.
They log every attestation and revocation with timestamps and reviewer attribution, archive historical decisions and justification, generate exportable compliance reports, and package an audit trail that demonstrates who reviewed what and when for auditor verification.