MongoDB Access Reviews: 7 Platforms to Consider in 2026

MongoDB’s native access controls are more granular than most SaaS applications. A single Atlas project can contain dozens of users, each assigned specific built-in roles (read, readWrite, dbAdmin, clusterAdmin) at the database or collection level, alongside service accounts used by applications through connection strings and API keys. When headcount grows or org structures shift, that granularity compounds quickly.
Atlas provides built-in audit logging and LDAP integration for enterprise teams, but it doesn’t hand you a certification campaign. You still need to route access for manager sign-off, track who reviewed what and when, and produce a paper trail that holds up to SOC 2 or ISO 27001 scrutiny. That’s where third-party tools step in.
Atlas organization and project roles, database-level user accounts and built-in role assignments, collection-level permissions for sensitive data, service accounts and API keys used by applications, LDAP-integrated users in enterprise deployments, and orphaned accounts that remain active after role transitions or employee departures.
This comparison covers seven platforms for MongoDB access reviews in 2026, from SaaS governance tools that handle MongoDB as part of a broader stack to enterprise IGA platforms with purpose-built certification workflows.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| Veza | ★★★ | ★ | ★★★ | ★ |
| Nudge Security | ★★ | ★★ | ★★ | ★ |
| Okta Lifecycle Management | ★★ | ★ | ★★ | ★★★ |
| SAP Cloud IAG | ★ | ★ | ★★ | ★★ |
| Oracle Identity Governance | ★ | ★ | ★★ | ★★ |
| Avatier | ★★ | ★★ | ★ | ★ |
Table of Contents
- Torii
- Veza
- Nudge Security
- Okta Lifecycle Management
- SAP Cloud Identity Access Governance
- Oracle Identity Governance
- Avatier
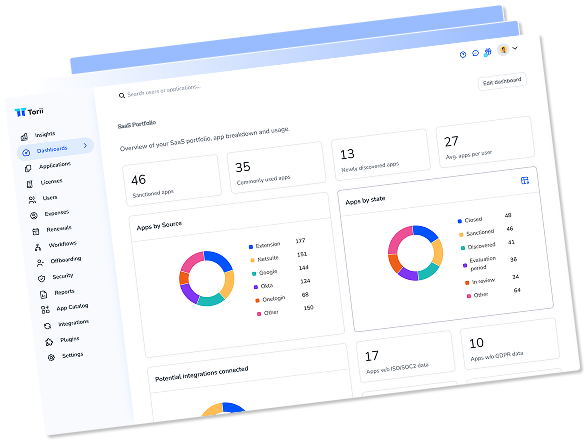
Torii
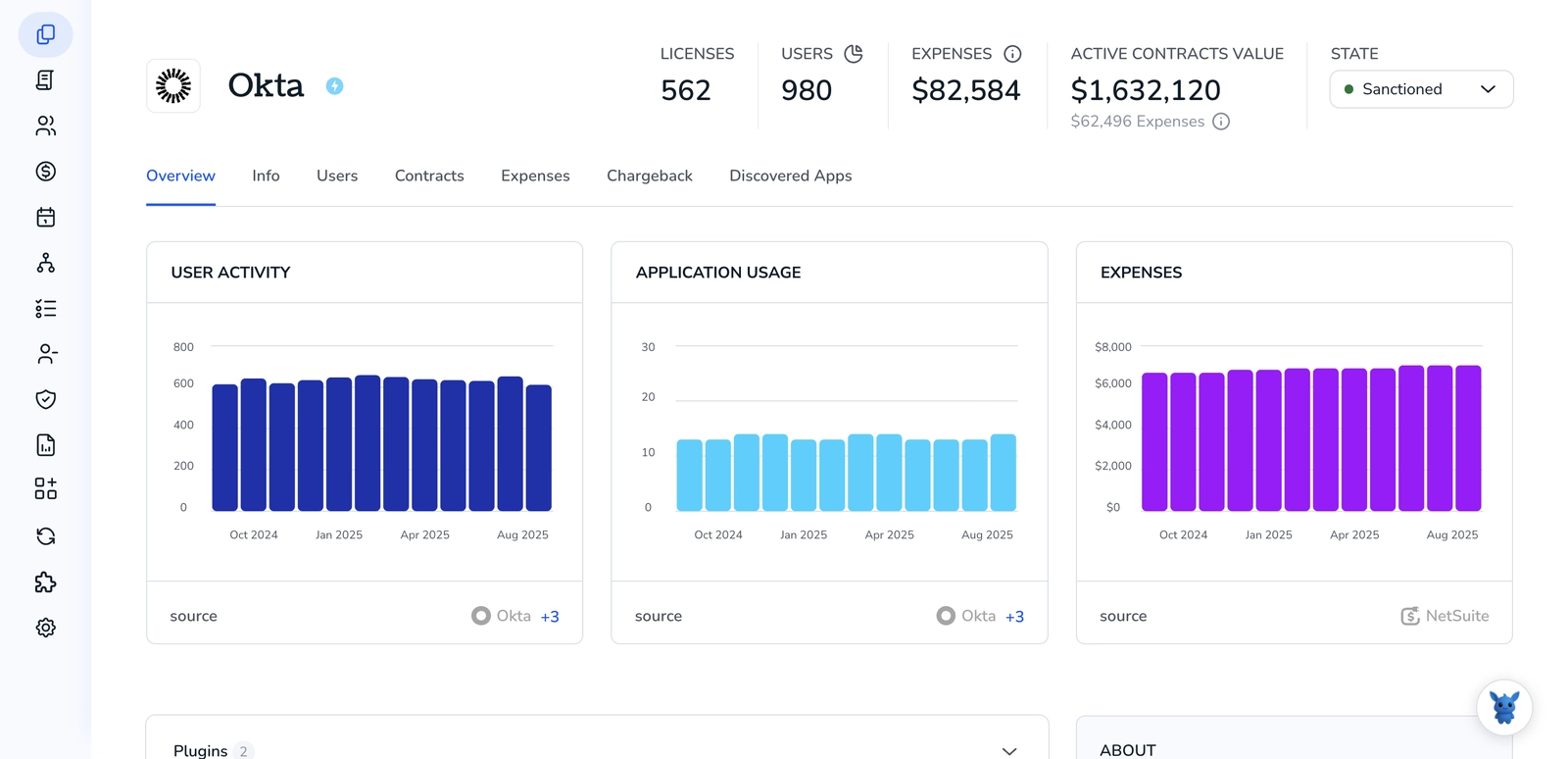
Torii connects directly to MongoDB and surfaces employee name and email, job title, department, user status, license data, and license types for every MongoDB user tied to an employee record. For IT and security teams running quarterly certification cycles, that gives reviewers an organized view of who holds Atlas roles without needing to export data from the MongoDB admin portal and reconcile it against an HR spreadsheet manually.
Where the integration adds practical value is in catching access drift. Employees who changed departments or job titles but kept their Atlas project roles are exactly the kind of issue quarterly audits are designed to surface. Torii flags those mismatches automatically. The integration also identifies accounts that exist in MongoDB but have no corresponding active HRIS record, which covers the orphaned account scenario common in databases where engineering teams provision access directly without routing it through IT.
Torii’s certification campaigns route review tasks to the correct owners automatically, with enough context built in that reviewers don’t need to track down background information separately. Every approval and revocation is logged with a timestamp, generating an audit trail that satisfies SOC 2 and ISO 27001 requirements. For organizations running MongoDB alongside a broader SaaS stack, Torii handles MongoDB reviews within the same platform managing Salesforce, Slack, and GitHub, which eliminates the overhead of running parallel governance programs. The platform holds the number-one spot in G2’s inaugural SaaS Management Platform Grid Report and is a 2025 Gartner Magic Quadrant Leader for SaaS Management Platforms.
Pros:
- Surfaces employee name/email, title, department, user status, and license data directly from MongoDB
- Flags accounts where Atlas roles don’t match current HR records or department assignments
- Routes certification tasks automatically with a complete, timestamped audit trail for SOC 2 and ISO 27001
- Manages MongoDB governance within the same workflow as the rest of the SaaS stack
Cons:
- Last-used date and historical usage data are not available from MongoDB through the integration
- Pricing reflects an enterprise-grade feature set, positioning it above entry-level options
| G2: 4.5/5 (302 reviews) | Capterra: 4.9/5 (26 reviews) |
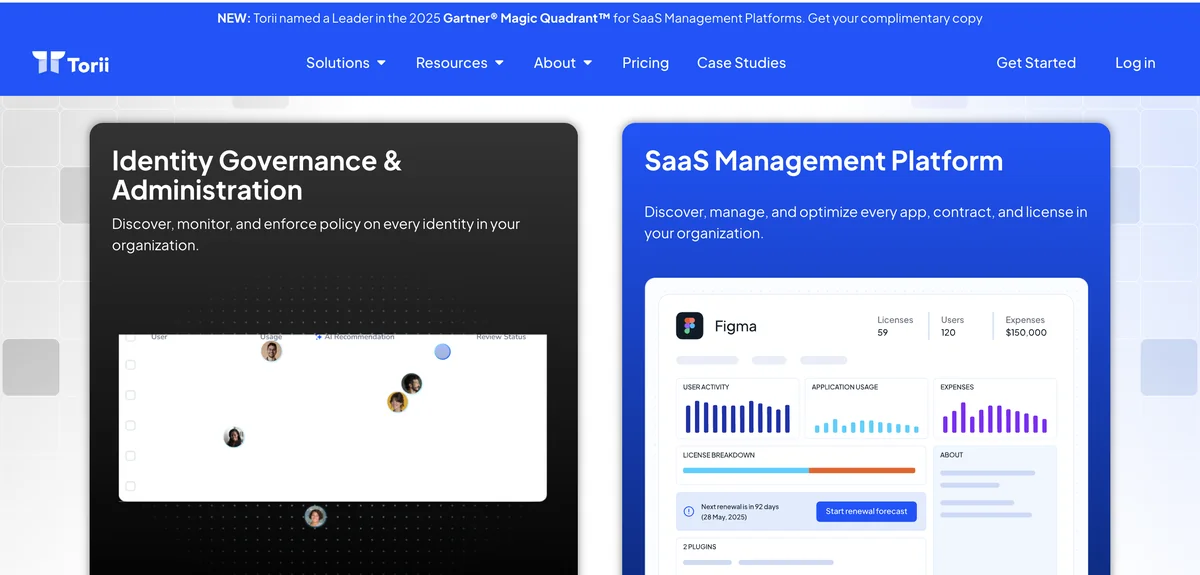
Veza
Veza’s Access Graph technology maps MongoDB permissions at the entitlement level rather than stopping at role labels. Instead of showing that a user holds the “dbAdmin” role, Veza translates that assignment into the actual CRUD operations it enables across specific databases and collections. For MongoDB environments where custom roles are stacked on top of built-in roles, that translation layer is meaningful: reviewers can see what a user can actually do rather than interpreting role names that don’t always communicate scope.
Veza also covers non-human identities, which matters specifically for MongoDB governance. Application service accounts, API keys, and connection string credentials carry real database privileges but rarely surface in standard access reviews tied to directory-connected employees. Veza’s discovery pulls those accounts into its graph alongside human users, so certification campaigns cover the full population rather than just the LDAP-integrated or SSO-managed accounts.
The platform is built for large enterprises, and pricing is not publicly disclosed. Veza has minimal public reviews (no G2 reviews, one Capterra review at the time of writing), though Gartner Peer Insights scores it 4.9 out of 5 from 29 verified reviews. The company was acquired by ServiceNow in December 2024, which could affect product direction over time. For security-first organizations that need permission-level MongoDB visibility above all else, Veza is one of the strongest options in the market.
Pros:
- Translates MongoDB role assignments into readable CRUD operations rather than role labels reviewers must interpret
- Covers service accounts and API keys in certification campaigns alongside human MongoDB users
- Risk-based sorting and toxic permission combination detection prioritize the highest-risk accounts first
Cons:
- No public pricing, no free trial—requires a sales conversation and is priced for large enterprises
- Minimal public reviews: 0 G2, 1 Capterra; Gartner Peer Insights shows 29 reviews at 4.9/5
- ServiceNow acquisition creates some product roadmap uncertainty going forward
| Capterra: 5.0/5 (1 review) | Gartner Peer Insights: 4.9/5 (29 reviews) |
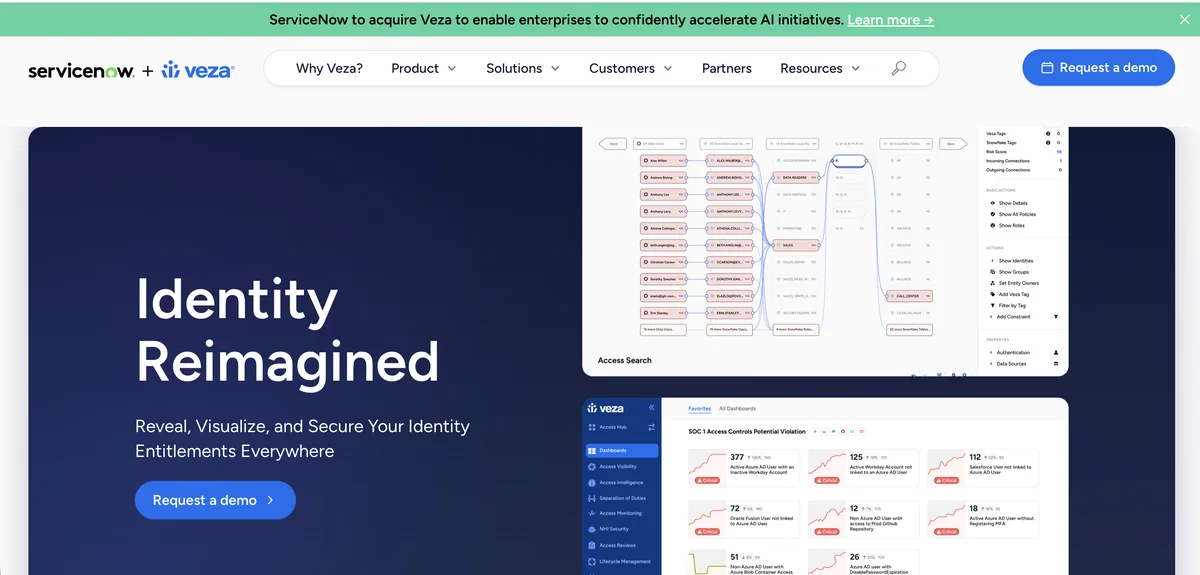
Nudge Security
Nudge Security approaches MongoDB access coverage from the discovery angle first. Its patented email-based detection finds MongoDB Atlas accounts created by employees across the organization, including shadow instances that IT may not have officially cataloged. For companies where developers spin up their own Atlas clusters for testing or side projects, that visibility is a prerequisite before any meaningful access review can begin.
Once accounts are discovered, Nudge Security’s automated playbooks categorize them and prompt users via Slack or email to confirm whether their MongoDB access is still needed. The platform reports an 83% compliance rate with its behavioral nudge approach, which outperforms block-and-ticket workflows that tend to generate support friction without consistently changing behavior. Nudge Security also tracks OAuth grants and service account connections tied to MongoDB, making it easier to understand what downstream systems are relying on a given user’s credentials before revoking access.
Nudge Security’s MongoDB capabilities center on discovery and lifecycle management rather than formal certification workflows. Structured campaigns with manager-facing review queues and the kind of attestation evidence that SOC 2 auditors typically require are not core features. For organizations whose primary MongoDB review concern is finding shadow access and handling departing employee offboarding, it’s a strong fit. Visit Nudge Security’s website to see the full capability set.
Pros:
- Email-based discovery finds shadow MongoDB Atlas instances and accounts not tracked in official IT inventories
- Nudge-driven compliance achieves high response rates without blocking user productivity or creating support queues
- Offboarding playbook covers MongoDB access deprovisioning as part of a complete cross-stack employee exit process
Cons:
- Structured access certification campaigns with manager review queues are not a primary feature
- Audit evidence generation is limited compared to dedicated IGA platforms, making it a weak fit for SOC 2 or ISO 27001
- Requires Google Workspace or Microsoft 365 as the email source; discovery doesn’t work without one of those platforms
Gartner Peer Insights: 4.7/5 (22 reviews)
Organizations using MongoDB Atlas with SSO enabled have a narrower review scope, since identity is managed at the IdP layer. Those running self-managed MongoDB clusters or using database-native user authentication face a broader challenge: user accounts live directly in the database, service accounts accumulate over time, and there's no central directory to query. Tools that can discover and certify both layers handle the full problem.
Okta Lifecycle Management
Okta Lifecycle Management governs MongoDB access primarily through its SCIM provisioning capabilities and Atlas’s native SSO and SAML integration. Organizations that have connected MongoDB Atlas to Okta as an identity provider can use OLM to manage org-level user provisioning and deprovisioning, ensuring that employees who leave the organization are removed from Atlas automatically based on Okta status changes rather than a manual IT ticket or a missed offboarding step.
For access certifications, Okta Identity Governance adds structured campaigns on top of the lifecycle layer. Teams can schedule recurring reviews of MongoDB Atlas users, route certification tasks to managers, and track campaign completion from a centralized dashboard. In 2025, Okta introduced Security Access Reviews with AI-generated summaries, which give reviewers contextual information about a user’s Atlas access during a certification rather than asking them to interpret raw role names they may not recognize.
Okta’s MongoDB coverage sits at the organization and project level. Collection-level access and service account governance within MongoDB require additional tooling, since the provisioning model works through the Atlas identity layer rather than reaching into database-native users and roles. The platform functions well when MongoDB Atlas is part of a broader Okta-managed SaaS portfolio and the primary concern is lifecycle automation during employee transitions. Learn more at Okta’s product page.
Pros:
- SCIM-based deprovisioning removes MongoDB Atlas users automatically when employee records change in Okta
- AI-generated access summaries (2025) give reviewers context during MongoDB certifications without requiring role expertise
- Handles MongoDB access reviews within the same certification workflow covering 7,000+ other integrated applications
Cons:
- Identity Governance features are bundled in the OIG tier, not available standalone, increasing cost for teams that only need certification
- MongoDB governance covers org and project roles; collection-level and database-native service account visibility requires additional tooling
- Initial configuration is complex and typically requires dedicated identity management expertise to get Atlas integration working correctly
| G2: 4.5/5 (1,257 reviews) | Capterra: 4.7/5 (914 reviews) |
SAP Cloud Identity Access Governance
SAP Cloud Identity Access Governance is built for enterprises where identity governance is tightly coupled to SAP business process compliance. Its SoD rulesets, certification workflows, and role optimization engine are designed around SAP SuccessFactors, S/4HANA Cloud, and Ariba. Connecting MongoDB to SAP IAG requires API-based integration and custom connector configuration rather than a turnkey setup, which adds to the already significant implementation investment.
For companies running SAP as their core ERP alongside MongoDB as a data layer or microservices backend, the platform offers one governance process spanning both environments simultaneously. Certification campaigns can cover SAP system access and MongoDB Atlas roles in the same pass, with automated escalations firing when reviewers miss deadlines and completion rates tracked through a centralized dashboard. The platform’s machine learning-based role design module also identifies over-provisioned access patterns across all connected systems, which can surface MongoDB users who accumulated database roles they no longer need.
Outside of SAP-centric enterprises, the cost and configuration overhead doesn’t justify the MongoDB governance value delivered. SAP IAG is public cloud only, carries enterprise pricing with no publicly disclosed rate card, and requires specialized SAP knowledge to operate certification campaigns at any depth. Check the SAP Cloud IAG product page for module details and trial access.
Pros:
- Unified access reviews spanning SAP application environments and MongoDB in the same certification campaign
- Machine learning role optimization identifies over-provisioned access patterns across all connected systems
- Continuous SoD monitoring catches cross-system policy violations in real time rather than at campaign intervals
Cons:
- MongoDB connector requires custom API configuration rather than turnkey setup, adding to implementation timeline
- Enterprise-only pricing with no public rate card and limited trial access beyond a 50-user BTP sandbox
- Requires specialized SAP expertise to run campaigns effectively; configuration complexity is high for non-SAP teams
| G2: 3.0/5 (limited reviews) | Gartner Peer Insights: 4.4/5 (114 reviews) |
Oracle Identity Governance

Oracle Identity Governance connects to MongoDB through REST APIs and custom connectors, pulling user account data into OIG’s certification campaigns. Its event-based micro-certification feature is one of the more useful capabilities for MongoDB environments with active developer populations: access reviews can trigger automatically when an employee changes roles or departments rather than waiting for the next scheduled campaign cycle. For teams where developer job changes are common, that responsiveness shrinks the gap between a permission change and the next attestation check.
OIG’s AI layer compares MongoDB users against peer groups during campaigns and surfaces outliers for closer reviewer attention. A developer holding read access across eight databases that none of their peers touch will appear flagged without a reviewer having to manually hunt for the anomaly. For Oracle shops running MongoDB alongside Oracle databases or Fusion Applications, OIG can run a unified certification covering both environments from a single platform rather than requiring separate governance processes for each system.
The practical barrier for most teams is cost and implementation complexity. Oracle OIG licensing starts at $3,600 per named user or $180,000 per processor, and implementation typically takes several months with custom development work required for the MongoDB connector. G2 rates ease of setup at 6.1 out of 10. Visit Oracle Identity Governance’s product page to understand full licensing options before building a business case.
Pros:
- Event-based micro-certifications trigger MongoDB access reviews automatically when job codes or departments change
- Peer group analysis flags MongoDB users with unusual role assignments compared to colleagues in similar positions
- Unified reviews across MongoDB and Oracle environments make sense for Oracle-centric enterprises already running OIG
Cons:
- Licensing starts at $3,600 per named user, making it cost-prohibitive outside existing Oracle deployments
- MongoDB connector requires custom development work that extends an already-long implementation timeline
- G2 ease-of-setup score of 6.1 out of 10, with reviewers noting the UI hasn’t substantially changed in five years
| G2: 3.8/5 (71 reviews) | Capterra: 4.4/5 (7 reviews) |
Avatier

Avatier supports MongoDB governance through its containerized identity platform and 90+ pre-built application connectors. Its delta certification approach is distinctive for MongoDB environments where access changes frequently: rather than running a full quarterly review of every MongoDB user and role assignment, Avatier scopes subsequent certifications to only the accounts and permissions that changed since the last audit. For Atlas deployments with hundreds of users across dozens of databases, that scoping keeps campaigns manageable without gaps in coverage.
Review tasks reach managers through Teams, Outlook, Slack, or mobile notifications rather than requiring login to a separate portal. Avatier’s automated escalation workflows keep campaign completion rates up without IT manually chasing reviewers, and its AI-powered access pattern analysis flags accounts showing unusual MongoDB usage for prioritized attention. The platform also handles orphaned account detection and automated access revocation, which is particularly relevant for MongoDB environments where service accounts accumulate over time without a consistent cleanup process.
Avatier’s all-in-one approach combines IGA, SSO, password management, and lifecycle automation in a single platform. Pricing runs $1.50 to $5.00 per user per month, with a fixed-bid implementation option that eliminates the surprise professional services costs common with enterprise IGA vendors. G2 rates the platform 4.6 out of 5, and the company reports a 97% customer satisfaction rate across a customer base spanning healthcare, financial services, and government sectors.
Pros:
- Delta certification reviews only changed MongoDB accounts since the last audit, making campaigns significantly shorter
- Multi-channel review notifications (Teams, Slack, Outlook, mobile) improve manager participation rates during campaigns
- All-in-one platform avoids the need for separate SSO, IGA, and password management tools across the identity stack
Cons:
- Smaller market presence means fewer community resources and less third-party validation than Okta or SailPoint
- Native reporting customization options are more limited than enterprise IGA platforms with advanced query tools
- Not included in Gartner Magic Quadrant or Forrester Wave, which can create procurement friction in analyst-validation-required organizations
G2: 4.6/5 (31 reviews)
How to Choose a MongoDB Access Review Tool
The decision comes down to three factors: the scale of your MongoDB deployment, the compliance requirements driving the review, and how MongoDB fits into the rest of your environment.
If your review covers Atlas SSO-managed users at the org and project level, SaaS governance platforms like Torii and Okta handle it well without requiring dedicated IGA infrastructure. If your scope extends to database-native users, custom role hierarchies, service accounts, and collection-level permissions, you need a platform with deeper data layer visibility—either a purpose-built IGA tool or something like Veza that maps entitlements rather than stopping at role labels.
Full-scale IGA platforms like Oracle OIG and SAP Cloud IAG are best suited to enterprises where MongoDB is one component of a governed application landscape that already includes those vendors’ ecosystems. Both bring deep certification workflows and SoD enforcement, but neither deploys quickly or cheaply, and MongoDB governance is not what either was originally designed for.
Veza fills a specific need: organizations that need to understand what MongoDB users can actually do in the database, not just what role they hold. That permission-level visibility matters in data-sensitive environments with complex nested role structures. Nudge Security addresses a different gap, specifically the discovery problem, and works well for teams whose MongoDB review challenge starts with shadow Atlas instances they don’t know exist.
Torii makes sense when MongoDB access reviews need to happen alongside the rest of the SaaS stack rather than as a standalone program. Its combination of AI-enabled automation, shadow IT discovery, SaaS financial governance, and automated license remediation means MongoDB governance doesn’t require a separate workflow or tool. For mid-market organizations running MongoDB Atlas alongside dozens of other applications, consolidating that governance into one platform tends to reduce both cost and operational overhead more than running separate point solutions for each system.
Avatier is a competitive alternative for teams that prioritize lower total cost of ownership and faster deployment over analyst recognition and brand familiarity, and its delta certification model is genuinely useful for MongoDB environments where access changes frequently.
Frequently Asked Questions
MongoDB Atlas access controls are highly granular: projects can contain dozens of users with built-in roles assigned at database or collection level, plus service accounts, connection strings, and API keys. That granularity multiplies as headcount or organizational structures change, complicating reviews.
Access reviews typically cover Atlas organization and project roles, database-level user accounts and built-in role assignments, collection-level permissions for sensitive data, service accounts and API keys used by applications, LDAP-integrated users, and orphaned accounts after role transitions.
Nudge Security uses patented email-based scanning to find shadow Atlas instances and accounts, while Torii reconciles Atlas users against HR records to surface orphaned accounts and department mismatches before formal certification campaigns begin.
Veza maps MongoDB permissions at the entitlement level, translating role labels into actual CRUD operations a user can perform across databases and collections. It also surfaces non-human identities—service accounts, API keys, and connection strings—so certifications cover actionable privileges.
Torii pulls employee name, email, title, department, and license data from MongoDB, flags role-to-HR mismatches, identifies orphaned accounts, routes certification tasks automatically, and logs every approval or revocation with timestamps to produce a SOC 2 and ISO 27001-ready audit trail.
Choose based on scale, compliance requirements, and scope of MongoDB access. Use SaaS governance (Torii, Okta) for org/project-level reviews; Veza or IGA platforms for entitlement and collection-level visibility; and Nudge Security for shadow-instance discovery and lightweight remediation.