Top 8 JumpCloud Access Review Solutions in 2026

JumpCloud manages directory services for more than 200,000 organizations, handling authentication, device binding, group-based app access, and LDAP/RADIUS connectivity from a single cloud platform. That scope means a JumpCloud access review isn’t just checking who can log into a single app. It covers which users hold admin roles across five permission tiers, which groups grant access to dozens of bound applications, and whether former employees still have active directory accounts anywhere in the chain.
JumpCloud’s native Directory Insights tool tracks more than 120 event types and lets admins export point-in-time permission reports. What it doesn’t provide is a campaign workflow: no scheduled certifications, no routing review tasks to managers, no structured audit trail built for compliance evidence. That gap is where third-party tools become necessary.
Admin role assignments (five tiers from Read Only to Administrator with Billing), user group memberships and the SSO apps, devices, and RADIUS networks they unlock, stale or orphaned accounts from departed employees, and privileged access stored in JumpCloud's PAM vault. Most teams also audit dynamic group rules to verify that auto-assigned memberships still reflect current job scope.
This comparison covers eight tools for running structured JumpCloud access reviews in 2026. Each takes a different approach to the problem, ranging from SaaS governance platforms to full-scale enterprise IGA solutions.
★ = low · ★★ = medium · ★★★ = high
| Tool | Ease | Cost | AI Capabilities | Reviews |
|---|---|---|---|---|
| Torii | ★★★ | ★★ | ★★★ | ★★★ |
| SAP Cloud IAG | ★ | ★ | ★★ | ★★ |
| SailPoint IdentityIQ | ★★ | ★ | ★★★ | ★★ |
| One Identity | ★ | ★★ | ★★ | ★★ |
| Oracle Identity Governance | ★ | ★ | ★★ | ★★ |
| Saviynt | ★★ | ★ | ★★★ | ★★ |
| MiniOrange | ★★★ | ★★★ | ★ | ★ |
| CloudEagle | ★★ | ★★ | ★★ | ★★ |
Table of Contents
- Torii
- SAP Cloud Identity Access Governance
- SailPoint IdentityIQ
- One Identity
- Oracle Identity Governance
- Saviynt
- MiniOrange
- CloudEagle
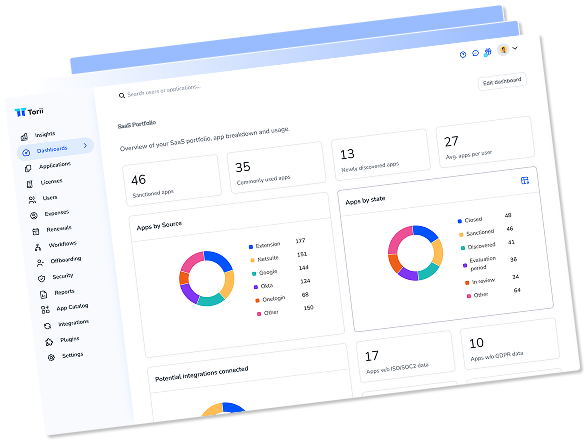
Torii
JumpCloud’s group-based access model gives Torii a lot of structure to work with. Torii connects directly to JumpCloud and surfaces employee name and email, title, department, user status, license data, license types, and historical usage patterns across the directory. That gives reviewers an immediate, organized view of who has what access without needing to run manual exports from JumpCloud’s admin portal.
Where Torii adds meaningful value beyond basic visibility is in cross-system correlation. It identifies accounts that exist in JumpCloud but have no matching record in your HRIS, flags users whose group memberships don’t align with their department or title, and surfaces licenses sitting on accounts with no documented activity. That kind of reconciliation normally takes hours to build in a spreadsheet.
Torii’s access review campaigns route tasks to the correct owners automatically, with enough context so reviewers don’t need to dig for information. Every approval and revocation is logged with a timestamp, creating an audit trail that holds up to SOC 2 and ISO 27001 requirements. For organizations running JumpCloud alongside a broader SaaS stack, Torii handles JumpCloud access reviews within the same platform used for Slack, GitHub, and every other connected app, which eliminates the overhead of running parallel governance processes.
Pros:
- Surfaces employee name/email, title, department, user status, license data, and historical usage directly from JumpCloud
- Automatically flags accounts with group memberships that don’t match HR records or role context
- Routes access review tasks to correct owners with built-in audit trail documentation
- Combines SaaS management and identity governance, so JumpCloud reviews happen alongside the rest of the stack
Cons:
- Last-used date is not available for JumpCloud, limiting activity-based filtering in access campaigns
- Pricing is above entry-level options, making it less suitable for very small teams
| G2: 4.5/5 (302 reviews) | Capterra: 4.9/5 (26 reviews) |
SAP Cloud Identity Access Governance
SAP Cloud Identity Access Governance is designed for enterprises where identity governance is tightly coupled to SAP business process controls. It connects to JumpCloud through SCIM-based federation and SAML integration, which allows JumpCloud user data to be pulled into SAP IAG’s certification campaigns alongside identities from SAP SuccessFactors, S/4HANA Cloud, and Ariba.
Organizations running JumpCloud alongside a major SAP environment get one practical benefit from SAP IAG: a single certification campaign spanning both the directory layer and the SAP application layer at once. Campaign dashboards track completion rates in real time, automated escalations fire when reviewers miss deadlines, and the platform’s SoD ruleset catches access conflicts across JumpCloud and SAP systems in the same pass.
SAP IAG’s strength is the SAP ecosystem, and the tool is a poor match outside that context. Organizations using JumpCloud without deep SAP dependencies will find significant configuration overhead for relatively modest governance benefit. The platform is public cloud only, carries enterprise pricing, and requires specialized SAP knowledge to operate effectively. You can find out more about SAP Cloud IAG at their product page.
Pros:
- Consolidates JumpCloud and SAP system reviews in unified campaigns, reducing process fragmentation
- Hybrid bridge capability allows governance to span on-premise SAP GRC and cloud deployments simultaneously
- Machine learning-based role optimization helps clean up over-provisioned access across connected systems
Cons:
- Purpose-built for SAP environments; limited governance value for non-SAP organizations
- Complex to configure and maintain, requiring specialized SAP expertise
- Enterprise pricing with no publicly disclosed rates, typically excluding mid-market budgets
G2: 3.0/5 (limited reviews)
SailPoint IdentityIQ
SailPoint connects to JumpCloud through its connector framework, pulling user accounts, group memberships, and role assignments into access views that feed certification campaigns. Its peer group analysis compares each JumpCloud user’s profile against others in similar roles and flags accounts with group bindings or admin role assignments that deviate from the norm.
AI-driven certification recommendations appear as thumbs-up or thumbs-down icons for each access item during a campaign. For JumpCloud environments with a large number of groups and SSO app bindings, those recommendations make a real difference in reviewer fatigue. Instead of processing every line item from scratch, managers can focus attention on the flagged outliers rather than rubber-stamping the whole list.
Deployment timelines and pricing create real barriers for mid-market JumpCloud teams considering SailPoint. Implementations typically take six to twelve months and require significant professional services involvement. Entry pricing starts at $75,000 annually, and professional services often match or exceed the software cost. For mid-market organizations using JumpCloud without a dedicated IAM team, that investment is hard to justify compared to faster, lighter alternatives. SailPoint IdentityIQ is built for large enterprises with complex compliance requirements, and the deployment experience reflects that.
Pros:
- Peer group analysis flags JumpCloud accounts with unusual group bindings or admin role assignments
- AI certification recommendations reduce reviewer fatigue during large campaigns
- 1,100+ enterprise connectors enable governance across JumpCloud alongside every other system in the environment
- Deep SoD controls (up to 500 policies) provide enterprise-grade compliance enforcement
Cons:
- Implementation takes six to twelve months with significant professional services cost
- Minimum annual commitment of $75,000 excludes most mid-market JumpCloud customers
- Steep learning curve, with reviewers noting administrators need weeks of training before system access
| G2: 4.5/5 (161 reviews) | Capterra: 4.2/5 (21 reviews) |
One Identity
One Identity Manager governs JumpCloud environments through Starling Connect, a SCIM 2.0 component that pulls user and group data into its identity model. Once connected, attestation policies define which JumpCloud accounts get reviewed, how often, and by whom, with a complete audit trail generated at each step of the certification process.
The platform suits organizations running JumpCloud as a cloud directory alongside Active Directory on-premise. JumpCloud and AD often co-exist during infrastructure migrations, and One Identity’s deep AD heritage means it can run access reviews across both sources without requiring separate tools for each. Its unified IGA and PAM capabilities also cover privileged access stored in JumpCloud’s vault, which most SaaS-native platforms don’t address.
One Identity’s cost profile sits below SailPoint’s, with median annual contracts around $31,000 and volume discounts for larger deployments. The trade-off is user experience: multiple Gartner reviews describe the access certification interface as dated and difficult for business users to navigate, which can hurt campaign completion rates when certifications go to non-technical managers. Visit One Identity for current pricing and deployment options.
Pros:
- SCIM 2.0 connection to JumpCloud with structured attestation policy framework
- Strong hybrid environment support, covering JumpCloud and Active Directory in combined campaigns
- More cost-effective than SailPoint for comparable governance capabilities
Cons:
- Access certification UX is described as dated in multiple Gartner reviews, affecting business user adoption
- Implementation requires a partner and typically takes weeks to months
- Earlier connector versions showed gaps in Microsoft Entra ID support that complicate JumpCloud-to-Azure migration scenarios
| G2: 3.5/5 (limited reviews) | Capterra: 5.0/5 (2 reviews) |
Oracle Identity Governance

Oracle Identity Governance connects to JumpCloud through REST APIs and third-party connectors, bringing directory user data into OIG’s certification campaigns. One of its stronger features for JumpCloud governance is event-based micro-certification: access reviews can trigger automatically when a user’s department, job code, or org structure changes, rather than waiting for the next quarterly campaign cycle. That shrinks the window between a role change and the next certification check.
OIG’s AI layer surfaces recommendations during campaigns, comparing each user against peer groups and prioritizing outliers for closer attention. For organizations managing JumpCloud alongside Oracle Fusion, EBS, or Oracle databases, this unified review approach covers the directory layer and the application layer together.
Outside of Oracle-heavy environments, the cost-to-benefit ratio for JumpCloud governance gets difficult to justify. Licensing starts at $3,600 per named user or $180,000 per processor, implementation is measured in months, and G2 rates ease of setup at 6.1 out of 10. Reviewers note the UI hasn’t changed significantly in five years. The Oracle Identity Governance platform is a strong fit for Oracle shops but a costly choice for organizations that simply need JumpCloud directory governance.
Pros:
- Event-based micro-certifications trigger access reviews automatically on department or role changes
- Deep integration with Oracle’s application suite enables unified reviews across directory and app layers
Cons:
- Licensing starts at $3,600 per named user, making it prohibitively expensive outside Oracle environments
- G2 ease of setup score of 6.1/10 and multiple reviews citing implementation complexity
- Product innovation described as slow by reviewers, with minimal changes outside the GUI in recent years
| G2: 3.8/5 (71 reviews) | Capterra: 4.4/5 (7 reviews) |
JumpCloud's GBAC model means a single group membership can simultaneously unlock SSO apps, RADIUS networks, LDAP access, and device bindings. Reviewers often find that users accumulate group memberships through project assignments and role changes without a removal process in place, creating the kind of stale access that compliance audits surface. Third-party tools that can query JumpCloud's group model directly tend to catch this faster than export-based approaches.
Saviynt
Saviynt connects to JumpCloud through SCIM integration, pulling user accounts, group memberships, and admin role assignments into its identity model for access certification. Its AI-powered Trust Scoring feature handles low-risk approval decisions automatically, which the company reports can reduce reviewer workload by as much as 75% during large campaigns. For JumpCloud environments with hundreds of users across dozens of groups, that kind of automation keeps certification campaigns from becoming a months-long manual slog.
JumpCloud group memberships shift frequently, and that’s where Saviynt’s continuous compliance model makes a practical difference. Saviynt monitors access in real time and triggers micro-certifications when significant changes occur, like a user being added to a group that grants admin-level application access through bound SSO connectors, rather than waiting for the next quarterly campaign to surface it.
Saviynt holds the highest percentage of 5-star reviews in the IGA category across Gartner, with 85% of 185 reviewers giving it five stars and four consecutive Customers’ Choice recognitions. Pricing starts above $10,000 annually, and implementation carries real complexity. Learn more at Saviynt’s website.
Pros:
- Trust Scoring automates low-risk JumpCloud access decisions, reducing reviewer workload by up to 75%
- Continuous compliance monitoring triggers micro-certifications on group membership changes rather than waiting for campaigns
- Four consecutive Gartner Customers’ Choice recognitions for IGA with 85% five-star review rate
- Mobile certification experience supports on-the-go reviews, which improves manager participation rates
Cons:
- Starting price above $10,000 annually, with total cost significantly higher once implementation is included
- Mixed customer support reviews, with some users reporting slow ticket resolution for complex issues
| G2: 3.5/5 (limited reviews) | Capterra: 4.5/5 (2 reviews) |
MiniOrange

MiniOrange treats JumpCloud as an identity source and IdP for SSO, layering structured access request workflows and compliance reporting over it. Teams already running JumpCloud can add governance coverage where the native Directory Insights tool leaves off, without switching to a full IGA platform. Its SCIM provisioning syncs user status between JumpCloud and connected applications, keeping downstream access current when accounts are deprovisioned in the directory.
Its access governance automation runs through Jira Service Management, which makes it a practical fit for organizations already using Jira. Users submit access requests through the Jira portal, automated routing assigns approvals to the right manager or project lead, and every action is logged with enough detail to satisfy SOX, HIPAA, and ISO 27001 audit requirements.
At $2-$3 per user per month, MiniOrange is among the most affordable options in this comparison. The trade-off is depth: native access certification campaigns with manager-facing review queues are limited compared to dedicated IGA platforms, and reviewers note that support quality can vary significantly. It’s a practical option for smaller teams that need basic governance structure without enterprise platform complexity.
Pros:
- $2-$3 per user per month, significantly below enterprise IGA pricing
- Jira-based workflow automation fits teams already using Jira Service Management for IT requests
- SCIM provisioning keeps JumpCloud and connected app access synchronized during employee lifecycle events
Cons:
- Native access certification campaign tooling is limited compared to dedicated IGA platforms
- Support quality is inconsistent, with some users reporting difficulty getting issues resolved
- Access governance automation requires Jira, creating a tool dependency that not all organizations have
| G2: 4.5/5 (264+ reviews) | Capterra: 4.5/5 (36 reviews) |
CloudEagle
CloudEagle connects to JumpCloud through SSO and identity provider integrations, drawing from it to build a cross-stack view of user access. When JumpCloud is the central directory, CloudEagle cross-references identity data against actual SaaS app usage, flagging accounts where access provisioned through JumpCloud’s SSO connectors doesn’t match real-world activity.
Access review campaigns in CloudEagle are built around Slack-native workflows. Reviewers get notifications and can approve or revoke access without leaving the messaging app. The platform reports an 80% reduction in review time, backed by case studies from RingCentral (3x ROI) and ICEYE (5x ROI). Compliance documentation is generated automatically, with one customer completing a full SOC 2 prep in 72 hours.
CloudEagle sits closer to the SaaS management side of the market than pure IGA. Its strength is uncovering shadow IT, tracking license spend, and running SaaS access reviews at speed. Directory-level governance covering JumpCloud admin roles, device bindings, and LDAP/RADIUS access is shallower than what dedicated identity platforms provide. For orgs whose JumpCloud review scope is primarily SaaS app access and user lifecycle, that trade-off works. Visit CloudEagle to see the full integration list.
Pros:
- Slack-native review workflows improve campaign completion rates by keeping approvals in the tools managers already use
- 500+ direct integrations, ranked in Gartner’s top tier for SaaS management platform connectivity
- Continuous shadow IT detection surfaces JumpCloud-connected app access that may not be tracked elsewhere
Cons:
- Directory-level governance (admin roles, device bindings, RADIUS access) is shallower than dedicated IGA tools
- No API access for custom integrations or reporting, limiting extensibility for complex environments
- Some users report integration inconsistencies requiring manual intervention when automated workflows break
G2: 4.7/5 (150+ reviews)
How to Choose a JumpCloud Access Review Tool
The decision largely comes down to which part of JumpCloud you need to govern and what the rest of your environment looks like.
If your review scope centers on SaaS app access provisioned through JumpCloud's SSO bindings, lighter platforms like Torii and CloudEagle get you there faster. If your scope extends to LDAP, RADIUS, device management, and privileged access governance across a hybrid environment, you'll need an IGA platform with deeper directory coverage.
Full-scale IGA platforms like SailPoint and Saviynt fit best when JumpCloud is one directory among many in a large, compliance-heavy enterprise. They deliver deep certification workflows, SoD enforcement, and structured audit documentation across all identity sources. The trade-off is deployment time, cost, and the need for dedicated IAM resources to maintain the configuration.
Cloud-first environments where JumpCloud is the primary directory tend to be better matched with Torii or CloudEagle. Torii is specifically useful when shadow IT discovery, AI-enabled automation, SaaS financial governance, and access certification all need to happen in one platform rather than separate tools. Combining license optimization with identity governance reduces the administrative overhead of running two parallel programs, which is where Torii tends to stand out.
SAP IAG and Oracle OIG are strong picks only when those vendors are already central to the application environment. Their JumpCloud governance is functional but comes packaged with significant ecosystem dependency and premium pricing that makes little sense outside an SAP or Oracle shop.
For smaller teams working within a tight budget, MiniOrange offers access governance structure at a fraction of enterprise pricing. Organizations expecting full certification campaign functionality with manager-facing review queues should evaluate the depth of those features carefully during a trial before committing.
Frequently Asked Questions
A JumpCloud access review checks admin role assignments across five tiers, group memberships that grant SSO apps, devices, LDAP/RADIUS access, stale or orphaned accounts, privileged entries in JumpCloud's PAM vault, and dynamic group rules that auto-assign memberships.
JumpCloud's Directory Insights provides event tracking and point-in-time reports but lacks campaign workflows: no scheduled certifications, manager routing, or compliance-ready audit trails, so third-party tools add automation, routing, and persistent evidence for audits.
Match tool to scope and environment: choose Torii or CloudEagle for SaaS-centric JumpCloud governance, MiniOrange for tight budgets, and full IGA platforms like SailPoint or Saviynt when you need deep LDAP/RADIUS, privileged access, SoD controls, and enterprise-scale compliance.
Torii pulls JumpCloud user, license, and group data, correlates with HRIS to flag mismatches, routes review tasks to owners with timestamped audit trails, and consolidates SaaS management and identity governance for faster, unified access reviews.
Full-scale IGA platforms provide deep certification workflows, extensive SoD controls, AI-driven recommendations, continuous compliance, and broad connector coverage—ideal when JumpCloud is one of many identity sources and your organization requires rigorous audit evidence despite higher cost and longer deployments.
JumpCloud's group-based access model can let a single membership grant SSO apps, RADIUS, LDAP, and device access. Memberships accumulate through role changes, creating stale or orphaned access; direct group-model queries from third-party tools catch sprawl faster than export-based audits.